Subscribe to AIR Release Notes
Trusted by Organizations Worldwide
AIR v5.17
29 April 2026
Feature
The release of Binalyze AIR v5.17 delivers key enhancements that improve investigation workflows and policy management, enabling security analysts to work faster and more precisely. New features focus on structured data analysis, policy cloning, and bulk allow-list imports to streamline response actions and handle large-scale environments effectively.
What is new?
-
Structured Data Viewer for JSON, XML, and YAML: AIR automatically identifies structured content within evidence and opens it in a dedicated viewer, allowing analysts to collapse, search, and format data for clearer insight into complex artifacts such as system logs or Tornado data.
-
Policy Cloning: Users can duplicate existing isolation or acquisition policies, reducing setup time and configuration errors when standardizing response templates across organizations.
-
Bulk Import for Isolation Policy Allow Lists: Analysts can import IP/Port or process allow lists in bulk through text or CSV input, enabling rapid creation of large-scale isolation rules.
The Investigation Hub now includes a read-only structured data viewer supporting JSON, XML, and YAML, improving readability and forensic-level clarity on parsed artifact sources without external extraction. Enhancements in user visibility provide sortable “Created” and “Last Active” fields to help track authentication and active use for audit and compliance purposes. Syslog forwarding configuration applies dynamically, ensuring uninterrupted log integration during active investigations.
Policy management benefits from duplication capabilities that prefill cloned policies for quick adjustment, streamlining policy replication across complex enterprise environments. Isolation policies support bulk allow-list import, with automated validation, and now include process and domain-based entries, improving cross-platform containment precision.
Asset list rendering is optimized for environments with hundreds of online assets, stabilizing tag updates, search, and filtering through background polling. Task management introduces creation date filters to aid incident correlation and post-incident reviews. DRONE analyzer toggles now synchronize global and individual settings for clearer task configuration.
Responder-side improvements include safer handling of decimal disk space inputs during acquisition tasks and clearer failure feedback when partial evidence collection occurs. Updated macOS deployment instructions emphasize filename consistency to prevent installation issues in secure environments.
Investigation management export performance is significantly enhanced by caching and query optimizations, accelerating large-scale CSV exports from the Investigation Hub to support fast evidence correlation across extensive asset sets.
Notable bug fixes address evidence repository validation logic during interACT tasks, stabilize asset polling and UI selections in large environments, and ensure immediate application of syslog configuration changes without console restarts. DRONE analyzer toggling now reflects individual analyzer states correctly, decimal disk space entries are standardized, and Windows DNS evidence collection returns accurate results. User interface corrections improve search and column persistence, and task status messaging better differentiates partial from full acquisition failures to reduce investigator confusion.
Click here for more detailsAIR v5.16
15 April 2026
Feature
The release of Binalyze AIR v5.16 delivers key enhancements designed to improve investigation workflows for cybersecurity and security operations teams. This update expands evidence coverage across Windows environments, enhances file analysis capabilities for XFS partitions, and strengthens responder–console communication reliability to support large-scale distributed investigations.
What is new?
-
AIR File Explorer XFS Partition Support: Added support for recognizing and parsing XFS partitions in disk images. Analysts can now browse and analyze evidence from XFS-based assets directly within AIR File Explorer.
-
Expanded Windows evidence coverage in Baseline Comparison: Baseline Comparison supports over 40 new Windows artifact sources, including file system, registry, system, network, and SRUM data, enabling deeper and broader comparative analysis. macOS artifact mappings were refined for improved consistency.
-
Enhanced RelayPro: Upgraded RelayPro with a new toolchain and improved dependencies, enhancing responder–console communication security and reliability for uninterrupted evidence transfers during complex investigations.
This release significantly broadens Baseline Comparison’s visibility by incorporating new Windows artifact sources such as crash dumps, recycle bin contents, system restore points, shell bags, LNK files, and jump lists. Registry artifacts including AppCompatCache, UserAssist, and MRU lists are now included, alongside expanded system, network, and SRUM-based usage data. These additions empower investigation teams to perform more comprehensive change and activity analysis across their assets.
Improvements to AIR File Explorer enable full disk images containing XFS partitions to open with correct file type recognition. This enhancement resolves previous limitations in analyzing evidence stored on XFS-based storage, accelerating file triage and validation within investigations.
RelayPro’s communication stack was updated to strengthen encryption and enhance failover handling, leading to more secure and reliable sessions during live-response operations. Network optimizations reduce redundant HTTP requests by suppressing duplicate status reports and disabling unnecessary retries on permanent errors. These enhancements reduce network overhead and improve responder connectivity, especially in distributed and restricted network environments.
Additional bug fixes address task status inconsistencies in Cases, proxy configuration application across external services, reliability of Investigation Hub report generation, acquisition task report loading issues, and improved integrity in Chrome History data collection. Together, these fixes increase overall platform stability and user confidence in investigation workflows.
Click here for more detailsAIR v5.15.3
02 April 2026
Hotfix
Bug Fix
Responder stability improvement during service shutdown: Resolved an issue introduced in a previous release (v5.13) where stopping the Responder service caused unexpected termination. This fix restores proper service stop behavior and ensures ongoing evidence collection or analysis tasks complete gracefully without data loss or interruption.
AIR v5.15
01 April 2026
Feature
The release of Binalyze AIR v5.15 delivers key enhancements and fixes that improve investigation workflows and operational continuity for cybersecurity and investigation teams. This release advances session visibility, expands asset management capabilities, and introduces a universal trusted certificate store—critical improvements for efficient, integrity-preserving incident response.
What is new?
-
Enhanced interACT Session Visibility: When reviewing historical interACT sessions, the session header now shows the specific task name, enabling analysts to quickly identify and navigate between concurrent live-response sessions. This improves investigation context and analyst efficiency.
The v5.15 update introduces an Independent Universal Trusted Certificate Store within AIR Console, allowing secure management of Trusted Certificate Authorities outside proxy configurations. This enhancement supports organizations with strict SSL inspection policies and self-signed certificates, ensuring forensically sound authentication and uninterrupted licensing and update services in high-security environments.
Asset management sees improvements with the addition of the Registered At field in Advanced Filters, empowering analysts to filter assets by registration timestamp for targeted, time-scoped investigations. Moreover, auto asset tag search now extends to tag content, facilitating faster triage and correlation across rich tagging datasets.
This release addresses multiple critical bug fixes, including improved stability and handling for large dataset uploads, reliable Windows volume imaging, resolution of authorization errors post-upgrade, and enhanced AWS integration scans. Performance optimizations in audit log search and pagination reduce latency in large environments, while improved feedback during responder unisolation clarifies operational status.
The Binalyze MITRE ATT&CK Analyzer advances to version 13.0.1, adding Microsoft 365 detection enhancements to identify unauthorized administrative configuration changes and correlating suspicious activity such as brute-force logins and permission changes. Sigma rule integrations have been updated with the latest rules for comprehensive endpoint and cloud analysis. Additionally, YARA-based detection signatures for Covenant C2 activities strengthen early adversary infrastructure identification.
Full details follow below. Binalyze AIR v5.15 Release Notes
Click here for more detailsAIR v5.14
17 March 2026
Feature
The release of Binalyze AIR v5.14 introduces key enhancements designed to improve incident response workflows and investigation management. This update strengthens rule governance with Git-managed triage, refines SIEM integration through customizable syslog filtering, and delivers important improvements across responder reliability, and network isolation. These updates enable cybersecurity and investigation teams to achieve more consistent, traceable, and focused analyses across assets.
What is new?
-
Git-Managed Triage Rules: Security and investigation teams can now connect their organization’s Git repositories (GitHub, GitLab, Azure DevOps, or Bitbucket) directly to AIR to manage YARA, Sigma, and osquery triage rules as their single source of truth. This integration supports webhook-based synchronization, secure token handling, and ownership modes such as Mirror or Fork, ensuring consistent, auditable rule management during investigations.
Take the Tour -
Syslog Event Filtering for SIEM Integrations: SIEM-connected environments can now configure which AIR events are forwarded via Syslog. Analysts can focus on critical events, such as login failures or case creation, and exclude repetitive operational data to improve visibility in Splunk, QRadar, or Microsoft Sentinel.
This release also delivers broader improvements in the Hunt/Triage workflow with asynchronous and resilient Git synchronization and enhanced Sigma metadata visibility. Analysts benefit from more fine-grained filtering and grouping of findings based on rule authorship and status, promoting efficient prioritization.
Organizations integrating AIR with external SIEM platforms gain enhanced control over event streaming through flexible syslog filters, reducing noise and improving actionable insights. License usage and capacity reporting have been updated for greater consistency across multiple Consoles sharing a license key.
Network isolation on Linux and macOS assets has been fortified to filter inbound/outbound traffic reliably, terminate existing connections upon isolation, and apply bidirectional exclusion policies, ensuring dependable containment during investigations.
RelayPro has been enhanced with architectural upgrades that improve proxy efficiency, connection pooling, and operational logging to maintain robust connectivity at scale.
Multiple bug fixes address report generation timeouts, advanced filtering accuracy, evidence browsing convenience, access control enforcement, export stability under load, audit job performance, and responder startup consistency—ensuring a more stable and performant platform experience.
The embedded Binalyze MITRE ATT&CK Analyzer advances to version 12.5.2, incorporating false positive reductions in YARA and detection rules, and synchronization with the latest Sigma community contributions for up-to-date behavioral detection.
Click here for more detailsAIR v5.13
02 March 2026
Feature
The release of Binalyze AIR v5.13 brings critical enhancements focused on improving the reliability and efficiency of investigation workflows, particularly around MITRE ATT&CK rule management and system stability. These updates enable security and investigation teams to conduct evidence collection, correlation, and response tasks with greater confidence and faster throughput, reducing downtime and operational delays.
-
AIR Console: MITRE ATT&CK Rules Download Optimization and Resilience: Improved package download efficiency, retry logic, and validation accelerates rule pack retrieval and reduces incomplete transfers for SaaS and on-prem deployments.
-
AIR Console: Queue Initialization and Cache Connection Reliability: Enhanced job queue startup and Redis connection handling ensure stable and predictable evidence analysis task execution, eliminating transient startup errors and backend delays.
-
Responder: MITRE ATT&CK Rules Download Stability and Resilience: Reinforced rule package download integrity and error handling maintain verified rule delivery despite variable bandwidth, supporting uninterrupted concurrent deployments and investigation sweeps.
-
TACTICAL - Windows: Immediate Network Isolation: Isolation commands now sever network connections instantly while preserving monitored visibility, enabling rapid containment with ongoing responder connectivity for continuous evidence collection.
This release also includes system reliability improvements such as enhanced Redis error handling that prevents lingering connections and session locks, which optimizes backend synchronization and cache operations within the AIR Console.
Bug fixes address inefficiencies in Responder upload workflows by removing duplicate intermediate interACT evidence files and recalibrating polling intervals for exclusion list synchronization, improving overall upload performance and data consistency.
The Binalyze MITRE ATT&CK Analyzer is updated to version 12.5.0, extending detection coverage with new and refined rules for multiple adversary toolsets like DeskRAT, LockBit 5.0 variants, and MuddyWater operations. Sigma rules are refreshed to include the latest community-sourced detection patterns, and Dynamo Analyzer’s classification models are refined to better categorize domains in large file transfer and sharing contexts.
Click here for more detailsAIR v5.12
18 February 2026
Feature
The release of Binalyze AIR v5.12 introduces key enhancements that improve evidence correlation, event log collection, and analysis precision. These updates provide cybersecurity teams and analysts with greater operational visibility and streamlined investigation workflows, reinforcing AIR’s forensic-level visibility across enterprise assets.
What is new?
-
Advanced Time Display and Copy Options: The DateTime component within AIR Console now allows analysts to view and copy timestamps in multiple formats including UTC, ISO, local, and relative time. This enhancement streamlines correlation activities across multiple evidence sources and logs during complex investigations.
-
Improved Kerberos Event Collection for KDC Event ID 42: Added support for critical Kerberos Key Distribution Center events (Event ID 42) within default Windows event collection profiles. This expands detection visibility for authentication downgrade and anomaly scenarios often relevant in enterprise breaches.
The DateTime display includes a contextual pop-over revealing multiple time formats (UTC ISO 8601, UTC, local, relative, and timestamps), simplifying event timeline correlation for assets in different time zones. Copying timestamps now generates event records for operational audit and forensic traceability.
Event log acquisition profiles (Full, Quick, Compromise Assessment) have been refactored to capture a broader, more relevant set of event IDs. With expanded coverage (214 events in Full, 78 in Quick, 31 in Compromise Assessment), investigation teams benefit from richer context in timeline analysis without manual configuration.
File Explorer usability is enhanced with an increased default display of 100 items per page, reducing pagination and improving navigation through large directory structures. A fix in multi-directory selection ensures accurate path handling for targeted evidence collection.
System performance is improved by refining endpoint name change event handling. AIR now suppresses excessive audit logs and notifications related to name changes, especially in golden image deployment scenarios, reducing load and supporting stable operation.
DRONE analysis workflows have been stabilized by preventing stalled re-analysis tasks due to cache issues. This assures uninterrupted automated retrospective detection and improves reliability for analysts reviewing evidence with updated detection rules.
Responder component configuration fields have been renamed for clarity to reduce confusion when setting evidence storage destinations for automatic upload to external repositories.
Multiple bug fixes address critical issues including responder task display naming, registration handling for assets with identical cloud instance IDs, SQLite insert errors in Windows legacy responders, path concatenation in File Explorer, and UI navigation consistency in organization selection. The Audit Logs export API in SaaS mode now handles heavy activity reliably, and the AIR Home page filtering displays updated and accurate asset and case counts. Auto-scaling and recovery stability have been improved for SaaS tenants.
Binalyze MITRE ATT&CK Analyzer is updated to version 12.4.0. The Dynamo Analyzer now suppresses benign false positives and adds detection of suspicious RunMRU commands. Expanded detections cover high-risk email file extensions, enhancing visibility into initial access vectors. YARA and MITRE ATT&CK analyses include new threat detections (e.g., Pulsar RAT, Interlock ransomware, OrcaC2 implants) with enhanced alert severity for remote access tools. DRONE integrates the latest Sigma rule releases from SigmaHQ and Hayabusa repositories, offering hundreds of updated correlation patterns for system logs and security events.
Click here for more detailsAIR v5.11.6
5 February 2026
Hotfix
Improvements
-
Smarter evidence analyzer behavior for missing artifacts
Updated DRONE analyzer logic now skips analysis tasks when expected artifacts are absent from collected data. This prevents confusing error messages―making error logs clearer and more accurate for investigation teams. -
Dynamic scaling of visit intervals for large-scale asset deployments
AIR now calculates responder visit intervals based on asset count and environment type. This ensures scalable performance in environments with thousands of assets while maintaining efficient responder–server communication.
Bug Fixes
-
Task setup blocked when using asset filters
Resolved an issue where applying any advanced filter during task setup (e.g., acquisition, Hunt/Triage) caused the setup step to freeze. Analysts can now use advanced asset filtering without workflow interruption. -
Evidence import fails due to asset name mismatch
Addressed an issue during off-network evidence import where inconsistent casing or truncation in asset names prevented valid evidence from being matched to existing assets. This fix allows for broader compatibility based on normalized name matching. -
Investigation Hub asset filter crashes with large cases
The "Asset" dropdown in Investigation Hub could become unresponsive in investigations with thousands of assets. The filter now supports virtualized loading for smoother performance in enterprise-scale environments. -
Unexpected Sigma detections during Hunt/Triage
Fixed a limitation where two embedded Sigma rules (including “Clearing of event logs”) were automatically triggered during Hunt/Triage regardless of analyst selection. Rules now execute only when explicitly chosen. -
Asset registration failure on identical cloud instance IDs
In environments where multiple assets share the same cloud infrastructure ID, responder registration could fail. AIR now handles additional identifiers to differentiate assets reliably in these cases. -
DRONE analysis on imported data blocked by nil values
Resolved an issue where certain re-analysis tasks (DRONE on imported evidence) would remain stuck due to invalid or nil backend entries. The fix ensures proper fallback and completed task cleanup. -
MFT evidence missing from full collections
In some full collection workflows, raw MFT files were collected but not reflected in task results. This has been resolved to ensure MFT is preserved and available across all workflow types. -
History artifacts marked as corrupted
Fixed an issue where collected browsing history files were unreadable due to malformed formats. AIR now handles different browser versions smoothly for this artifact type. -
Drone Analyzer error on missing or renamed database columns
Analysis tasks that rely on specific columns now handle mismatches between rule versions and underlying evidence more gracefully, avoiding task failure. -
Date parsing handled consistently in DRONE rules
Ensured that DRONE dynamically respects analyst-defined date fields in rule exports. Incorrect fallback assignments to unrelated timestamps have been corrected. -
Startup panic during NTFS evidence collection
Stabilized collection engine in scenarios where NTFS evidence items are missing or inaccessible. The responder now exits cleanly without interrupting the overall task. -
Case database lock files removed after acquisition
Corrected behavior where temporary journal files remained on disk after off-network acquisitions. These temporary artifacts are now cleaned up automatically. -
Windows 11 build number now collected
Updated evidence parsing to include accurate operating system build numbers for Windows 11 assets. These are now visible in both Case.db and Investigation Hub.
Binalyze MITRE ATT&CK Analyzer is now at version 12.2.0, introducing expanded and enhanced detection capabilities across multiple threat categories, including comprehensive rule coverage for advanced malware families such as RedLeaves RAT, ChronosRAT, and PlugX—covering variants used by CL-STA-0969 actors targeting telecommunications infrastructure—along with new Sigma and Dynamo rules to detect suspicious administrative share access (for example, C$ and ADMIN$) within ShellBag artifacts following interactive or lateral movement activity; this release also delivers improved detection for malware frameworks like VoidLink and Defender manipulation techniques via Windows Security Center services, expanded Linux backdoor coverage with new YARA rules for MystRodX, a stealth backdoor leveraging DNS and ICMP triggers to remain dormant until activation, and enhanced hacker tool flagging through improved rule sets that identify known attacker tools, scripts, and artifacts commonly uncovered during retrospective forensic analysis.
AIR v5.11.3
15 January 2026
Hotfix
Improvements
-
Investigation management audit logs now include auto-closure reasons: Users can now see the reason a Case was automatically closed by the system in the audit trail. This enhancement improves transparency and helps analysts understand license-based behavior behind automated Case closures.
Bug Fixes
-
Fixed filtering in Case search: Resolved an issue that impacted filtering results while searching active or closed Cases in the AIR Console.
-
Correct asset selection in disk image views: Fixed behavior in the disk image detail page where selecting a single asset unintentionally triggered multiple assets. Analysts can now correctly initiate evidence acquisition from a specific disk image.
-
Processor selection logic fixed in disk image tasks: An issue causing wrong processor selection for performing disk image actions was resolved, ensuring consistency across investigation workflows.
-
Task duration display corrected: Fixed inconsistencies where task duration times were incorrectly displayed on the task details page. Duration now reflects accurate timing based on task start and completion.
The Binalyze MITRE ATT&CK Analyzer has been updated to version 12.0.0. Binalyze MITRE ATT&CK Analyzer v12.0.0 introduces major detection improvements across Dynamo, YARA, and Sigma capabilities to strengthen threat identification within collected evidence. This release expands Dynamo rule definitions to better spot hacker tools, enhances MITRE ATT&CK Analyzer + YARA coverage with new detections for threats and techniques such as the CQTools toolkit, LOLDrivers-based malicious/vulnerable drivers, MgBot backdoor, ValleyRAT RAT and related C2 activity, and executables signed with stolen or suspicious certificates, and also integrates the latest Sigma rules from SigmaHQ and Hayabusa to broaden DRONE detection coverage.
AIR v5.11
12 January 2025
Feature
The release of Binalyze AIR v5.11 introduces key enhancements designed to improve investigation workflows and evidence management across diverse environments. This update empowers security and investigation teams with greater flexibility in evidence storage, asset integrity verification, and streamlined asset navigation, supporting faster and more accurate cyber investigations.
What is new?
-
Google Cloud Storage support: AIR now supports evidence upload and archival to Google Cloud Storage. This provides analysts and investigation teams with greater flexibility in selecting secure cloud repositories for collected evidence, improving integration with multi-cloud environments and accelerating post-incident data availability for review.
-
Golden Image hostname conflict alert: AIR automatically identifies assets that share duplicated hostnames due to image deployment errors and raises a visible alert within the Console. This ensures analysts can maintain asset integrity during investigations and prevents misattribution of evidence sources.
-
Asset menu restructuring: The redesigned Asset view separates Assets into three intuitive sections: Devices, Disk Images, and Cloud Assets. This streamlined layout helps analysts quickly locate relevant evidence sources, assess responder status, and initiate investigation workflows with improved clarity.
This release also includes several improvements and new features. The AIR Console management now detects hostname conflicts caused by image cloning, presenting clear alerts to safeguard evidence integrity and minimize asset misidentification during investigations. The Asset section has been restructured into distinct categories with tailored views and filters, enabling analysts to efficiently navigate large environments and focus on relevant asset sources.
Enhancements to backend APIs introduce task ID filtering within case investigations, allowing precise tracking and validation of evidence collection steps in multi-asset workflows. User management is improved with role-based filters, streamlining user access audits and ensuring appropriate authorization for investigation privileges.
Expanding AIR’s multi-cloud compatibility, evidence can now be stored directly in Google Cloud Storage. This supports forensically sound preservation of collected artifacts while aligning with organizational compliance and retention policies.
Several critical bug fixes improve platform reliability: timeline views now respect exact date selections including empty ranges, preserving chronological accuracy during investigation reviews. Task listing and pagination performance on the Tasks page has been optimized to handle high task volumes without unresponsiveness, supporting robust operations in large investigations.
In addition, the Binalyze MITRE ATT&CK Analyzer has been updated to version 11.6.0. The DRONE engine incorporates refined detection logic for suspicious Windows process behaviors and administrative share activities, reducing false positives and enhancing detection of lateral movement and privilege escalation techniques. Sigma detection rules have been synchronized with the latest repositories, extending coverage of adversary tactics and improving MITRE ATT&CK correlation accuracy.
Full details follow below. Binalyze AIRv5.11 Release Notes
Click here for more detailsAIR v5.10
26 December 2025
Feature
The release of Binalyze AIR v5.10 extends the platform's management and investigation capabilities to Google Cloud Platform, providing broader multi-cloud forensic-level visibility. This update introduces enhanced flexibility with interACT 2FA settings and streamlines evidence organization in multi-tenant environments through automatic repository folder creation, supporting faster and more efficient incident response workflows.
What is new?
- Google Cloud Platform (GCP) Support: AIR now extends its cloud forensics and asset management capabilities to Google Cloud Platform. Security and investigation teams can now enumerate, sync, and deploy Responders directly to their GCP assets, enabling consistent, forensically sound evidence collection and incident investigation across multi-cloud environments.
- interACT 2FA Disable Option: Allows global administrators to disable Two-Factor Authentication (2FA) for interACT access when operational flexibility is required during live-response investigations.
-
Custom Evidence Collection Naming: A new capability in Settings → Console Settings → Features allows users to customize how evidence files and folders are named—whether saved locally on assets or uploaded to remote Evidence Repositories. Users can define a naming template by combining text with variables such as Timestamp, Organization Name, Task Name, Asset Name, and Case ID. Using / in the template creates folder structures for logical organization. This improves repository maintenance and ensures clear separation of evidence in multi-tenant environments. Folder names are limited to 50 characters.
-
Full Text Search: Enables investigators to search both file contents and metadata on remote assets using keywords or regex patterns. This allows targeted searches across documents, configuration files, logs, and other text-based data to quickly identify indicators of compromise, policy violations, or evidence of data exfiltration. The feature supports keyword and pattern matching, reusable search profiles, file-type filtering, and cross-platform investigations for faster, more focused evidence discovery.
This release adds a new Application Information API endpoint providing authenticated systems and administrators with core version and configuration details about the AIR deployment. This foundation supports integration, configuration validation, and automated health monitoring for orchestration systems, enhancing operational confidence and auditability.
Administrators gain granular user access control over interACT 2FA enforcement, enabling a disable option for live-response investigation flexibility without compromising overall system security policies.
The online acquisition workflow now supports automatic creation of normalized organization-level folders in evidence repositories. This improvement ensures collected evidence is maintained under clear organizational contexts, facilitating repository management and chain-of-custody transparency across tenants.
User experience enhancements include fully resizable modal pages in the AIR Console, allowing analysts to adjust viewing panels for artifact details and visual data, improving workflow efficiency during evidence review.
Investigation managers benefit from a new user search field when assigning case visibility, accelerating user selection in environments with large user bases and reducing operational friction during time-sensitive investigations.
Windows evidence analysis improvements address inconsistencies in UserAssist and Amcache artifact parsing and presentation, aligning timestamps and metadata to enhance accuracy in investigative timelines and activity reconstruction.
Several bug fixes improve platform stability and accuracy, including resolving duplicate endpoint registration conflicts on Linux assets, correcting UserAssist Focus Time conversions, fixing DRONE YARA recursion logic, aligning Shellbag timestamps, and improving event log search result handling. Sigma XML key/value filtering and Amcache parsing have been refined to enhance detection precision and artifact completeness.
The Binalyze MITRE ATT&CK Analyzer has been updated to version 11.5.0. The Dynamo Analyzer now includes broader detection coverage with improved rule accuracy and maintenance. The ATT&CK/YARA definitions expand recognition of adversary techniques, and DRONE integrates the latest Sigma rule corpus, ensuring continuous alignment with community detection research and extended behavioral coverage.
AIR v5.8.5
18 December 2025
Hotfix
Corrected an issue that prevented AIR Console installation from completing successfully when proxy configurations were applied. During setup, the system failed to reference saved proxy settings while verifying license information with the database. This has been resolved to ensure consistent proxy handling throughout the installation flow. This fix improves compatibility for environments using outbound proxy configurations.
Binalyze MITRE ATT&CK Analyzer is now at version 11.4.1
Improved detection of adversary techniques using ClickFix-style social engineering: DRONE Analyzer has been updated to strengthen its ability to flag suspicious command line patterns found in RunMRU artifact sources. These updates identify PowerShell-encoded commands and known malicious script execution workflows associated with misleading command line usage.
Added detection of deceptive file path patterns commonly used in Run shortcut entries to lure users into executing unauthorized commands. This adds greater forensic-level visibility into possible ClickFix-influenced behaviors during security investigations.
AIR v5.8
11 December 2025
Feature
The release of Binalyze AIR v5.8 delivers significant enhancements to evidence collection, analysis, and investigation workflows—strengthening forensic-level visibility for cybersecurity and investigation teams. Key capabilities include offline evidence acquisition in Windows Recovery Environment, improved time zone handling across assets, and expanded artifact coverage for macOS, enabling analysts to accelerate incident response and investigation correlation at scale.
What is new?
- Evidence Collection in Windows Recovery Environment: AIR Windows off-network responders can now collect evidence inside Windows Recovery Environment (WinRE), supporting forensically sound acquisition from non-bootable assets, reducing imaging time and costs.
- Timezone Visibility and Filtering on the Assets Page: Asset detail views now display time zones and support filtering by timezone, enhancing cross-regional timeline correlation for faster investigation workflows.
- macOS Artifact Expansion: Added collection of macOS Spotlight indexes and USB storage history artifacts, enriching user activity and data movement visibility.
- PowerShell Console Host History Line Numbering: Parsed PowerShell console history now includes line numbers, enabling precise command execution order for improved timeline accuracy during live response.
- MFT CSV Performance Refactor: The Master File Table export has been optimized with a multi-threaded parser, significantly reducing analysis times for large file systems.
- Proxy Configuration Evidence Enhancement: Proxy configuration data is now captured as part of collected evidence, allowing verification of system-level network redirection and unauthorized proxy use.
This release further includes a dedicated timezone field for assets visible in detail pages and filterable via advanced search, helping analysts organize data and align event timelines across distributed environments. Tactical improvements enable off-network responders to operate within WinRE for efficient offline evidence collection from compromised or non-bootable systems, preserving evidence integrity before remediation actions. Proxy configuration detection has been broadened to reveal hidden network interceptions that could indicate command-and-control or data exfiltration channels. The MFT CSV export’s performance gains accelerate file system timeline reviews and change detection in enterprise-scale investigations.
The PowerShell console history enhancement strengthens command activity correlation by adding line numbers to parsed artifacts. macOS investigations now benefit from new artifact sources including Spotlight indexes, and USB storage history, deepening insight into file metadata, index activity, and external device usage. Responder updates provide configurable HTTP request headers for integration flexibility, asynchronous command execution through interACT’s new background aliases, and updated User-Agent headers to improve compatibility with enterprise network policies.
Bug fixes address Microsoft Edge cookie acquisitions, correct OS version reporting in the Investigation Hub, resolve user-group relationship display issues for SAM data, and fix filename parsing in DRONE YARA scanning to ensure consistent evidence processing.
Additionally, the Binalyze MITRE ATT&CK Analyzer advances to version 11.4.0, expanding detection coverage across shell histories, browser and registry artifacts, and system configurations on Windows, macOS, and Linux. Detection rules now identify Dystopia Windows RAT variants leveraging Discord, Telegram, and GitHub, with improved signature precision to reduce false positives. Sigma rule sets are updated from community sources to enhance automated analysis workflows within DRONE.
Full details follow below. View Binalyze AIR v5.8 Release Notes
Click here for more detailsAIR v5.7
04 December 2025
Feature
The release of Binalyze AIR v5.7 delivers key enhancements designed to improve investigation workflows and asset management for security and investigation teams. This version introduces Maintenance Mode to safeguard asset integrity during maintenance, expands evidence acquisition navigation, and enhances global search capabilities—empowering analysts with clearer visibility and control across hybrid environments.
What is new?
-
Maintenance Mode for Device Assets: Analysts can now place assets into Maintenance Mode to prevent task execution during diagnostics or hardware work. interACT and log gathering remain active to maintain forensic continuity.
-
Global Search for Acquisition Profile Evidence Groups: Enables consolidated search results across acquisition profiles and evidence groups, streamlining evidence retrieval in large-scale investigations.
-
Acquire Evidence Menu Expansion: The Quick Start menu’s “Acquire Evidence” section now expands to show “From Device,” “From Disk Image,” and “From Cloud” options to better guide analysts in acquisition strategy.
-
Device, Disk Image, and Cloud Menus in Navigation: The Asset menu is reorganized into separate top-level entries for faster access and management across asset types.
-
Feedback Form and UI Flow Updates: New in-console feedback form with up to five daily submissions per user; improved Resource Center layout enhances usability without obstructing navigation.
The introduction of Maintenance Mode addresses operational challenges where assets undergoing diagnostics or hardware service needed to be isolated from automated tasks, preventing conflicts and preserving chain-of-custody. Analysts can now easily identify and control maintained assets within filters and device details for more transparent management at scale.
The updated “Acquire Evidence” navigation with distinct acquisition paths supports analysts operating in hybrid or multi-cloud environments by clarifying evidence source options. Although “From Disk Image” and “From Cloud” options are marked as coming soon, this prepares users for upcoming capabilities and improves workflow clarity.
The Asset menu redesign further facilitates large-scale response operations by separating Devices, Disk Images, and Cloud entries, reducing filtering complexity. Global search enhancements now return acquisition profile evidence groups, enabling higher-level correlation across investigations and better cross-case insight.
With the new feedback form, investigation teams gain a direct channel to share feature-level insights securely from within AIR, improving product responsiveness to analyst needs. The Resource Center UI improvements ensure efficient access to resources on diverse screen sizes.
Additional improvements include enriched role identification in token creation APIs for enhanced audit and authorization tracking, supporting accountable delegated automation and investigation task management.
Bug fixes resolve issues affecting UI layout, scheduled task duplication, task assignment offline, shareable deployment link consistency, keyword upload validation, Hunt/Triage update warnings, and Resource Center icon alignment—enhancing overall system reliability and usability.
The Binalyze MITRE ATT&CK Analyzer has been updated to version 11.3.1, with Dynamo Analyzer expanding detection of remote monitoring tools and crypto-mining domains. New YARA rules increase coverage of ransomware variants and PowerShell techniques, while Sigma rule updates in DRONE improve behavioral detection across timeline evidence analysis.
Click here for more detailsAIR v5.6
19 November 2025
Feature
The release of Binalyze AIR v5.6 advances the platform's investigation and response capabilities with critical enhancements in real-time collaboration, search efficiency, and operational control—empowering security analysts to execute more targeted and coordinated incident response workflows with greater efficiency and clarity.
What is new?
-
Investigation Hub Live Collaboration and Activity Sync: Analysts can now observe real-time user presence, comment updates, and evidence flag changes within the Investigation Hub. This enables investigation teams to collaborate simultaneously on the same evidence and instantly see each other’s actions without refreshing the view.
-
Investigation Hub Search Enhancements with Prefix Support: The new prefix search capability allows using the “*” symbol in the Investigation Hub to find evidence names or keywords starting with a given text. This makes it faster to locate related items across large investigations, particularly when searching partial filenames, process names, or user activities.
-
Maintenance Window Configuration for SaaS Environments: Administrators can now select preferred maintenance windows directly within AIR. This ensures updates and maintenance operations occur within defined time slots, providing predictable scheduling for managed tenants.
-
Command Snippets Management Improvements: Snippets can now be tagged and grouped, making it easier to filter or categorize repeatable live-response actions in interACT sessions—improving operational efficiency and consistency for investigation teams.
-
Hunt/Triage Location Inclusion and Exclusion Support: Analysts define precise include/exclude path patterns for each platform in the Hunt/Triage feature. This ensures keyword and YARA scanning occurs only on relevant directories—improving performance and reducing noise during evidence analysis.
-
Expanded Evidence Support for macOS and Linux: New artifact sources, including DNF/YUM History, SSH Files, System Logs, and software update information, improve cross-platform visibility and provide deeper forensic coverage for investigations.
This release significantly enhances collaboration within the Investigation Hub by providing live user presence indicators and instant activity synchronization, reducing communication gaps during incident response. The addition of prefix search accelerates locating relevant evidence or findings across large datasets, a crucial boost for fast-paced investigations.
Administrators gain granular control over SaaS maintenance schedules with the new configurable maintenance windows. This feature ensures operational continuity and adherence to organizational change management policies.
Investigation teams benefit from improved command snippet organization in interACT, enabling more efficient reuse and categorization of live-response actions. The Hunt/Triage feature now supports include/exclude path filtering per platform, allowing for more focused and performant scanning during hunts and triages.
Artifact support broadens on macOS and Linux, adding critical sources such as software update records and system logs, enriching cross-platform forensics data accessible to analysts.
Notification delivery has been optimized with a move to Server-Sent Events (SSE), improving real-time visibility while reducing network overhead for ongoing investigations.
Responder communication and authentication flows are strengthened to maintain stable, secure connections during extended investigations. RelayPro enhancements improve connection reliability and resource management in environments with persistent remote communication.
Additional refinements include fixes to search input behavior, task list sorting, and asset tagging status alignment ensuring a smoother investigation management experience. Network isolation policies and key artifact collections, such as ScreenConnect logs and browser login data timestamps, are corrected for accuracy and reliability.
The Binalyze MITRE ATT&CK Analyzer advances to version 11.0.0 with broader detection coverage, including new analyzers and updated Sigma rules, reinforcing AIR’s capability to surface and prioritize adversary techniques with increased accuracy.
Full details follow below. Binalyze AIR v5.6 Release Notes
Click here for more detailsAIR v5.4.5
03 November 2025
Hotfix
Fix for Microsoft 365 evidence visibility in Investigation Hub
Resolved an issue where Microsoft 365 evidence appeared with empty categories in the Investigation Hub after task execution and ingestion. The issue was caused by a query failure triggered by the parsing of evidence category/platform names containing hyphens. With this fix, all Microsoft 365 evidence sections are now properly imported and display the expected data within the Investigation Hub.
AIR v5.4.4
27 October 2025
Hotfix
-
Enhanced User Import for Organizations and Roles
Resolved an issue in the user import workflow where the selected organization and role could not be overridden per user during CSV import. Administrators can now modify organization and role assignments in the preview step, and the updated selections are accurately reflected in the user list post-import. -
Deploy New Page Functionality Restored
Fixed a critical issue that prevented the “Deploy New” page from loading when the Relay Server feature was enabled. This update ensures that endpoint deployment can proceed smoothly, regardless of the Relay Server configuration. -
Accurate DRONE Analyses Task Counts in Case View
Addressed a display issue in the case overview where the task count for “DRONE Analyses” incorrectly appeared as zero, even when tasks existed. The task counter now correctly reflects the number of analysis tasks within a case.
AIR v5.4
22 October 2025
Feature
The release of Binalyze AIR v5.4 introduces significant enhancements that empower DFIR and security analysts with more agile forensic validation, improved secure communication, and scalable user onboarding. These updates streamline investigation workflows, strengthen data integrity in segmented environments, and extend endpoint visibility—delivering a robust platform for rapid incident response and comprehensive forensic analysis.
What is new?
-
DRONE analysis on previously or newly collected evidence files: Analysts can now initiate DRONE analysis directly from the Investigation Hub on any existing evidence file, regardless of prior responder analysis, enabling rapid reassessment and streamlined forensic workflows.
-
RelayPro: Introducing RelayPro, a secure, authenticated HTTPS relay server with JWT-based two-step authentication that replaces the legacy relay implementation. RelayPro provides enhanced data integrity, independent deployment, administrative control, and improved reliability in restrictive or segmented network environments.
-
Bulk User Import via Email List or CSV Upload: Large-scale user onboarding is simplified by enabling administrators to import users with role and group metadata in bulk, accelerating enterprise deployments and ensuring consistent privilege management.
-
macOS Evidence Expansion: The responder now collects additional evidence sets., including SSH, Launchd, Crash logs, Apple System Logs, Gatekeeper data, and more—offering deeper visibility for Apple ecosystem investigations. (Credits: Jessica W.)
AIR’s Asset & Task Management module has been refined by renaming the Triage module to “Hunt/Triage” to better align with forensic workflows emphasizing proactive hunting and rule-based anomaly detection. Enhancements include mandatory naming and tagging for Hunt/Triage rules, with full support for tag deletion, improving rule organization and clarity. Bulk deletion capabilities across rule sets, acquisition profiles, auto asset tags, interACT command snippets, and more provide streamlined maintenance of forensic and automation configurations.
Within AIR Settings, the bulk user import feature via CSV or email list expedites onboarding with optional metadata assignments. Backup file management now includes AIR version information in .abf filenames, simplifying environment recovery and audit processes.
The Investigation Hub now displays DRONE Analysis progress indicators, allowing teams to monitor, access, and manage ongoing or completed analyses in a transparent and centralized manner—reducing the need for external monitoring and enhancing evaluation workflows.
Significant extensions to macOS evidence collection expand artifact coverage to system and user-level persistence and activity data, significantly improving cross-platform forensic baselines. A new Chrome Quick Assist collector adds visibility into remote support session activity, aiding detection of adversarial lateral movement through legitimate remote access tools.
RelayPro marks a critical architecture upgrade by enabling fully authenticated, logged, and JWT-secured HTTPS proxy communication between responders and console. This shift from legacy SOCKS5 relays lowers attack surfaces, aligns with best security practices, and strengthens deployments in zero-trust or segmented networks with comprehensive connection validation and administrative control.
The DRONE re-analysis feature allows server-side execution of compatible DRONE modules on any previously or newly collected evidence, facilitating retrospective validation of threat intelligence or detection logic without requiring live asset connectivity. This capability supports forensic-level re-evaluation in both online and air-gapped incident response scenarios, preserving investigation integrity and agility.
Bug fixes in this release address MITRE tactic navigation issues within the Investigation Hub, correct SMB address string parsing in DRONE databases, and restore efficient search functionality in Sigma Hunt/Triage event records—enhancing usability and investigation reliability.
Binalyze MITRE ATT&CK Analyzer advances to version 10.8.0, featuring upgraded Dynamo Analyzer detection coverage across Windows, macOS, and Linux, new behavioral Browser Downloads analysis, and renamed Amcache module for clarity. YARA rules are enriched with new signatures for emerging threats and privilege escalations. DRONE integration now includes updated Sigma rule sets from SigmaHQ and Hayabusa repositories, ensuring continued alignment with community threat intelligence.
Click here for more detailsAIR v5.2.11
30 September 2025
Hotfix
-
Improved Disk Image Status Detection: Addressed a bug where the online status of disk image assets was not correctly displayed in the endpoints table. This fix enhances visibility and accuracy of asset status during investigations.
-
Investigation Hub Enhancements:
-
Flag visibility issues with previously created evidence records have been resolved. Flags manually added to evidence prior to upgrading from older versions are now preserved and visible after migration.
-
Fixed Investigation Hub migration issues and enhanced Windows event record migration speed and efficiency.
-
Corrected inconsistencies between global search results and the filtered data shown in the evidence tables. Users can now rely on matched counts and results for more accurate evidence reviews.
-
Improved visibility and clarity for investigation import status to provide users better feedback during import processes.
-
Improved the clarity and detail of migration status updates to give users better feedback throughout the investigation migration process. Status details now provide richer context, making it easier to understand progress and enabling faster, more effective support when needed.
-
AIR v5.2.8
25 September 2025
Hotfix
-
Improved Investigation Hub Migration Behavior After Upgrade
Fixed a critical issue where, in some cases, Investigation Hubs became blocked during data migrations after upgrading from version 5.0 to 5.2. This bug prevented access to investigations and disrupted analysts' workflows. With this fix, existing Investigation Hubs now load successfully after the upgrade, and migrations complete without introducing unnecessary delays. (Credits Joe T.) -
Fix for Flag Removal Error in Investigation Hub
Resolved a problem where users were unable to remove previously selected flags within the Investigation Hub interface. Attempting to remove multiple flags caused errors and prevented completion of the action. The removal mechanism has been corrected, enabling smooth interaction with the flagging feature. -
User Management Table Sorting Correction
Fixed an error that occurred when sorting the "Roles" column on the Users page under Settings. The fix ensures proper sorting functionality within user role management.
AIR v5.2
22 September 2025
Feature
The release of Binalyze AIR v5.2 introduces powerful new capabilities to enhance digital forensic and incident response operations. Remote command execution, and endpoint identification, this update empowers DFIR and security analysts to streamline workflows, improve accuracy, and accelerate investigations.
What is new?
-
Command Snippets in interACT Terminal: Investigators and response teams can customize, execute, and reuse predefined or custom command snippets within the interACT terminal, streamlining repetitive operations and boosting accuracy. See It in Action
This update includes a breaking change for macOS Responder deployment, now using the native ComputerName for device identity to improve asset matching and reduce confusion. The AIR Console enhances asset and task management with optimized LDAP hostname extraction and detailed task duration visualizations to better benchmark task performance.
Investigation Hub now features a compact timeline visualization using icons and severity markers alongside actionable comment icons, fostering improved collaboration and auditability during investigations.
The interACT component gains a full command snippet library for command reuse and sharing, along with an increased file upload limit from 200MB to 500MB, extending its utility in complex response scenarios.
Administration improvements include audit log search across multiple data fields and a password generator tool to create secure user credentials natively within the platform, enhancing security and usability.
Numerous bug fixes address critical issues such as DRONE hash detection accuracy, SMB authentication failures, disk image management, responder upload reporting, timestamp consistency across timezones, and interACT session stability after server restarts.
Additionally, the Binalyze MITRE ATT&CK Analyzer has been updated to version 10.5.2 with expanded detection capabilities for attacker tools and malware variants, along with updated Sigma rule sets to keep detection logic current.
Click here for more detailsAIR v5.0.4
04 September 2025
Hotfix
Resolved Case Migration Issue Following Upgrade: Fixed an issue that caused case migrations to become stuck after updating to AIR v5.0, preventing users from opening existing cases. This was caused by a problem in the database migration scripts, which shared the same root cause as the issue described below. A permanent fix has been implemented to ensure seamless upgrades without disrupting case accessibility.
Improved Handling of Evidence Import Platform Names: Addressed a bug affecting evidence import functionality (CSV, PST, and Tornado formats) where platform names containing multiple words (such as "Windows 365") led to errors due to incorrect database table naming conventions. The system now correctly handles these cases to prevent import failures.
AIR v5.0
21 August 2025
Features
The release of Binalyze AIR v5.0 introduces a major evolution in our digital forensics and incident response capabilities with a focus on enhanced investigation workflows, case management, and AI-powered assistance. These enhancements aim to empower DFIR and security analysts with faster, more interactive, and more insightful tools for threat detection, root cause analysis, and collaborative incident response.
What is new?
-
Redesigned Timeline in Investigation Hub: A completely rebuilt timeline offering high-performance searches, zoomable event visualizations, advanced evidence-specific filters, and enriched interactivity with exports for streamlined reporting and collaboration. See It in Action
-
Enhanced Case Management with Insights & Customization: Visual task and disk usage metrics, member highlights, an insightful overview panel, and a redesigned Kanban board with customizable tags and categories for flexible case triage and prioritization. Take the Tour
-
Fleet AI – Multi-Agent DFIR Assistance with BYOAI Support: Natural language-driven expert assistance to generate hunting rules, scripts, and investigative answers with the new BYOAI feature supporting OpenAI GPT, Anthropic Claude, Google Gemini, and Ollama models for enhanced privacy and customization. View Interactive Demo
This release significantly upgrades the Investigation Hub with a powerful, multi-granular interactive timeline tightly integrated with evidence and findings. Analysts benefit from synchronized flagging, improved filtering precision, mini-maps, and export capabilities enhancing forensic workflows and collaborative analysis.
Case Management has been reimagined with actionable insights, comprehensive metadata views, collaborative note-taking, and an intuitive Kanban interface with flexible organizational tags and categories. These improvements streamline case oversight, triage, and team coordination.
Asset and Task Management improvements include more robust evidence upload handling to prevent archive corruption, refined interACT shell session UX, and an optimized one-click DRONE configuration for rapid acquisition task setup in critical incidents.
Fleet AI introduces a transformative AI-powered assistant platform delivering multi-agent expert support directly within AIR — reducing complexity, accelerating investigations, and enabling customizable, privacy-respecting AI integrations.
Additional enhancements involve improved API role handling with tags, support for acquisition profile metadata in task queries, and hardened SSL certificate serial number generation for better security and compatibility. Various bug fixes address live investigation UI errors, user group persistence, auto-tagging misclassifications, case import reliability, export accuracy, and interACT shell session stability.
Click here for more detailsAIR v4.43.9
13 August 2025
Hotfix
-
Resolved multiple deadlock scenarios in evidence acquisition. Several issues related to multithreading and concurrent access in the NTFS and SQLite-based components have been addressed. This improves stability and ensures more reliable data collection particularly in environments with high forensic activity on Windows endpoints.
-
Enhanced responder stability on Windows platforms. Fixes have been implemented to eliminate edge case deadlock conditions and database locking issues that were affecting the responder's ability to complete evidence collection and analysis efficiently.
-
Security vulnerability addressed on Windows endpoints. A critical DLL hijacking vulnerability has been fixed to improve the security posture of the AIR Responder agent when deployed on Windows systems.
-
Platform support and tooling improvements. The system's internal tooling and support structures for Linux and AIX platforms have been updated to improve compatibility and performance across supported environments.
AIR v4.43.7
30 July 2025
Hotfix
-
Improved FortiAuthenticator SSO integration by fixing group resolution logic for users assigned to a single group, ensuring accurate role and permission mapping during login.
-
Fixed a memory leak in the offline registry hive preparation process, improving stability and memory efficiency during evidence collection.
-
Fixed an intermittent issue in SaaS environments where task files failed to import into IH due to incomplete disk writes, ensuring reliable task processing and archive handling.
-
Fixed an issue where the Interact session worker goroutine could hang indefinitely due to unsent close session requests or network issues, causing WebSocket connections to remain open until a machine reboot, service restart, responder update/uninstall, or task cancellation.
AIR v4.43.6
21 July 2025
Hotfix
-
Fixed an issue where the Responder failed to handle certain error or exit codes during specific evidence collection scenarios. This bug caused the Responder to stop the entire evidence collection process prematurely. With this fix, the Responder now handles these errors gracefully, allowing it to continue collecting all remaining artifacts and complete the process partially when needed.
-
Fixed a bug caused by an incorrectly implemented fallback mechanism during page file evidence collection. This fix ensures more reliable behavior in cases where the primary method fails.
-
Fixed an issue that caused an unhandled error in the UAL log parser under certain conditions. The parser now handles such cases more gracefully to prevent unexpected termination.
AIR v4.43
8 July 2025
Features
New Multi-Asset interACT capability
AIR 4.43 introduces a completely redesigned experience for interACT, Binalyze’s remote live shell feature. This update significantly improves productivity by allowing analysts to manage multiple live sessions within a single, intuitive interface, reducing cognitive load and streamlining interactive investigations.
This short video shows Multi-Asset interACT in action.
What’s New?
-
Multi-Asset Sessions: Analysts can now open multiple simultaneous interactive shell sessions (up to 50 assets) in a single AIR console window.
-
Command Broadcasting: A new "ALL" tab enables users to send a single command to all live sessions with a single action, eliminating the need to repeat commands.
-
Flexible Layout: The new dockable interACT drawer is:
-
Resizable and movable (top, bottom, left, or right of the screen),
-
Collapsible or maximizable based on user preference or screen space.
-
-
Launch interACT from anywhere: A new interACT button is now permanently available in the AIR header bar, allowing analysts to initiate sessions from any screen.
-
Additionally, in-context launching is supported directly within the Investigation Hub, allowing for live responses without interrupting the current investigation workflow.
-
Session Visibility & Reporting:
-
Flexible session output display: View interACT results per individual asset or use the consolidated “All” tab to see responses from all connected assets in one place.
-
Reports can be generated or exported as PDF or HTML directly from the interACT window.
-
These improvements are already resonating with users and threat-hunting teams who rely on AIR for high-speed investigations. This release positions interACT as a true analyst-first feature with native multi-session awareness.
Real-Time User Online Status Indicators
AIR now displays user presence across the UI to help with team coordination and case visibility:
-
A green dot under the avatar indicates a user is currently online.
-
A gray dot means the user is offline.
-
This indicator appears in the user management table, case views, and other screens where user details are displayed.
This improvement supports collaboration in larger teams and across time zones.
Acquisition Profile Type Visibility
To reduce errors when assigning acquisition profiles to assets, AIR now displays the associated platform(s) for each profile:
-
Windows
-
Linux
-
macOS
This small but impactful change helps ensure analysts select valid profiles for each target asset, especially during baseline or full acquisitions.
Enhancements
Investigation Hub - Global Filters Repositioned
To improve efficiency, the Global Filters have been relocated from the secondary menu to the top of the Investigation Hub, immediately below the section title, ensuring permanent visibility and immediate access.
Also new:
-
‘Evidence Category’ has been added as a Global Filter.
-
These global filters persist throughout user interactions at both asset and case levels.
Investigation Hub - Relative Date/Time Filtering
AIR now supports relative time selection to apply date and time filters in the Investigation Hub. Analysts can quickly select dynamic ranges, such as “Last 5 minutes,” “Last 7 days,” or “Next 30 minutes,” by clicking on the timestamps in Investigation Hub tables.
This enhancement complements the existing absolute date/time filtering (e.g., 00:00–23:59 on a specific date) by offering more flexible, context-aware filtering, particularly useful in timeline reviews and live evidence analysis.
Investigation Hub - Improved Text Selection Actions
We've improved the visibility of contextual search tools that appear when text is selected in tables or details views.
Now clearly visible:
-
Search in the current table
-
Search in the Investigation Hub
-
Google Search
-
VirusTotal Lookup
These actions are now represented with intuitive icons and light animation to reduce the risk of being overlooked.
Binalyze MITRE ATT&CK Analyzer is now at version 9.6.1
Recent updates to the MITRE ATT&CK Analyzer and Dynamo module introduce improved coverage for emerging threats and evasive behaviors:
-
Expanded Detection of MCP Server Activity
New rules detect Model Context Protocol (MCP) server behaviors on Windows endpoints, covering configuration files, environment variables, processes, and network activity, to help identify unauthorized AI assistant access and potential data exfiltration. -
IIS Malware Coverage
Added YARA-based detection for multiple native IIS malware families, including IIS-Raid, RGDoor, IIStealer, ISN, IISpy, and IISerpent, each tuned to the unique traits of these stealthy web server threats. -
ConfuserEx Detection Improvements
Updated rules improve the detection of samples protected by the ConfuserEx .NET obfuscator, enhancing coverage of heavily packed malware. -
Suspicious Service Path Detection
Dynamo now queries all fields when identifying suspicious service paths, improving accuracy in identifying abuse scenarios. -
Minor rule refinements and false-positive reductions were included across the YARA and Dynamo rule sets.
These updates enhance DRONE’s automated assessments and MITRE ATT&CK mapping for faster, more accurate investigations. Full changelog available here.
Fixes
-
Minor UI/UX adjustments across the Investigation Hub, including feedback from usability testing.
-
Stability and layout improvements in task creation screens.
-
Interactive shell drawer display issues resolved for specific browser sizes.
AIR v4.41
10 June 2025
New Features and Enhancements
Repository Explorer – Centralized Forensic Image and File Access
A new main menu item, the AIR Repository Explorer, now centralizes access to all disk image data and repository files, replacing the previous per-asset image file management.
Once selected, the Repository Explorer will reveal a secondary menu which lists the available repositories and their contents under Global or Organizational assignments.
Key benefits of this new feature include:
-
A single interface to browse and manage repositories.
-
Download individual files directly to the user's machine.
-
Directly upload files into existing repositories using the Upload File action button.
-
Import any compatible file in the repository to mount as a ‘disk image asset’ using the new "Import Disk Image" action.
-
Improved navigation between global and organization-specific repositories across Azure, AWS S3, SFTP, and SMB.
NB: The Repository Explorer only displays repositories that are configured and available to the logged-in user. For example, FTPS will not appear unless it has been added previously.
This enhancement significantly improves visibility, usability, and operational efficiency.
Fleet AI – AI Agents for Rule Generation and Guided Investigation
Fleet AI marks Binalyze's first major step into Agentic AI for investigation and response automation, introducing our Multi-Expert Agent System (MEAS) architecture to embed specialized AI expertise directly into AIR’s investigation workflows—if and when the user chooses to activate it.
The first of these agents, Fleet Detection Engineer, debuts in AIR 4.41. It can generate validated YARA, Sigma, and osquery rules based on natural language prompts. A contextual memory system enables secure, persistent conversations, enhancing rule accuracy and usability.
If the Triage Rule wizard is open during a Fleet AI session, you can instantly accept and inject a generated rule directly into the wizard for immediate use.
Coming Soon:
-
Deeper AIR integration and task automation, including a DFIR-specific assistant to answer investigation-related questions.
-
Security guardrails for scope control, sensitive data filtering, and secure access.
-
Scalable architecture built with FastAPI, Redis (with pgvector), and Docker/ECS deployment.
-
Bring Your Own AI (BYOAI): Option to deploy Fleet AI on-premise with no Binalyze Cloud connectivity, ensuring complete data privacy.
Search in AIR’s Settings
You can now search across AIR’s Settings section and subsection titles using the new search box located at the top of the Settings secondary menu.
Selecting a result takes you directly to the relevant configuration page, where the matching item will be highlighted.
This small but powerful enhancement makes navigating complex settings faster, easier, and far more intuitive.
User Profile Photos
Users can now upload their own profile images. These will be displayed across the AIR console UI in user-facing areas, such as the user menu, case history, and activity logs. Supported for both regular and SSO-authenticated users, although not synced from the identity provider.
Event Subscription UI Improvements
The Event Subscription configuration interface, found under Main Menu > Integrations > Event Subscriptions, has been refined for improved usability. Enhancements include:
-
Categorized grouping of events.
-
Searchable interface for faster configuration.
-
Improved multi-select and toggle options for greater clarity and control.
Exclude Responder(s) from Updates
The Exclude from Updates feature allows users to prevent selected assets from receiving responder updates. This can be done individually via the More actions menu or in bulk using the bulk action bar—ideal for maintaining a state, managing phased rollouts, or excluding specific assets.
Excluded assets are hidden from update-related actions and skipped by auto-update processes. Their status is clearly indicated on the asset detail page.
To re-enable updates, use the Include in Updates action. The asset will be included in the next update cycle, and update controls will reappear.
NB Any scheduled or manual update tasks are discarded when exclusion is applied. These are not restored automatically—new tasks must be created.
Investigation Hub - Multiple Findings per Evidence
Evidence items can now display more than one finding:
-
A plus (“+”) indicator in the Finding Type column indicates when multiple findings are present for that item.
-
A dedicated "Findings" tab in the details view allows each Finding to be examined independently.
This resolves prior inconsistencies in the representation of evidence and improves investigative accuracy.
Investigation Hub - Contextual Time Filtering
You can now filter any Investigation Hub table by date directly from the column view:
-
Click a date to access options such as “before,” “after,” or “exact.”
-
Applied filters are automatically added to Advanced Filters as additional criteria.
-
Supports all date columns within the Investigation Hub.
Investigation Hub - Launch Asset Actions in the Investigation Hub
You can now launch core AIR actions—such as Acquire Evidence and Triage—directly from the asset name column within the Investigation Hub.
Simply hover over an asset name to reveal a gear icon, then click it to access quick actions instantly.
This streamlined interaction eliminates the need to return to the Quick Start screen, making task initiation faster and more intuitive.
Binalyze MITRE ATT&CK Analyzer is now at version 9.5.0
This update expands AIR’s detection capabilities through improvements to YARA and Dynamo rules:
-
YARA: Added detection for KoiLoader/KoiStealer and hacker tools used in recent campaigns. Includes false positive fixes and new rules targeting Initial Access IOCs.
-
Dynamo: Broadened tool coverage to improve context and correlation in forensic evidence.
These updates enhance DRONE’s automated assessments and MITRE ATT&CK mapping for faster, more accurate investigations. Full changelog available here.
Fixes
This release includes minor fixes and polish items from AIR 4.40 and 4.41, including UI refinements and background performance improvements.
AIR 4.39
8 May 2025
New Features and Enhancements
AIR UI Improvements to Main Navigation
-
Main Menu icons design refresh with written titless visible or hidden option.
-
General Settings, Theme selection, and Account Settings have moved to the Header Bar.
-
The organization settings are relocated to the left side of the Header Bar.
-
The Recent activity and notifications remain in the header bar but as icons only, and when selected, are now in drawers, not pop-up windows.
-
Frank AI has moved from the Main Menu to the header bar.
To see these improvements in action, click here.
MITRE ATT&CK Heatmap
A new MITRE ATT&CK heatmap has been added to the Findings page in the Investigation Hub, providing a visual overview of tactic coverage based on the volume of mapped findings.
-
The heatmap view is configurable: sort techniques by volume (ascending or descending), and toggle the display of empty techniques and sub-techniques to focus your analysis.
New Artifact Parser: Jump Lists (Windows)
We’ve added Jump List parsing to AIR’s existing Jump List collection capabilities, providing critical insight into user activity and file access history on Windows systems. This new parser supports analysis of user behavior by linking applications to accessed files with reliable timestamped evidence.
Jump Lists track files and applications opened by a user, whether it’s a document, a config file, or an executable. Even if the original file is deleted or moved, the artifact remains, offering invaluable forensic context for investigations.
Key capabilities include:
-
Accessed file paths and associated application names
-
Timestamps: first and last access
-
Access frequency counts
-
Link metadata including hostnames, MAC addresses, volume info, and more
When is it useful? - some examples:
-
Insider threat cases: Confirm if a user accessed a sensitive document they deny interacting with.
-
Ransomware investigations: Validate which application or file was opened just before an infection.
-
Deleted file tracing: Reconstruct file access even if the original file is no longer present on disk.
Note:This parser supports analysis of user behavior by linking applications to accessed files with reliable timestamped evidence.
Tornado 1.2.2: Major Upgrade with New Microsoft Collectors + DRONE Analysis Integration
The latest version of Binalyze Tornado brings a significant boost to cloud forensics with powerful new data sources and automated analysis capabilities, making Tornado 1.2.2 our most advanced release yet.
50+ New Microsoft 365 Collectors
This update dramatically expands Tornado's coverage to 99 collectors across the Microsoft ecosystem. Investigators can now collect a wide range of new cloud artifacts, including:
-
Azure Active Directory logs
-
Defender for Office 365 alerts
-
Exchange Online message traces
-
Mailbox audit and permission logs
-
Policy configurations and sign-in events
The full list of collectors is always available directly in the Tornado application.
All available collectors under both admin and user consent modes are now visible before login, improving visibility and ease-of-use when configuring collections.
DRONE Now Integrated with Tornado
Tornado collections can now be automatically analyzed using DRONE, our powerful rule-based analysis engine.
Use DRONE to:
-
Detect suspicious email content (e.g., shortened URLs, unusual attachments)
-
Identify MITRE ATT&CK techniques in Microsoft 365 activity.
-
Automatically tag and score findings (Low/Medium/High) before ingesting them into AIR.
This integration turns raw cloud data into actionable insights without manual triage.
Findings Automatically Appear in AIR’s Investigation Hub
For existing AIR customers, once analyzed, DRONE findings from Tornado are automatically sent to AIR’s Investigation Hub, giving analysts immediate visibility and context alongside other evidence sources.
Read more about Tornado here in the Knowledge Base.
User Groups for Organization Management
We’ve introduced User Groups to simplify and scale user management across organizations in AIR.
With this new feature, Global Admins can create and assign user groups—collections of users that can be linked to one or more organizations. This is especially valuable for environments with complex structures or where group-based access is managed via SSO (Azure AD or Okta).
Key benefits:
-
Centralized control: Assign entire groups to organizations instead of managing users one by one.
-
SSO integration: Groups can sync with AD or Okta groups for seamless role mapping and access management.
-
Role-aware: Users inherit access and roles from their group memberships.
-
Visibility & safeguards: Group-assigned users cannot be removed from an organization directly, ensuring clarity and consistency in access control.
Note: Only Global Admins can create, edit, and manage user groups.
Killswitch – Cancel All Running Tasks
A new "Killswitch" option has been added to the AIR Console under Settings > Danger Zone, allowing users to instantly cancel all currently running, cancellable tasks across the platform—no selection of Assets or Tasks is required.
To prevent accidental use, confirmation is required by typing a case-sensitive phrase, ‘Cancel All Tasks” before execution.
Personal Access Tokens (API)
We’ve improved how users can orchestrate AIR programmatically with new Personal Access Tokens (PATs).
Unlike existing API tokens, which operate independently of user accounts, PATs are directly linked to individual users. Any API actions performed using a PAT are logged as if they were executed by the user themselves, providing clearer audit trails and more substantial alignment with user permissions.
Key benefits:
-
User-bound: PATs inherit the user’s roles, permissions, and organization memberships automatically.
-
Lifecycle awareness: Delete the user, and the PAT disappears. Modify the user’s permissions, and the PAT’s capabilities adjust accordingly.
-
Audit clarity: All actions appear as performed by the user, not just a token.
Note: This is an API-only feature for now—there is no UI available yet.
Confirmation Warning for Large-Scale Tasking
To help prevent accidental bulk operations, AIR now includes a confirmation prompt when tasking affects 70% or more of all assets.
This new safeguard is triggered whenever a task, such as isolation, acquisition, or triage, is set to run against the majority of your asset inventory. Instead of executing immediately, the platform now displays a clear confirmation message, asking you to verify that the large-scale task is intentional.
Key benefits:
-
Accidental prevention: Avoid costly mistakes like unintentionally isolating thousands of assets due to a misconfigured API call.
-
Better control: Reinforces situational awareness before executing high-impact actions.
-
API included: The confirmation requirement also applies to API-based tasking, further reducing automation risk.
Note: This feature is automatically enabled and currently cannot be turned off. We are exploring configurability in future updates to better support smaller environments.
Binalyze MITRE ATT&CK Analyzer is now at version 9.2.2
Here is a summary of the updates since 9.0.1, which was covered in our last release notes:
YARA Enhancements: New detection rules have been added for a diverse range of advanced threats, expanding forensic coverage and improving incident response accuracy:
-
Anubis (Python): A stealthy backdoor linked to FIN7, now detectable through signature-based analysis.
-
QDoor: Backdoor malware targeting Windows systems, often used in persistent attack chains.
-
SectopRAT (ArechClient2): A powerful RAT with surveillance and remote control capabilities.
-
Lazarus APT - BeaverTail & Infostealer: Detection of both command components and information-stealing modules used in high-profile espionage campaigns.
-
StealcStealer (variant): A new strain of credential and data-stealing malware now actively detected.
-
Dunloader (Earth Kurma APT): Detection added for this staging malware used in targeted campaigns.
Dynamo Enhancements - We've also bolstered forensic detection with new rules to identify risky Windows Registry settings, including:
-
Enabled RDP: Flagging systems where Remote Desktop Protocol is active.
-
Unsecure SMB configurations: Detection of outdated or vulnerable SMB protocol usage.
-
Unencrypted WDigest: Identifying legacy authentication methods still in use—often exploited for credential theft.
These additions support faster, deeper compromise assessments and ensure security teams can respond more confidently to complex threats.
Learn more in the Knowledge Base page for MITRE ATT&CK Analyzer changelog
Fixes
Database Migration Performance Issue Resolved
This release addresses the migration performance issue introduced in AIR 4.37 during the transition from MongoDB to PostgreSQL. In certain environments, large volumes of timeline data caused increased database load, potentially leading to application unresponsiveness immediately after upgrade. This issue has now been fully resolved, so upgrades can now proceed as normal.
Flag Export Issue Resolved
We've fixed an issue that caused exported flag files to generate empty ZIP archives, even when multiple flags were selected. You can now export flags reliably for reporting and review.
AIR 4.37
8 April 2025
Important Notice: Database Migration
This is a major release that includes a database migration step. As a result, the upgrade process may take longer than usual.
To minimize disruption, we strongly recommend scheduling this upgrade outside of business hours. If you need assistance or have any concerns, please contact Binalyze Support before proceeding.
New Features and Enhancements
Bulk Task Cancellation and Deletion
Managing large volumes of tasks is now faster and more efficient with the introduction of Bulk Task Cancellation. This new capability allows users to cancel one or more tasks directly from the Tasking view using the familiar bulk action toolbar.
To help users narrow down which tasks to cancel, all advanced filters are fully supported, making it easier to locate and select specific task types, names, sources, or statuses. Once multiple tasks are selected, the bulk action bar will automatically appear, along with a task count to indicate how many have been selected for cancellation (note: this refers to the number of tasks, not assets).
As part of the same enhancement, we’ve also introduced Bulk Task Deletion. When using the Delete Tasks option in the bulk action bar, users can choose between:
-
Delete Task Only – Removes the task from the console without affecting the asset.
-
Delete and Purge Local Data – Deletes the task and purges any associated local data from the asset.
These enhancements streamline the cleanup of redundant or misconfigured task assignments, helping maintain a more organized and accurate tasking environment while offering greater control over retained data.
Read more about task cancellation and deletion here in the Knowledge Base.
Investigation Hub – Regex Support Added to Advanced Filters
The Investigation Hub now includes regex (regular expression) operator support within the Advanced Filters section. This enhancement enables more powerful and flexible data filtering across cases, triage results, and evidence views.
How It Works
Regex filtering is available via the existing Contains filter dropdown, with the following operator options:
-
Matches RegEx (case insensitive)
-
Does not match RegEx (case insensitive)
-
Matches RegEx (case sensitive)
-
Does not match RegEx (case sensitive)
These options allow you to create highly granular search conditions, ideal for forensic analysts dealing with variable or loosely structured data inputs.
Read more about RegEx in Advanced Filters here in the Knowledge Base.
Investigation Hub – Import Status Progress Display
Users can now monitor import progress directly within the Investigation Hub as the status is shown in real time next to the case title, providing immediate visibility into the current state of ongoing or newly added tasks.
When hovering over the data import icon, users will now see a clear visual status:
-
A green tick indicates that the import has successfully completed.
-
A spinning circle of dots signifies that the import is still in progress.
This small but impactful addition makes it easier to track case activity at a glance, helping investigators stay informed without switching views or refreshing pages.
Read more about the Secondary Menu here in the Knowledge Base.
Investigation Hub – Keyboard Navigation Now Refreshes Details Pane
We've added this ‘quality-of-life’ improvement to the AIR Investigation Hub based on customer feedback.
Previously, when navigating between artifacts in the center pane using keyboard arrows, the Details Pane did not update accordingly, requiring a manual click to refresh the content. We’ve now addressed this.
With this release:
-
The Details Pane now automatically refreshes when navigating through artifact line items using the keyboard arrow keys.
-
This behavior also applies when the details pane is detached in a separate window, ensuring a consistent experience across both views.
This enhancement makes artifact review faster and more intuitive—just the way it should be.
(Credit: Adam D, Josh T)
Investigation Hub – User Attribution for Individual Exclusions
We've enhanced the Individual Exclusions feature in the Investigation Hub by adding user attribution. Now, when a user manually excludes a Finding, their name is recorded and displayed in the Exclusion Table. This update brings greater transparency and auditability to the exclusion process.
Why it matters:Users can now easily identify who excluded specific findings—helping teams maintain accountability and better understand investigation decisions.
This builds on the original feature introduced in v4.35, which allowed analysts to exclude findings on a case-by-case basis without needing to define a rule.
Read more about Exclusions here in the Knowledge Base.
API Support for Creating Tags in Triage Rules
Users can now create and categorize triage rules using the public API. This new capability allows tags to be programmatically added during triage rule creation, eliminating the need for manual tagging and enabling more scalable, automated workflows.
Key Benefits:
-
Streamlines triage rule management via automation.
-
Enhances organization with consistent, tag-based categorization.
-
Reduces manual overhead in rule setup.
Binalyze MITRE ATT&CK Analyzer is now at version 9.0.1
Here is a summary of the releases since our last release notes, 5 March – 2 April 2025:
Version 9.0.1
-
Updated detection for SystemBC proxy malware.
-
Enhanced detection of Play ransomware variants and related tools.
-
Additional minor fixes and improvements.
Version 9.0.0
-
New YARA rules targeting China-based APT tools:
-
HUI Loader (S1097), ShadowPad (S0596), SodaMaster (S0627)
-
SparowDoor backdoor and ABYSSWORKER rootkit
-
-
Detection improvements for:
-
Credential theft, brute-force utilities, network discovery, and reverse proxy tools
-
Malware using compromised or revoked digital signatures
-
-
Dynamo has been updated to better recognize commonly used hacker tools in forensic artifacts.
Versions 8.7.0 – 8.7.1
-
Added detection for Winos, a C2 framework used in recent Taiwan-focused campaigns.
-
Improved coverage of ESXi-targeting ransomware variants.
-
New detection for Sosano, a backdoor aimed at aviation, satellite, and critical transport sectors.
These updates continue to strengthen Binalyze’s threat detection arsenal with broader coverage and enhanced forensic insight. For more details, visit the Binalyze MITRE ATT&CK Analyzer changelog.
Fixes
None of note
AIR 4.35
13 March 2025
New Features and Enhancements
Findings - Individual Exclusions
Previously, in the Investigation Hub, ‘Findings exclusions’ were limited to defined rules based on path and description. With this update, AIR now offers greater flexibility with two exclusion methods:
-
Exclusion Rules – The existing capability that excludes an item either only when found in a specific location or regardless of its location based on the finding itself.
-
Individual Exclusions – A new method that allows users to manually exclude any Findings within individual cases, based on their specific needs or investigation requirements without the need to create a rule.
This AIR v4.35 enhancement provides greater control and adaptability when managing exclusions in AIR.
Key Benefits: With this new enhancement, users can now:
-
Individually exclude items with no need for defined rules.
-
Easily view and manage these exclusions through the Exclusion Table in the Investigation Hub. Here the table will show if the exclusion is made by a rule or individual Finding.
-
Bulk removal of individual exclusions can be performed directly within the Exclusion Table.
-
Continue using rule-based exclusions alongside the new method for greater flexibility.
Read more about Exclusions here in the Knowledge Base.
Persistent Saved Filters for Asset Management
Managing large-scale asset inventories is now easier with the introduction of Persistent Saved Filters.
What’s New?
Previously, users could filter assets using preset filters (e.g., Managed Assets, Isolated Assets). However, these preset options were often insufficient for organizations handling thousands of assets, and custom filtering did not persist in the browser between sessions.
Key Benefits:
-
Save custom filters for frequently used asset searches.
-
Quickly apply saved filters to streamline asset management.
-
Take bulk actions or monitor asset status without re-entering the same filter conditions.
-
Use quick actions directly on saved filters for even faster asset selection.
Important Details:
-
Saved filters are ‘per-user’ – Users can only see and manage their own filters.
-
Preset filters remain unchanged – The existing predefined filters are still available.
-
Filters persist across sessions, allowing users to maintain their preferred filtering setup effortlessly.
This enhancement provides greater efficiency, ensuring that users can categorize and take action on assets more effectively.
Read more about using Persistent Saved Filters here in the Knowledge Base.
Bulk User Management Enhancements in Organization Settings
Managing users in Binalyze AIR just got easier! Previously, organization administrators had to remove users one by one, which was time-consuming, especially for large organizations.
Key Benefits:
We have introduced several improvements to streamline user management:
-
Bulk user removal – Select multiple users at once for removal.
-
One-click removal – Remove all users selected on a page in a single action.
-
Advanced user filtering – Filter users by email, username, and role on the Users page and organization settings.
-
Bulk user addition and removal – Easily manage large numbers of users by adding or removing them in bulk.
Why This Matters?
These improvements were developed in response to customer feedback, and mark a further step in enhancing user management efficiency in AIR. Administrators can now manage users more effectively, reducing manual work and improving overall operational efficiency.
Binalyze Tornado - updates and improvements
Version 1.0.12 (5 March 2025)
System Improvements
-
General enhancements to system stability and performance, ensuring a smoother and more reliable experience.
Version 1.0.11 (25 February 2025)
Microsoft 365 Collectors – Expanding forensic visibility in cloud environments:
-
Unified Audit Logs Collector – Added support for collecting Unified Audit Logs from Microsoft 365, providing a comprehensive audit trail for security investigations.
-
Risky Events Collector – Introduced a collector for risky users and risk detections, improving threat monitoring and security analytics.
-
MFA Configuration Status Collector – New collector to retrieve Multi-Factor Authentication (MFA) settings across all users in an organization, helping assess security configurations.
-
OAuth2 Permission Grants Collector – Implemented a collector to gather OAuth2 permission grants, offering better visibility into application permissions and access controls.
Binalyze MITRE ATT&CK Analyzer is now at version 8.6.3
These enhancements bring cutting-edge threat intelligence to your compromise assessments, allowing for faster and more accurate identification of advanced persistent threats (APTs), malware, and evasive attack techniques.
Expanded APT & Malware Threat Intelligence
-
New backdoor detections:
-
Sagerunex (Lotus Blossom APT) – Used against government, telecom, and media targets since 2012.
-
InvisibleFerret & BeaverTail (Lazarus APT) – Deployed in job scam attacks against developers.
-
LightSpy (APT41) – A Windows variant of the well-known espionage tool.
-
Sosano – Targeting organizations in aviation, satellite communications, and critical transport infrastructure.
-
Winos C2 framework – Recently used in attacks on Taiwan-based entities.
-
-
New Rust-based backdoor detection, actively targeting the cryptocurrency sector.
-
Gh0stRAT & FatalRAT updates – Strengthened detection of remote access trojans used in cyber-espionage.
Advanced Forensic Detection & Evasion Countermeasures
-
PowerShell & Scheduled Tasks Enhancements – Stronger identification of malicious command execution and obfuscated scripts.
-
Improved ransomware detection, including ESXi-focused variants and a macOS ransomware masquerading as LockBit.
-
New privilege escalation techniques tracked, such as the Truesight driver abuse used in large-scale defense evasion.
-
Enhanced detection of crypto wallet stealers, securing against browser extension-based threats.
Why This Matters for Your Compromise Assessments and Investigations
Stronger, Faster Threat Detection – Identify sophisticated APTs and malware variants with increased precision.
-
Better Forensic Visibility – Gain deeper insight into cross-platform threats and evasive attack techniques to guide investigations
-
Improved Security Posture – Strengthen defenses to protect high-value assets from emerging cyber threats.
For more details, visit the Binalyze MITRE ATT&CK Analyzer changelog.
Fixes
The following bug fix has been applied:
Asset Duplication Prevention: To prevent asset duplication, we have introduced a new validation mechanism. Assets now send a ‘responderId’ during both registration and visits, allowing the system to detect and block duplicate entries. This enhancement ensures better asset integrity and consistency in AIR.
AIR 4.33
12 February 2025
New Features and Enhancements
Dark Mode
A Dark Mode UI is now available in AIR. This feature provides a more comfortable and visually appealing experience, especially in low-light environments. It reduces eye strain during extended sessions and enhances usability while aligning with modern UI standards. Users can now switch between light and dark modes in the main AIR menu based on their preference, improving usability and overall satisfaction.
Data Usage Dashboard - Hierarchical Sunburst View
Understanding data usage in complex environments can be challenging, especially with large datasets. The new Hierarchical Sunburst View in the Data Usage Dashboard offers an intuitive, hierarchical visualization that makes it easier to identify key usage patterns, trends, and anomalies at a glance.
Key Benefits:
-
Clear, Visual Breakdown – Navigate data relationships more effectively than with traditional tables or linear charts.
-
Interactive Exploration – Click on segments to drill down into deeper data layers for detailed insights.
-
Consistent Filtering – All global filters apply to the Sunburst visualization for a seamless analysis experience.
-
Save to Dashboard – Easily save your customized Sunburst views for quick access and ongoing monitoring.
Where to Find It?
The Sunburst View is available under; Settings>Actual Disk Usage in the Hierarchical View tab on the Actual Usage page.
Read more about Disk and Data Usage here in the Knowledge Base.
Enhanced API Token Management with Role-Based Access Control
To improve security and flexibility, API Token Management now supports role-based access control (RBAC), reducing the need for excessive permissions.
Key Enhancements:
-
Global Admins continue to create and modify API tokens.
-
Granular Permissions: Tokens now inherit only the privileges of their assigned role (e.g., read-only or custom roles), preventing over-permissioning.
-
Post-Creation Role Updates: Token permissions can be modified after creation, allowing for dynamic access control.
-
Governance & Security:
-
The role assigned to a token and its creator cannot be deleted unless the token is reassigned or removed.
-
Improved auditability and compliance with least privilege principles.
-
The primary enhancement in this release is the revised role of the API token. Previously, API tokens were automatically assigned the Global Admin role, granting unrestricted access to all APIs. This update introduces role-based limitations, allowing API usage to be tailored according to the selected role. This improvement refines automation workflows and strengthens access control policies.
Event Subscription for Automated AIR Workflows
To enhance automation workflows, AIR now supports Event Subscriptions, allowing users to receive real-time notifications when specific events occur. Previously, while AIR actions could be triggered via API, there was no way to retrieve results automatically, requiring users to log in manually. This limitation made it occasionally challenging to integrate AIR with other tools for fully automated workflows.
Key Enhancements:
-
Event Subscription Mechanism: Users can subscribe to specific events in AIR and receive instant notifications.
-
HTTP Callbacks: When an event occurs, AIR sends a POST request with relevant event data to the user’s specified HTTP endpoint.
-
Seamless Automation: These triggers enable users to automate follow-up actions, such as initiating workflows in external tools.
-
Improved API Integration: Reduces the need for manual intervention, making end-to-end DFIR automation more efficient.
This update ensures that users can build fully automated incident response processes, improving efficiency and operational flexibility.
Read more about Event Subscription in the Knowledge Base.
Security Update for AIR Console Access Control
To address a security vulnerability involving Host header injection, we have implemented more stringent controls on AIR Console access.
Key Points:
-
Access Restriction: The AIR Console will now only be accessible through the specific address registered during the initial setup, ensuring that only legitimate requests are processed.
-
Technical Enforcement: This measure counters manipulations of the Host header that could potentially allow unauthorized access.
-
Configuration Flexibility: For legitimate access needs from multiple domains or IP addresses, users can specify allowable entries via the AIR_CONSOLE_ADDRESSES environment variable.
-
Enhanced Security: This change not only prevents unauthorized access but also aligns with best practices for secure network management.
This update enhances security protocols and provides administrators with better control over access settings.
AIR Responder Support in Windows Safe Mode
The Binalyze AIR Responder can now function in Safe Mode, allowing forensic acquisition even when a system is booted in a restricted state. To enable this functionality, users must register the Binalyze AIR Agent Service before entering Safe Mode.
Key Details:
-
If the machine enters Safe Mode with Networking, the AIR Console connection remains active.
-
Users must add the two Registry Keys before Safe Mode is active to allow tasking via the console.
-
Without these additions, interACT and remote tasking will not work until the Registry keys are added.
-
When using an off-network collector, users can perform acquisitions in Safe Mode without modifying the registry unless remote tasking is required.
Read more about AIR Responder in Windows Safe Mode here.
Binalyze MITRE ATT&CK Analyzer is now at version 8.5.0
Recent enhancements included:
Yara
Enhanced Detection Capabilities:
-
Deceptive Development Backdoor: Detection added for Lazarus APT group's custom backdoor targeting developers via fake job offers.
-
Veeam Credential Dumping Tools: Now detects tools extracting Veeam credentials from MSSQL databases, addressing technique T1555.
-
ValleyRAT Backdoor: Introduced detection for the ValleyRAT backdoor linked to the Silver Fox cybercrime group.
Dynamo
Forensic Analysis Enhancements:
-
Enhanced identification and analysis of hacking tools found during forensic investigations for more efficient threat assessment and response.
We have also implemented minor fixes and performance enhancements to improve system stability and detection accuracy, strengthening our security solutions against emerging threats and enhancing investigation processes.
For more details, visit the Binalyze MITRE ATT&CK Analyzer changelog.
AIR 4.31.5
29 January 2025
Hotfix
AIR version 4.31.5 fixes an issue with our LDAP integration where domain assets did not appear in the Assets section after starting a sync despite successful credential verification. This is fixed, please update to the latest version to see the domain assets correctly displayed.
AIR 4.31
15 January 2025
New Features and Enhancements
Investigation Hub Historical Disk Usage Statistics Dashboard
AIR version 4.29 introduced a comprehensive Disk Usage Dashboard in the Investigation Hub. This feature offers real-time, detailed insights into disk usage within the Investigation Hub, categorized by cases, organizations, and evidence types. Additionally, a new Historical Insights view has now been added, providing an enhanced perspective for trend analysis.
Key Benefits:
-
Granular Insights combined with Filters: View breakdowns by organization, case, evidence type, etc.
-
Improved Storage Management: Easily visualize data with pie charts and detailed tables.
-
Historical Views: Analyze trends over time.
-
Report Generation: Export insights as PDF reports for sharing or as CSV files directly from table views.
User Guidance:
-
Access: Available exclusively to Global Admins via the AIR console:
-
Navigate to: Settings > Investigation Hub Disk Usage > Actual Disk Usage or Historical Disk Usage.
-
-
Summary and Filters:
-
Total disk usage is summarized at a glance.
-
Filters include organization, investigation type, platform, evidence type, and category.
-
-
Visual Representation:
-
Pie charts highlight the top nine usage categories, with the remaining items visible via scrolling arrows.
-
This update enhances usability, supports trend analysis, and streamlines disk usage monitoring for better resource management. Read more in the Binalyze KB.
New Data Collectors
-
The following Browser based Data Collectors have been added:
-
Linux: Firefox Extensions
-
macOS: Chrome Extensions, Edge Extensions, Opera Extensions, Firefox extensions, DHCP Settings
-
Windows: Firefox Extensions
-
Tornado - Preview Version
We’re thrilled to announce the Tornado Preview, a standalone desktop application designed to streamline and enhance evidence collection from cloud platforms such as Google Workspace and Microsoft Office 365.
Tornado equips investigators with the tools to effortlessly gather critical artifacts, including email records, user access logs, and administrative actions—key elements for Business Email Compromise (BEC) investigations.
Key Highlights
-
Multi-Platform Support:
Tornado currently supports Google Workspace and Microsoft Office 365, with additional platforms planned for future releases. -
Advanced Collection Capabilities:
Gather essential data types such as email and activity logs across supported platforms. -
Investigation-Centric Design:
Tailored for BEC investigations with rapid evidence collection, optimized workflows, and enhanced incident response capabilities. -
User-Friendly Evidence Collection Interface:
Intuitive design ensures precise, efficient, and reliable evidence gathering. -
Data Analysis Options:
Export data to SQLite for detailed analysis, integrate seamlessly with Binalyze AIR and leverage the Investigation Hub for advanced use cases.
Availability
The Tornado Preview is:
-
For AIR Customers: Available alongside the release of AIR version 4.31 on January 15, 2025, via the Tornado Preview button in the AIR console.
-
For non-AIR customers: A dedicated landing page offers a free preview starting February 10, 2025. Early registration is available to join the mailing list and receive the download link.
For comprehensive details on Tornado’s features and usage, please visit our Knowledge Base.
Binalyze MITRE ATT&CK Analyzer is now at version 8.2.4
Recent enhancements included:
-
Added detection for malicious extensions involved in the Cyberhaven compromise and a broader campaign targeting Chrome extensions for credential-stealing purposes. Blog Post here.
For more details, visit the Binalyze MITRE ATT&CK Analyzer changelog.
AIR 4.29
12 December 2024
New Features and Enhancements
Investigation Hub Disk Usage Statistics Dashboard
-
Overview: AIR version 4.29 introduces a comprehensive Disk Usage dashboard in the Investigation Hub. This feature provides detailed, current insights into your AIR’s Investigation Hub disk usage across cases, organizations, and evidence categories, with a “historical insights” view planned for the next release.
-
Key Benefits:
-
Provides granular insights with breakdowns by organization, case, evidence type, and more.
-
Enhances storage management by simplifying visualization through pie charts and detailed tables.
-
Historical views are available for analysis trends (historical functionality to be added in upcoming releases).
-
Users can generate PDF reports for sharing and record-keeping, as well as export CSV files directly from the table views.
-
-
User Guidance:
-
Accessible exclusively to Global Admins via the AIR console; Settings > Investigation Hub Disk Usage > Actual Disk Usage or Historical Disk Usage
-
Total disk usage summary available at a glance.
-
Filters include organization, investigation type, platform, evidence type, and category.
-
Pie charts display the top nine usage categories, grouping the remainder under “Others.”
-
Clarifying Backward Compatibility in AIR 4.29+
Overview
With AIR 4.29, we introduced a major improvement: decoupling AIR console updates from Responder updates. This gives teams greater flexibility when deploying AIR updates, especially in large-scale environments.
-
What This Means (and What It Doesn’t)
-
Starting with AIR v4.29, the AIR console can be updated independently of Responder updates.
-
All future AIR versions (4.29 and onward) will maintain backward compatibility with Responders that are also on version 4.29 or newer.
-
Responders running versions older than 4.29 (e.g., 2.54.3) are not compatible with certain key features such as:
-
Evidence acquisition
-
Triage
-
interACT
-
Users with older Responder versions will see messages like:
To summarize:
Backward compatibility begins from version 4.29 onwards. If your Responders are still on versions earlier than 4.29, they must be upgraded at least once to benefit from this compatibility model going forward.
Why This Matters
Once all Responders are updated to v4.29+, you’ll no longer need to upgrade Responders with every new AIR console release — simplifying upgrades and reducing operational friction.
Binalyze MITRE ATT&CK Analyzer is now at version 8.1.0
Recent enhancements include:
-
GHOSTSPIDER detection: Added detection for Earth Estries APT's sophisticated backdoor activity. (T1059.003)
-
Driver exploitation identification: Enhanced detection of vulnerabilities like malicious Avast driver usage for defense evasion. (T1547.001)
-
Kernel exploit detection: Improved detection of STEALHOOK and CVE-2024-30088 kernel-level attacks, ensuring quicker response prioritization. (T1068)
-
Real-time threat identification: Live YARA and Sigma scanning now address advanced threats like Medusa ransomware with greater speed and precision.
For more details, visit the MITRE ATT&CK Analyzer changelog.
AIR 4.27.6
26 November 2024
AIR now provides configurable encryption for off-network collections. By default, encryption is disabled to streamline the post-collection ingestion process, enabling faster and more efficient evidence handling.
However, for scenarios requiring enhanced security, you can enable encryption during the setup of the off-network collector package. This ensures that sensitive data remains protected while giving you the flexibility to prioritize efficiency when needed.
We believe this update will improve your workflows while maintaining the highest level of security for your investigations.
For more details please see the Binalyze Knowledge Base page Off-Network Responder and please don’t hesitate to reach out to our team if you need further information.
AIR 4.27
11 November 2024
Enhancements
Support for Accounts in Azure AD SSO without Associated Email Addresses
New enhancements to SSO functionality in Binalyze AIR:
-
Editable Organization Details: SSO-authenticated users can now edit user organization details directly within the platform Settings page which will allow the alignment of individual organizations with separate AD groups, providing greater flexibility and improving usability.
-
Automated Azure/OKTA Integration: Organization information will now automatically synchronize from Azure Active Directory and OKTA groups, ensuring consistent, up-to-date user data without manual intervention.
Learn more about SSO integrations here in the Knowledge Base.
New Docker Log Data Collectors
-
Windows, Linux & macOS: Collect Docker Container Logs
-
Linux & macOS: Collect Docker Logs
Learn more about supported evidence and artifacts here in the Knowledge Base.
Binalyze MITRE ATT&CK Analyzer is now at version 7.2.0
Recent YARA enhancements include:
-
Added detection for BianLian ransomware. (T1486)
-
Enhanced identification of credential stealers that collect browser data. (T1005)
-
Enhanced detection of Cobalt Strike. (S0154)
-
Enhanced detection of memory dumpers and scripts designed to extract and decrypt Kerberos tickets. (T1558)
For a deeper dive into our MITRE ATT&CK Analyzer visit the changelog in the Binalyze Knowledge Base.
Fixes
The following bug fixes have been applied:
-
$mft CSV import column ordering issues.
-
Investigation Hub UI options were not always visible.
AIR 4.25.3
25 October 2024
Hotfix
Several issues have been addressed today with this Hotfix release two that may have affected costumes are outlined below:
1. Issue Addressed: interACT progress communication with AIR console (VOC-1472)
There was an issue in Responder v2.50.5 where certain interACT commands (get, put, zip, YARA, image) were missing progress information in the Console, though the commands still functioned properly. This is fixed in Responder v2.53.6.
2. Issue Addressed: Case Tasks missing (VOC-1463)
When navigating to a Case with multiple Acquisition, Triage, and InterACT records, the entries briefly appear but then disappear from the screen. This affects all data types, and even refreshing the page does not fix the issue. The count for each category (e.g., Acquisition: 45) also drops to zero unexpectedly.
Recommendations:
Update to AIR v4.25.3 when released to benefit from these improvements.
AIR 4.25
22 October 2024
Enhancements
Edit Scheduled Tasks
The new "Edit Scheduled Task" feature, gives users the flexibility to modify scheduled tasks without starting over. Now, you can easily add or remove assets from a scheduled task on the fly, saving time and improving workflow efficiency.
With the assets selected, the user can proceed to modify the scheduled task’s Setup, Customization, and Follow-up.
This update makes scheduled task management completely adaptable, ensuring a smoother and faster investigation process.
Use offline (off-network) acquisitions for comparison
Baseline analysis with the Compare feature is an innovative feature for proactive forensics and it is now enhanced to support collections from offline assets.
Compare identifies and highlights artifacts added, changed, or deleted between asset snapshots, even when the evidential acquisition occurred while the asset was offline. This proactive approach strengthens security by addressing vulnerabilities early.
Pre-validate Evidence Repository connection before initiating evidence collection
To improve task reliability and save time, we’ve introduced a connection check feature for evidence repositories when initiating acquisition tasks (both scheduled and immediate).
How It Works
When creating tasks such as Acquisition and Acquire Image, if an evidence repository (SFTP, FTPS, Azure, or AWS) is selected, the AIR console will now automatically perform a connection check to ensure the repository is accessible.
If the connection check takes longer than 10 seconds, the check will be canceled, and a warning message will appear, but the task creation will not be blocked.
Users can choose to proceed with the task, even if the repository is temporarily inaccessible, or cancel the task creation.
The connection check does not apply to SMB repositories at this time.
Expanded Color Palette for Custom Flags
Flagging evidence items in AIR has been a popular feature, allowing users to easily categorize and prioritize key findings in the Investigation Hub. However, customers have requested more flexibility with color options for better organization, especially in complex investigations.
We’ve listened! You can now choose any color from a palette for your custom flags. This enhancement gives you more control, enabling better visual distinction of flagged items and improving workflow efficiency. Tailor your flagging system to fit your needs and manage investigations with greater clarity and precision.
Event Log collections now support date configuration for timezone offsets
The new event log collection wizard, introduced with AIR v4.23, has been a great success with users, and we've now enhanced it further by adding the option to select a time zone for collections.
The asset’s browser time zone setting will be used if no time zone is selected.
New Browser Extension Data Collectors
We have expanded the evidence-collection capabilities in AIR by adding several new browser extension collectors for Windows:
-
Edge Extensions
-
Opera Extensions
-
Brave Extensions
-
Vivaldi Extensions
-
QQ Extensions
Binalyze MITRE ATT&CK Analyzer is now at version 7.1.0 (18/10/24)
Recent YARA enhancements include:
-
Added detection for DragonForce ransomware binaries. (T1486)
-
Added detection for Angry IP Scanner. (T1018)
-
Added detection for Clop and MedusaLocker ransomware binaries observed in September 2024. (TA0040)
-
Enhanced detection of Defender Control hack tool often used to disable Microsoft Defender. (T1562.001)
-
Added detection for HRSword, which threat actors use for defense evasion. (T1562)
-
Multiple minor FP fixes and performance improvements.
-
Added detection for Bugsleep backdoor attributed to Iranian MuddyWater threat actor.
For a deeper dive into our MITRE ATT&CK Analyzer visit the changelog in the Binalyze Knowledge Base.
Fixes
The following bug fixes have been applied:
-
The acquisition reports icon was not always displayed in the AIR Console UI.
-
Exporting Flags resulted in errors in some instances.
-
Searching in the Investigation Hub was not always displaying the resultant hits.
-
Scheduled tasks in some cases launched before the correct start date/time.
AIR 4.23.3
25 September 2024
Hotfix
This hotfix addresses the following issues:
-
FSEvents Collection: The macOS Artifact Collection - FSEvents was not providing complete event data in the Investigation Hub. We have improved collection and removed the 3-day limit, ensuring all events are now captured.
-
Incorrect Asset Status: Assets were incorrectly marked as ‘Offline’ when they were actually ‘Online’. The fix ensures real-time and accurate status updates.
-
Report Viewing Issue: Users were unable to properly view reports in the Investigation Hub. The issue has been resolved, ensuring full access to reports.
-
Event ID Description Error: In the Investigation Hub, the description for every Event ID was incorrectly showing as "Windows is starting up". This issue has been resolved, and the correct descriptions are now displayed.
Recommendation: Apply the latest update to benefit from these fixes.
AIR 4.23
23 September 2024
Enhancements
New Improved Windows Event Log Collections
AIR v4.23 introduces a flexible and customizable event log collection feature, enabling users to collect event records in a fully configurable way by specifying channels, event IDs, and collection parameters.
Users can now:
-
Define specific channels for event log collection.
-
Select specific event IDs or add custom event IDs.
-
Set parameters such as:
-
Number of records to collect.
-
Date ranges for event log collection.
-
How It Works:
An “Event Log Records” configuration tab has been added to the “New Acquisition Profile” wizard in AIR. Users can enable this feature via the toggle switch and:
-
Select predefined event IDs from a list of over 200 of the most commonly used DFIR event IDs, or
-
Manually input custom channel IDs and event IDs of their choice using the “Add New Event Type” option.
Once configured, the new Acquisition Profile with Event Log Records settings can be saved to the AIR Acquisition Profiles library for future use. When running an Acquisition Profile that includes Event Log Records, users can select the profile and choose from two additional task options:
-
“Collect last N records”: The system will collect the specified number (N) of the most recent records for each event ID selected.
-
“Collect records between start and end dates”: This allows users to capture logs within a specific time range. (Note: This option is not available for scheduled acquisitions.)
These enhancements empower users to gather only the most relevant event logs for their investigations, significantly reducing the manual effort involved and ensuring critical events are not overlooked.
Fine-tuned and enhanced AIR’s Sigma engine
Significant backend improvements have successfully reduced unwanted noise and false positive findings by approximately 40%. Our efforts continue, with future releases aimed at reducing unwanted findings by 70-80%, enabling analysts to focus more quickly and efficiently on the most critical events.
Scan Local Drives Only Feature for triage tasks
The "Scan Local Drives Only" feature improves triage efficiency by focusing scans on local drives, excluding data from external or network drives.
-
Available for all AIR-supported operating systems.
-
Disabled by default but can be enabled as an organizational policy.
-
Also configurable by selecting the custom options during individual triage task creation.
This feature ensures faster, more focused scans by reducing unnecessary data collection.
Keyword-List Files can be added to DRONE searches
This release introduces the ability to upload keyword lists for the DRONE search capability, allowing users to efficiently search through data within their collections.
-
There is no character limit for keyword lists; the file size limit is 1 MB.
-
Each keyword must be on a new line.
-
Keyword searches operate only on data within the Case.db, not within CSV files.
-
Keyword search is extended to event log data, which is collected by the following Sigma analyzers:
-
Windows: Event Record Analyzer
-
Linux: Syslog Analyzer
-
macOS: Audit Event Analyzer
-
This feature enhances the search capabilities within the DRONE module, offering more flexibility and precision.
Investigation Hub Real-Time Disk Usage Visibility
This feature provides real-time visibility into disk space usage, allowing investigators to easily track storage utilization for both Cases and individual Tasking Assignments on the AIR database server (not assets or evidence repositories):
-
On the AIR Cases page, a new column shows the total space occupied by collections across all assets in a case.
-
In the Task Details window, the space occupied by each specific task assignment is now displayed.
These enhancements help investigators manage storage efficiently and prevent overloading environments, ensuring optimal performance.
Azure Blob supports image files for use in AIR’s File Explorer
Many customers store their evidence collections and forensic image files in Azure Blob Storage but until now AIR File Explorer could not access these image files to present (mount) them for investigation in the AIR console.
VHD and VHDX disk image support in AIR File Explorer
Investigators can now use the AIR File Explorer feature to create assets from VHD and VHDX disk images. You can then browse through files and folders within VHD and VHDX files.
This complements the functionality we already have for RAW, E01 Ex01, and VMDK disk image files. Please read more in our File Explorer FAQ’s.
Fixes
-
No notable issues, aside from those related to overall speed and performance.
AIR 4.21
21 August 2024
Enhancements
We have expanded the evidence-collection capabilities in Binalyze AIR by adding several new browser-related items for Linux, macOS, and Windows:
For Linux, we now collect:
-
Browser Bookmarks (Chromium, Edge, Opera, Vivaldi, Brave)
-
Browser User Profiles (Chromium, Edge, Opera, Vivaldi, Brave)
-
Browser Local Storage (Chromium, Edge, Opera, Vivaldi, Brave)
-
Dump Browser Indexed DB (Chromium, Edge, Opera, Vivaldi, Brave)
-
Browser Web Storage (Chromium, Edge, Opera, Vivaldi, Brave)
For macOS, the following items have been added:
-
Browser Bookmarks (Edge, Opera, Vivaldi, Arc, Brave, QQ)
-
Browser User Profiles (Edge, Opera, Vivaldi, Arc, Brave, QQ)
-
Browser Local Storage (Edge, Opera, Vivaldi, Arc, Brave, QQ)
-
Dump Browser Indexed DB (Edge, Opera, Vivaldi, Arc, Brave, QQ)
-
Browser Web Storage (Edge, Opera, Vivaldi, Arc, Brave, QQ)
For Windows, we now collect:
-
Browser Bookmarks (Edge, Opera, Vivaldi, Brave, QQ)
-
Browser User Profiles (Edge, Opera, Vivaldi, Brave, QQ)
-
Browser Local Storage (Edge, Opera, Vivaldi, Brave, QQ)
-
Dump Browser Indexed DB (Edge, Opera, Vivaldi, Brave, QQ)
-
Browser Web Storage (Edge, Opera, Vivaldi, Brave, QQ)
We have also further enhanced evidence collection capability by adding a new artifact group for Windows focused on Docker.
The new "Docker" group includes the following items for collection:
-
Docker Changes
-
Docker Containers
-
Docker Image History
-
Docker Images
-
Docker Info
-
Docker Networks
-
Docker Processes
-
Docker Volumes
This addition ensures that Docker-related artifacts can now be collected and analyzed from Windows systems, further extending the capabilities of Binalyze AIR for environments leveraging containerization.
For a full list of the evidence and artifacts supported by AIR please visit our Knowledge Base.
Security
2FA for LDAP users from account settings
-
You can enable 2FA for LDAP users even if 2FA is enforced for all users, and now you can configure 2FA for LDAP users directly from account settings.
Fixes
-
Fixed: Repeat Mechanism in Schedule Task for Case Selection
-
A fix has been applied for the issue that arose when the user selected 'Case' after configuring the ‘repeat’ option in the Schedule Task settings, the repeat mechanism did not function as expected.
-
-
Fixed: 'Select All' in Case Includes Only Case Assets
-
A fix has been applied for the issue that arose when selecting all assets from a case as it included all assets from the organization rather than only those within the case when 'select all records' was chosen. (Credit: Mustafa D)
-
-
Fixed: Potential PostgreSQL CVE-2024-7348 Vulnerability in AIR
-
We have resolved the PostgreSQL security vulnerability detailed in CVE-2024-7348 within Binalyze AIR. This vulnerability could potentially allow unauthorized access or data leakage due to improper handling of database permissions in PostgreSQL. Our update addresses this issue, ensuring that our platform remains secure and your data is fully protected. This fix reflects our commitment to maintaining the highest security standards in AIR.
-
AIR 4.19
7 August 2024
Features
VMDK support in AIR File Explorer
-
Investigators can now use the AIR File Explorer feature to create assets from VMDK disk images. You can then browse through files and folders within VMDK files. This functionality is available regardless of whether the images are segmented or contained in a single file.
-
This complements the functionality we already have for RAW, E01 and Ex01 image files. Please read more in our File Explorer FAQ’s.
AWS S3 bucket support in AIR File Explorer
-
Many customers store their evidence collections and forensic image files in AWS S3 and until now AIR File Explorer could not access these image files to present (mount) them for investigation in the AIR console.
-
This complements the functionality we already have for RAW, E01 and Ex01 image files. Please read more in our File Explorer FAQ’s.
Enhancements
Investigation Hub
The Investigation Hub in AIR continues to evolve at pace, offering enhanced workflows with comprehensive insights and collaborative tools. New features include a detachable evidence details window that can be resized and repositioned for improved clarity. The addition of fullscreen evidence tables and sticky column headings ensures efficient case management and significantly boosts productivity across all investigative activities:
-
Detachable Evidence Details Window
-
Allows users to detach the evidence details window into a standalone window, providing flexibility to place it anywhere on the screen(s) for improved clarity.
-
This window can be reshaped and resized to the user's preference, maintaining its form even when displaying new evidence items.
-
Clicking on a new row in the table will update the detached details view to match the newly selected item.
-
-
Fullscreen window for evidence tables
-
Users can now ‘go full-screen’ with their evidence tables, which is especially valuable for large, multi-column data sets.
-
-
Sticky column headings are saved in the Investigation Hub
-
Both column selection and position will remain saved/static within your browser for all user-based AIR sessions, even if you log out, unless you choose to clear your browser cookies.
-
New AIR audit log retention policy
-
AIR v4.19 introduces a new AIR audit log retention policy aimed at optimizing platform performance and data management. Users are encouraged to back up their audit logs regularly to ensure no loss of data.
-
With AIR v.4.19 and later, all AIR audit logs are saved to PostgreSQL and retained for 3 months after which they are deleted.
-
Please see this KB page to learn more.
Frank.AI Copilot configuration (Credit: James W)
-
Users can now choose to switch Frank.AI on or off from the AIR ‘Settings > Features’ page.
-
Frank.AI is active by default. You can learn more about it and our future development plans here in the Knowledge Base.
Binalyze MITRE ATT&CK Analyzer has been updated to version 6.3.0 (07/08/24)
Yara enhancements include:
-
Added detection for IOCs linked to North Korean Lazarus/Andrariel groups (G0032, G0138).
-
Added detection for APT group StormBamboo/Evasive Panda.
-
Improved detection of shellcode loaders.
-
Added detection for the SharpSploit post-exploitation tool.
-
Added detection for the open-source Lilith RAT (T1219).
-
Improved detection of Metasploit implants for Linux.
-
Added detection for Java-based STRRAT and related IOCs.
-
Other minor fixes and improvements.
-
For details please see the changelog in the Binalyze KB.
In addition to the updates listed above, we have fixed several minor issues and made improvements to enhance performance and user experience.
AIR 4.17.9
25 July 2024
Hotfix
This hotfix improves database migration stability by addressing data inconsistencies in investigation activities (comments, notes, etc.). This version aims to minimize potential migration issues.
AIR 4.17
11 July 2024
Features
EWF2 (Expert Witness Format 2) support
-
AIR now supports the creation of forensic disk and volume images in the EWF2 format. These images can be directly uploaded to your AIR Evidence Repositories.
-
EWF2 is commonly used in digital forensics to store and compress digital evidence and the format supports the inclusion of metadata.
-
Investigators can now use the AIR File Explorer feature to create assets from EWF disk images. You can then browse through files and folders within both E01 and Ex01 formats. This functionality is available regardless of whether the images are segmented or contained in a single file.
-
This compliments the functionality we alread have for RAW image files. Please read more in our File Explorer FAQ’s.
New Browser Data Collectors:
-
Thumbnails: Now includes support for Vivaldi, Brave, Chromium, Opera, Edge, QQ, and Arc.
-
Form History: Collect form history data from Vivaldi, Brave, Chromium, Opera, Edge, QQ, and Arc.
-
Cookies: Enhanced cookie collection capabilities for Vivaldi, Brave, Chromium, Opera, Edge, QQ, and Arc.
-
Favicons: Collect favicons from Vivaldi, Brave, Chromium, Opera, Edge, QQ, and Arc.
New ESXi Collectors:
-
Cross Active Connections: Monitor and collect data on active connections.
-
Datastores: Gather information from ESXi datastores.
-
Hardware Clock: Access and collect hardware clock settings.
-
Networks: Collect detailed network configuration and activity data.
-
VMware Version: Track and collect information on the VMware software version.
Enhancements
Investigation Hub
The Investigation Hub in AIR is the central point for all your investigations, enhancing workflows with comprehensive insights and collaborative tools. It includes advanced search options and a new dynamic filter, making it essential for efficient case management and boosting productivity across investigative activities.
-
New Evidence Category for ‘Other Evidence’, these items being Findings without an Evidence Category in AIR
-
This enhances the clarity of the Findings displayed to users. Previously, some findings identified by the DRONE did not correspond to any of the available evidence categories.
-
With this change, all findings without a specific category will be grouped under 'Other Evidence'. This ensures every finding is allocated an evidence record within a category, allowing the total count of findings on the Investigation dashboard to accurately match the number shown in the evidence list.
-
-
New filter option for flagged items
-
Users can now use the advanced filter to include or exclude flagged items in the Investigation Hub table views, enhancing the ability to focus on prioritized or highlighted evidence.
-
-
Windows FAT file system support
-
AIR now supports the FAT filesystem, expanding our compatibility for logical imaging with ext4, ext3, and NTFS file systems.
-
-
Nested Asset Tagging
-
Nested Tagging has been added for your Assets, providing tag grouping for the organization of assets. This new feature allows for a more structured and detailed structuring of assets within AIR, making navigating the more complex network structures easier.
-
To create a nested tag, go to the Asset Info page and use a colon (:) to separate each level of the hierarchy. For deeper nesting, simply add additional colons between each subsequent tag level:
-
Fixes
-
Cross-Site Scripting (XSS) Vulnerability Patched
-
We have addressed and resolved a critical vulnerability that allowed attackers to potentially take over accounts through Cross-Site Scripting (XSS) in compromised hosts. This fix significantly strengthens the security of our system against unauthorized access.
-
AIR 4.15.4
24 June 2024
Hotfix
Today we released a hotfix that provides a Responder update to solve tactical incompatibility issues with other security products.
AIR 4.15.3
11 June 2024
Hotfix
Issue Addressed:
In the AIR Investigation Hub, a materialized view in the PostgreSQL database related to exclusion and finding relations was identified as the root cause of performance degradation. This view was being refreshed every time a field within it was updated. Due to the resource-intensive nature of this refresh transaction, frequent updates often caused database-level deadlocks. These deadlocks, in turn, slowed down the database and degraded application performance.
Impact:
The issue does not necessarily affect all customers uniformly. The likelihood of encountering performance problems depended on the number of assets being managed, the volume of investigations being actively conducted, and the frequency of asset name changes. Consequently, while some customers have experienced performance issues, others did not.
Resolution:
We have today implemented a hotfix to optimize the refresh process for the materialized view, reducing the likelihood of deadlocks and improving overall database and application performance.
Recommendations:
Customers experiencing performance issues are advised to apply this hotfix to benefit from the optimizations. For further assistance, please contact our team via; support@binalyze.com
AIR 4.15
4 June 2024
Features
Investigation Hub - New Features
The Investigation Hub in AIR is the central point for initiating and concluding all your investigations. As the core of AIR, it enhances your investigative process by integrating comprehensive insights and prioritized data with robust collaboration features. Equipped with advanced navigation features like sophisticated search options and dynamic filters, the Investigation Hub is indispensable for smooth and efficient case management, boosting productivity and connecting all investigative activities seamlessly.
New Activity Feed
-
The Activity Feed enhances team collaboration and transparency by logging actions taken by investigators. This includes creating; exclusions, findings, flags, comments, and notes. Each entry includes user identification and timestamp information to ensure a comprehensive audit trail.
-
All of the activities are labeled and linked to the individual activity simply by clicking on it. In the example below we can see how Comment Added, Note Added, Flag Added, and Exclusion Rule Created have all been tracked as activities
Add Comment to evidence
-
Comments enhance communication by allowing analysts to directly comment on findings or/and tag relevant colleagues. This ensures that all discussions are captured and documented within the activity feed, promoting effective collaboration and transparent activity tracking.
-
Right-click on an item and select ‘Comment’ to attach your comment to that item.
Event Logs View and Filtering Improvements
-
To manage the extensive data from Event Logs, we've introduced a Column Chooser feature. This allows users to customize their view by selecting specific data fields from the Details view that they want to display in columns. This makes it easier to sort, filter, and analyze the desired relevant log data.
Search Options for selected text
-
Users can highlight text within tables and instantly search for it within the same table, across the entire Investigation Hub, or externally on Google or VirusTotal. This feature streamlines the research process and eliminates the need to toggle between different platforms.
Away from the Investigation Hub other new features include:
Tagging added to Triage Rules
-
Triage rules in the AIR console can now be associated with Tags, which help in organizing rules and filtering when required. This enhancement aids in managing the rules more efficiently and allows for streamlined searches and better organization within the console.
-
When creating a Triage Rule the UI allows the user to filter existing rules by their associated Tags.
-
The Triage Rule Library now includes Preset Filters in the secondary menu, allowing users to organize rules hierarchically.
ESXi parser added
-
The ESXi parser has been added to the AIR platform, allowing for the import of tasks from off-network ESXi collectors and their presentation in the Investigation Hub.
-
Learn more about our ESXi collector here.
Enhancements
Binalyze MITRE ATT&CK Analyzer has been updated to version 5.3.1 (31/05/24)
-
For details please see the changelog in the Binalyze KB.
Expose more action buttons on the Asset Info page
-
Additional Action Buttons have been introduced to the Asset page to improve usability and immediate access to the most commonly selected actions.
Improvements to the Details view
-
Each item's title is displayed in light grey text, making the more critical information in darker text stand out for easier reading and quick reference.
-
The "Show or Hide Empty Fields" view option helps to declutter the display by allowing users to hide fields that contain no data, thus reducing visual noise and focusing attention on fields with relevant information.
Advanced Filter improvements
-
The advanced filter save feature boosts efficiency by enabling users to save and share custom filters within an AIR organization. This functionality streamlines data analysis, promotes consistency, and enhances collaboration throughout the investigative process.
-
The Advanced Filter window remains visible as you build the filter and you can reposition it.
-
Each Advanced Filter is specific to the table it is built in eg; an advanced filter you build in Findings will not be available to you in the Browser Artifact table.
-
Filters can be saved and then later selected from the drop-down list.
-
Add items to Advanced Filters directly from the Details window using the filter icon.
Fixes
-
Timeline date/time picker bug is fixed
AIR 4.13
9 May 2024
Features
Investigation Hub - New Features
The Investigation Hub has been updated with a new look and feel, now aligned with the rest of AIR to provide a consistent navigation experience. It also features enhanced and new features, as well as improved overall performance.
-
New Dashboard & Widgets
-
Global search with tabbed search for AIR or the Investigation Hub
-
Export user-generated flags to .csv
-
Clickable Finding Types for new re-mapped 4 severity levels:
-
High
-
Medium
-
Low
-
Matched
-
-
New user-generated Flags widget
-
-
New Secondary Menu with the ability to:
-
Search for evidence in the comprehensive categories listings
-
Hide empty pages, and categories with no return
-
Show only evidence with Findings
-
Show only the evidence with flags
-
-
Global Filters for:
-
Assets including the ability to filter by individual taskings
-
Finding Types; High, Medium, Low, and Matched
-
Flags
-
Dates & Times via a ‘picker’ and some presets
-
Created By
-
-
New table layout and functionality:
-
Introducing a Flags column
-
Column header searching and filtering
-
Column header date & time ‘picker’
-
Dockable Details pane, horizontal, vertical, or minimized
-
Flags
-
It is now possible to create custom flags by right-clicking on an evidence item, selecting ‘Add/Remove Flag’, and then creating a name, description, and color for your Flag.
-
Select multiple items to perform Bulk Flagging operation.
-
Flags are saved at the Organization level in Libraries
User-generated Findings
-
AIR 4.13 has added user-generated Findings to complement AIR’s DRONE Findings
-
Right-clicking on an evidence item will allow users to allocate a Finding to the item
-
Exclusions
-
It is now possible to select any evidence items from your Findings for exclusion.
-
Three options:
-
Right-click on a Finding and select ‘Exclude’
-
Select the ellipsis at the end of the row
-
Bulk Actions will allow you to exclude more than one item at a time
-
-
The Exclusion Rule allows you to exclude by:
-
Path or Finding
-
For the Case or whole Organization
-
For selected assets or all assets in the case
-
Notes
-
Notes can now be added to every evidence item - the item does not have to be bookmarked to have a note attached.
-
The new table view now has a Notes column for all items
-
Notes can be included in your reports
Improved Reports
-
The new flagging capability in the Investigation Hub improves reporting by enabling users to include specific Findings and further filter by individual Flags for a more targeted output:
-
This enhanced granularity extends to the next step of report generation, where users can now add and filter non-finding evidence items by Flags for even more precise reporting:
-
Reports can be managed, edited, generated, exported, and deleted from the Reports tab in the Secondary Menu.
-
For more information about the Investigation Hub please visit our Knowledge Base:
Away from the Investigation Hub other new features include:
-
New Windows, macOS, and Linux evidence types:
-
Edge Sessions
-
Opera Sessions
-
Brave Sessions
-
Vivaldi Sessions
-
-
New Windows evidence types:
-
Powershell ConsoleHost History
-
QQ Sessions
-
-
New macOS evidence type:
-
QQ Sessions
-
Arc Sessions
-
-
New Linux evidence type:
-
Chromium
-
-
A full list of the 500+ items now supported in AIR is available in the Knowledge Base.
-
osquery can be added to an Acquisition Profile
-
A new "osquery" tab has been added to the acquisition profiles for each supported OS, enabling users to enhance evidence collection by incorporating osquery capabilities into their evidential acquisitions.
-
NB: This unique feature allows users to send data collected via osquery directly to a timeline, an option not available in previous osquery implementations for triage.
-
-
AIR Isolation ‘allow’ lists
-
Users can now specify a list of pre-approved processes, IP addresses, and ports that remain active on an isolated asset. This ensures that essential services and connections, such as EDR, continue uninterrupted, supporting ongoing SOC processes.
-
Enhancements
-
Binalyze MITRE ATT&CK Analyzer has been updated to version 5.0.1
-
For details please see the changelog in the Binalyze KB.
-
-
User Privileges for Task Scheduling:
-
AIR administrators can now restrict users from scheduling tasks or editing existing ones:
-
Schedule Task: Enables users to "Schedule for later." Without this privilege, this option is disabled, and a tooltip explains the restriction.
-
Update Scheduled Task: Allows users to edit scheduled tasks. If this privilege is not granted, the "Edit" button is disabled with an explanatory tooltip.
-
-
-
Scheduling options for responder updates
-
New scheduling options for responder updates to streamline the process, ensuring that updates do not disrupt ongoing investigations.
-
Scheduled Manual Updates: Users can now schedule updates for a specific time for an individual asset or a group of assets. Setting a new update time for an asset will override any previously scheduled time for that asset.
-
Scheduled Auto Updates: Users can establish a recurring schedule to automatically check for and apply updates within a designated timeframe.
-
-
-
File Explorer - Calculate Hash for disk images
-
When a disk image is added as an asset to AIR, users can now calculate the hash value of that image file either through the Asset Actions button or from the Disk Image Details window.
-
MD5, SHA1 and SHA256 are all calculated simultaneously.
-
This hash function can be carried out at any time.
-
-
File Explorer - Recursive Search
-
Recursive searching is now possible in the AIR File Explorer via the Global Search box where the File Explorer tab will display any hits found in the File Explorer.
-
Fixes
-
Timeline date filtering issue has been fixed (Credit: Josh T)
-
Column widths changing automatically with no user interaction has been fixed. (Credit: Guo Y)
-
Off-line users Windows Registry data will now be parsed (Credit: Mark CD)
AIR 4.11
2 April 2024
Features
-
Introducing Frank.AI, your investigation copilot
-
Frank is an AI Assistant designed to enhance forensic investigations within the AIR console. Frank.AI offers instant forensic assistance across all console pages, for example, providing insights, without leaving AIR, on subjects such as YARA, Sigma, and Osquery rule writing.
-
In this preview version, Frank leverages the ChatGPT API without additional fine-tuning, setting the stage for future enhancements. Future updates aim to expand Frank's capabilities through Retrieval Augmented Generation (RAG) for accessing broader data sources and deeper integration with the AIR ecosystem, including direct data retrieval from the AIR database and collaborative analysis with the AIR's AI module for advanced insights, such as anomaly detection and behavioral correlations.
-
You can reposition, resize, and minimize it just like any standard window, ensuring it fits seamlessly into your workflow without obstructing your view.
-
There are no additional domain requirements as Frank.AI is hosted on one.binalyze.com.
-
Stay tuned for evolving features and improvements based on user feedback.
-
-
New evidence types:
-
Parse LNK Files
-
Collect LNK Files
-
Systemctl Services
Browser evidence types across Windows, Linux and macOS
-
Chrome Sessions
-
Chrome Login Data
-
Chrome Local Storage
-
Chrome IndexedDB
-
Chrome Web Storage
-
Chrome Form History
-
Chrome Thumbnails
-
Chrome Favicons
-
Default Browser
-
Firefox Cookies
-
A full list of the 584 items now supported in AIR is available in the Knowledge Base.
Enhancements
-
Binalyze MITRE ATT&CK Analyzer has been updated to version 4.3.1
-
For details please see the changelog in the Binalyze KB.
-
-
Disk imaging errors reported in metadata.yml
-
AIR’s disk or volume imaging feature produces a file that captures the metadata related to the imaging process. This now includes a log of any errors encountered, which are documented within the metadata.yml file for comprehensive tracking and analysis. (Credit: Charlotte H)
-
Please see this KB article for a full explanation.
-
-
Scheduling Based on Asset Timezone
-
AIR now enables users to schedule tasks according to the asset's local time zone. This ensures that tasks are executed at the specified time relative to each asset's geographical location, allowing for synchronized operations across different time zones. For example, when choosing this option, instructing the system to perform a task at 01:00 will result in the task being carried out at 01:00 in the local time of each asset, regardless of their global positions. (Credit: Ramesh P)
-
Please see this KB article for more information.
-
-
Auto Asset Tagging Rules: New wizard and Organizational Saving
-
The new Auto Asset Tagging (AAT) wizard allows rules to be saved specifically for individual organizations or universally across all organizations. This enhancement supports users in creating and applying incident-specific AATs selectively, avoiding unnecessary use or exposure of a rule outside the intended organizational context. (Credit: Caleb T)
-
Please read this Auto Asset Tagging KB page for more information.
-
-
AIR version information is again displayed in the main menu
-
The AIR console version number has returned to the main menu to stop users from having to locate it on the settings page.
-
Fixes
-
A timestamp issue with the Event log content has been fixed. (Credit: Jon F, Grant O and Ben H)
-
Some incorrect "Match Counts" under the "Case Triages" Page have been resolved.
-
In previous versions, AIR displayed the "KeyLastWriteTime" in the evidential Amcache CSV files in local time instead of UTC. This has now been corrected to show times in UTC, ensuring consistency and accuracy. (Credit: Guo Y)
-
Tornado, crucial for AIR's File Explorer integration, retries registration until successful. A bug affecting success confirmation was fixed, enhancing reliability. (Credit: Nuno P)
AIR 4.9
7 March 2024
Features
-
New Task Scheduling capability integrated into the AIR tasking wizard.
-
Investigators can now use the tasking wizard to schedule the following activities:
-
Evidence collections.
-
Triage/Threat Hunting. (Credit: Turgut Ö)
-
Disk and Volume Imaging.
-
Auto Asset Tagging.
-
-
Scheduled tasks can be assigned to a Case.
-
The timezone for task execution can be adjusted.
-
The recurrence rate can be set to Daily, Weekly, or Monthly.
-
The sequence can be stopped at a particular date and time or after a defined number of occurrences.
-
-
New Windows evidence type
-
AIR now parses the Window $USN Journal and saves this file to the evidence repository as a .csv file for easy analysis (Credit: David C)
-
Enhancements
-
ESXi collections
-
We have extended the list of what we collect from ESXi from 10 to 100 items. For the full list please visit the Binalyze KB (Credit: Guo Y)
-
-
MacOS Agent - Full Disk Access requests
-
When installing an AIR responder on a T2 or later Mac, Full Disk Access is required for it to have the necessary permissions for all AIR collection types. AIR’s responder will now display a message to advise the installer to:
-
Open System Settings -> Privacy & Security -> Full Disk Access to grant permission to ”air”.
-
The user will need to toggle the switch 'on' to enable Full Disk Access for the AIR responder. (Credit: Caleb T)
-
-
-
Auto Asset Tagging Rules added to Task Details
-
Users can now see in the Task Details window, the Auto Asset Tag(AAT) rules which were checked during individual AAT task assignments.
-
Binalyze MITRE ATT&CK Analyzer has seen the following updates since the last release of AIR: 4.1.0, 4.2.0, 4.2.1, 4.2.2 and 4.2.3.
For details please see the changelog in the Binalyze KB.
Fixes
-
Bulk Action Bar re-sized and re-positioned
-
The new size and location of the Bulk Action Bar means that it no longer interferes with other information displayed in the UI. (Credit: David C)
-
AIR 4.8.1
20 February 2024
Hotfix
-
Attention to users of AIR 4.8.0: Some users may experience difficulty logging into AIRConsole. This issue affects only users assigned to specific organizations (but not those who select “All” organizations).
Please see the example below for reference.
In version 4.8.1, we have addressed and resolved this issue. We recommend all customers currently using AIR 4.8.0 to upgrade to AIR 4.8.1 at your earliest convenience
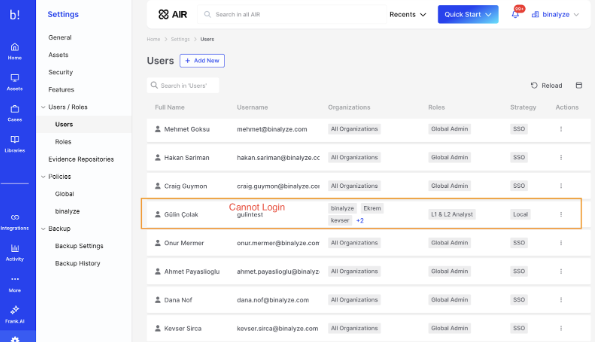
AIR 4.8
14 February 2024
In AIR version 4.7 and above, we've added a new Docker container specifically for enabling the new File Explorer feature in AIR. If you're not interested in using File Explorer, you can proceed with the upgrade as usual. However, if you do wish to utilize the File Explorer and haven't received assistance with migration yet, please reach out to our support team for guidance on updating to either version 4.7+. Kindly note that contacting our support team is only necessary if you intend to activate the File Explorer feature.
Enhancements
-
Isolate multiple assets simultaneously
-
Users now have the capability to select multiple assets simultaneously and execute bulk actions to isolate any desired number of assets concurrently. (Credit: Samer H)
-
-
Task renaming
-
Tasks can now be easily renamed via the edit pencil icon located within the Task Details Information tab, streamlining the renaming process for enhanced efficiency and convenience.
-
-
Columns Headings order & stickiness
-
We've enhanced the Investigation Hub tables, enabling users to choose and easily rearrange columns by dragging and dropping them into their preferred order. This selected layout will remain 'sticky' for each user, providing a personalized experience.(Credit: Allesando G)
-
-
Auto Asset Tagging Rules added to Task Details
-
The Auto Asset Tags used in a Tasking Assignment are now displayed under the Information tab in the Task Details window.
-
-
Enhanced Responder Uninstallation
-
By default, the responder uninstallation process now includes a purge/clean-up operation where certain responder application files that were not removed in earlier versions of AIR will now be purged during the process. It's important to note that evidence saved on the local asset or any external evidence repositories will remain unaffected.
-
Fixes
-
Agent Update Task Errors
-
A recent Windows update affected the ability of some AIR agents ability to auto-update. Fixed in AIR v4.8 (Credit: Blake B)
-
-
Asset labeling/editing issue fixed
-
Typing a new or editing an existing asset label was problematic as the UI was not allowing time to complete typing in some instances. Fixed in AIR v4.8 (Credit: Zainal B N)
-
AIR 4.7
5 February 2024
Features
In AIR version 4.7 and above, we've added a new Docker container specifically for enabling the new File Explorer feature in AIR. If you're not interested in using File Explorer, you can proceed with the upgrade as usual. However, if you do wish to utilize the File Explorer and haven't received assistance with migration yet, please reach out to our support team for guidance on updating to either version 4.7+. Kindly note that contacting our support team is only necessary if you intend to activate the File Explorer feature.
Investigation
-
Introducing AIR's new File Explorer.
AIR can now be used to explore the file systems of Windows, macOS, and Linux systems where full disk or volume images have been acquired in the RAW format.
The forensic image can be added to AIR as a new Asset in a three-step process:
-
1. On the Assets page, click on the ‘Add New’ button and then select Disk Image:
-
2. Select your connected repository and then the raw disk image you wish to explore:
-
3. Select ‘Create Asset’:
The image must be supplied to AIR from an SMB or SFTP shared location, where it needs to be saved as a single contiguous file. Segmented files are not currently supported.
The next step is to select File Explore from the secondary menu:
Now you can browse the asset’s directory structure which is now expanded in the secondary menu (highlighted below) and then go on to select individual files for closer inspection:
A file can be selected with a right-click to download it locally or calculate its hash values.
Advanced filters can be applied to filter the files displayed.
This is just the beginning of our File Explorer project - many more features are planned and your feedback is most welcome.
-
Advanced Filter capability for all evidence category tables
We have added and standardized our advanced filter functionality across all Investigation Hub evidence category tables to:
-
Ensure consistency across AIR's data analysis capabilities.
-
Empower users with flexible advanced query options.
-
Enhance overall data analysis efficiency.
The example above demonstrates the versatility of crafting filters that cater to both simple and intricate requirements. These filters offer support for compound logic by using AND/OR Boolean operators, applicable to any of the available columns. This empowers investigators with robust and flexible filtering capabilities.
-
New collection of remote tool artifacts:
macOS
-
Splashtop Mac Logs
Windows
-
Xeox Logs
-
ZohoAssist Logs
-
Supremo Remote Desktop Logs
-
TightVNC Logs
-
AmmyAdmin Logs
-
GoTo Logs
-
Kaseya Logs
-
Level Logs
-
Remote Utilities Logs
-
RealVNC Logs
-
Splashtop Windows Logs
-
UltraVNC Logs
Enhancements
Investigation
-
Improved visibility to DRONE’s verdicts.
-
V4.7 provides valuable transparency by reducing noisy findings and improving visibility into DRONE’s detection logic helping streamline investigations and boost confidence in DRONE's methodology. (Credit: Garett C)
-
The example below shows how, in the details tab, DRONE will now highlight each finding with:
-
Its description.
-
A reference to learn more about the findings.
-
The actual string that was detected.
-
Investigation Hub - Consolidated View of Bookmarked Items.
-
With this new feature, AIR users can easily access their bookmarked items, bypassing the need to navigate through multiple sections. This simplifies the workflow and saves time. (Credit: Grant O)
-
The ‘bookmarks-only’ view is accessed via the button in the Investigation Hub page header. Findings and evidence categories with bookmarks can be viewed via drop-down arrows.
-
Additionally, the note-taking capability enables users to capture extra context and insights, contributing to a more comprehensive understanding of their bookmarked content. Notes can be added via the edit pencil in the Bookmark Notes column.
Functionality
-
Windows direct collection
-
With the introduction of Windows support, which complements our existing macOS and Linux capabilities, it is now feasible to transmit evidential collections from all three operating systems directly to external evidence repositories, thereby efficiently minimizing the utilization of local disk space.
-
New API functionality
-
Acquisition profiles can be created directly with the API with ‘Get Acquisition Profiles’.
-
Asset Tags can be created or removed with the API (Credit: Blake B)
-
AIR API documentation is found at: docs.binalyze.com
MITRE ATT&CK Analyzer changelog
4.0.1
Yara
-
Added detection for C# and dictionary-based webshells.
-
Enhanced detection of JSP webshells.
-
Enhanced detection of directory traversal and XSS injection indicators found in server logs.
-
Enhanced detection of ProxyShell and ProxyNotShell vulnerabilities.
-
Added detection of various Linux exploits.
-
An updated list of vulnerable and malicious drivers from LOL Drivers project.
-
Added detection for binaries using potentially compromised AnyDesk certificate.
-
Other minor fixes.
Dynamo
-
Minor FP fixes.
(Full changelog is here: AIR MITRE ATT&CK Changelog)
Fixes
-
We are pleased to announce a critical fix regarding some of the NTFS categories of evidence collections, which were causing collection tasks to sometimes become unresponsive. The root of the issue was traced back to our backend library, which encompasses a range of NTFS-related evidence types, including:
-
Page File
-
Hibernation File
-
Swap File
-
Hosts
-
Recent File Cache
-
We have taken steps to address and rectify this issue, and users should no longer experience any issues with these collections. (Credit: Guo Y)
-
Fix applied for an issue regarding the console backup process via the optimization of our backup compression logic. (Credit: Ben H)
AIR 4.5
9 January 2024
Features
Investigation
-
Preview our new Customizable Reporting feature in the Investigation Hub.
-
This initial version is just the beginning, with many more enhancements in functionality and capacity planned for future updates.
-
Users can, at speed, automatically generate an insightful and shareable comprehensive Compromise Assessment PDF report based on DRONE’s findings.
-
This report is fully customizable, enabling users to choose specific elements for inclusion in their bespoke reports:
-
The Verdicts or Scores as determined by DRONE
-
A Company logo
-
An Executive Summary
-
The Methodology Overview
-
The Data Source Statistics
-
An Asset Overview
-
-
Post-generation, the report remains editable via our built-in browser editor, allowing for the addition of analyst-led notes and supplemental details such as observations, recommendations, and conclusions.
-
-
New macOS Evidence Types:
-
FS Events - On macOS 10.17 and later, files with an extension '.fseventsd' (File System Events Daemon) are used to record many file system events, such as file creation, modification, and deletion. This log acts like a 'black box flight recorder' and can be extremely useful in reconstructing the timeline of activities on a Mac.
-
Browser Download data for:
-
Chrome
-
Edge
-
Firefox
-
Opera,
-
Safari
-
Vivaldi
-
Waterfox
-
Brave
-
Arc
-
-
-
New Windows Evidence Types:
-
Browser Download data for:
-
Chrome
-
Edge
-
Firefox
-
Opera
-
Brave
-
Vivaldi
-
-
-
New Linux Evidence Types:
-
Browser Download data for:
-
Chrome
-
Chromium
-
Edge
-
Firefox
-
Opera
-
Brave
-
Vivaldi
-
-
Enhancements
Investigation
-
AIR UI Improvements include:
-
Secondary menus now consistently display drop-down arrows or sub-menu indicators, providing a clear visual cue that additional options are available.
-
Enhanced discoverability by setting menus to expand automatically by default.
-
We have enhanced the Quick Start menu by adding "New Case" and "New Asset" options for streamlined access to these features.
-
-
New Flags for interACT download commands:
-
With these new flags, users can speed up workflows by having the following extra functionality for files they want to download using the ‘get’ command in interACT.
-
Compression: ‘-zip’
-
Password protection: ‘-zip-password’
-
File name change: ‘-name’
-
-
Functionality
-
Investigation Hub Improvements:
-
The import status of task data into the Investigation hub is now displayed. There are four states:
-
Pending task completion.
-
Importing to the case.
-
Import completed.
-
Failed (a ‘Retry’ option is also presented to the user)
-
-
Auto refresh on-demand button (Credit: Ben H)
-
This update introduces an on-demand refresh button, notified via a banner message in the Investigation Hub, when new evidence is available for the current case. This reduces distractions from auto-updates, allowing analysts to refresh the page at their convenience and stay focused during investigations.
-
-
Audit logs for Evidence Imports into the Investigation Hub
-
These new logs detail who accessed the Investigation Hub import feature, when, and what actions they took, enhancing accountability by linking activities to specific users.
-
Fixes
-
Asset names are now included for User Access Logs downloaded from Investigation Hub as CSVs (Credit: Ben H)
-
Asset names are now featured in User Access Logs (UALs) downloaded from the Investigation Hub as CSV files, providing analysts with clear visibility of the originating assets for these logs.
-
AIR 4.3
7 December 2023
Features
Investigation
-
Enhanced Data Integration into the Investigation Hub:
-
Seamlessly import .csv files into the Investigation Hub using our data mapping service, accommodating all forms of structured .csv data.
-
Efficiently import and analyze .pst files, enabling the display of email data within the Investigation Hub for a more comprehensive examination.
-
-
2 New Windows Evidence Types:
-
Winrar History - This application history is valuable as it tracks file compression/extraction, revealing user actions, timelines, and data movement. (Credit: Ashok K)
-
Windows Error Reporting Files - WER files provide insights into system crashes and application failures, helping to identify potential security breaches or system vulnerabilities. Additionally, they are instrumental in malware detection and constructing accurate timelines for security incidents.
-
-
7 New IBM AIX Evidence Types:
-
MySQL Logs - These logs are critical for tracing database transactions, analyzing user activities, establishing timelines, and detecting unusual or malicious query patterns. They provide key insights into data modifications and user behavior.
-
SSH Server Logs - These logs are invaluable for tracking authentication attempts, identifying user access patterns, and detecting potential unauthorized or malicious activities.
-
DHCP Server Logs - provide crucial information on network device connections, including IP address assignments, timestamps, and MAC addresses, aiding in tracking device movements and identifying unauthorized network access.
-
System Logs - Records system activities, user actions, and error messages.
-
Auth Logs - These track authentication activities, such as login attempts and user privileges, providing insights into potential unauthorized access, user behavior, and security policy violations.
-
Boot Logs - Used to analyze system startup sequences, identifying unauthorized changes or failures during boot processes.
-
Mail Logs - Tracks email transactions, identifying senders and recipients, analyzing timestamps, and detecting anomalies or potential security breaches.
-
Enhancements
Investigation
-
Comparison report improvements
-
The Progress window now displays the status of the comparison, including a count for Added, Changed, or Deleted items. When an evidence item is selected, it filters the main viewing window to show the detailed comparison results for that specific item exclusively.
-
The comparison report now also makes it clear when no changes have been detected.
-
-
Exporting DRONE Findings
-
Users can export the DRONE findings table out of the Investigation Hub into a .csv file.
-
This will allow the use of DRONE findings in reports, SIEM, or other security tools where custom alerts can be developed based on the results of DRONE’s analysis.
-
-
AIR’s MITRE ATT&CK Analyzer version 3.1.0 includes the following:
✅ Every detection now links to an MITRE ATT&CK Technique instead of Tactic only.
Yara:
✅ Added coverage for various malware families mentioned in our latest reports.
✅ Enhanced detection of anomalies for various techniques such as masquerading, defense evasion, credentials access, suspicious PowerShell scripts, and more.
Dynamo:
✅ Enhanced detection of HTML Smuggling technique for more Chromium-based browsers.
✅ Enhanced detection of suspicious Firewall rules, Scheduled tasks, and Services.
Functionality
-
Ability to adjust timezones in Investigation Hub
-
By default, the Investigation Hub will use UTC as the timezone to display all timestamps.
-
With this release, Investigation Hub users can adjust timezones, improving analysis accuracy in investigations involving diverse geographic and timestamp data.
-
-
New Asset window for UI
-
Individual assets will now have a dedicated larger window to display more information, appear less cramped, and prepare for future developments.
-
Each Asset page now includes a secondary menu featuring preset filters, providing users with a count and instant access to all past tasking assignments associated with that asset.
-
In this new window, users can view and access all of the cases in which the current asset appears.
-
Tasks can be created from the Asset Action button or by clicking on the ‘+’ revealed when hovering on any of the task names listed in the secondary menu.
-
-
Adjustable Secondary Menu
-
The user can now manually adjust the secondary menu width in AIR, allowing it to expand up to half of the display window's width through a simple drag action.
-
Double-clicking the secondary menu border will return it to its default size.
-
-
New advanced filter to identify servers
-
Users can now filter assets based on whether or not any of their assets are servers. (Credit: Jon F)
-
-
Custom Message Banner available via API
-
Users can use all custom banner capabilities via API - the latest posted message, by UI or API, will prevail.
-
-
Removal of a default value from the acquisition profile selection field
-
When initiating a new Acquisition, the Acquisition Profile field will now be blank by default, requiring the user to actively choose a profile. The placeholder text in this field now reads, "Select/create an Acquisition Profile." (Credit: James S)
-
Fixes
-
Data grid issue with Organization Updates
-
Data grids now refresh correctly when Organizations are updated.
-
AIR 4.1
2 November 2023
Features
Investigation
-
6 new macOS Evidence Types:
-
SSH Known Hosts - Collects SSH Known Hosts used to store the SSH server key fingerprints of the servers that you have connected to in the past.
-
SSH Authorized Keys - Collects SSH Authorized Keys which grant user account access and are crucial for SSH key-based access.
-
SSH Configurations - Collects SSH Configurations which record remote IP addresses, different usernames, non-standard ports, and various used command-line options.
-
SSHD Configurations - Collects SSHD Configurations which indicates the locations of host key files and users' authorized_keys files.
-
Brave History - Collects Brave browser history.
-
Vivaldi History - Collects Vivaldi browser history.
-
-
3 new Windows OS Evidence Types:
-
Registry SAM Users - Collects Users and Groups from the SAM file. (Credit: Ashok K)
-
Brave History - Collects Brave browser history.
-
Vivaldi History - Collects Vivaldi browser history.
-
-
Persistence - A new Windows Evidence category for AIR which groups the following evidence items often essential to Windows DFIR investigations:
-
Active Script Event Consumers - Dump WMI Active Script Event Consumers.
-
Command Line Event Consumers - Dump WMI Command Line Event Consumers.
-
Registry Items - Enumerate Registry Items.
-
Scheduled Tasks - Enumerate Scheduled Tasks.
-
Service List - Enumerate Service List.
-
Startup Items - Enumerate Startup Items.
-
Security
-
New SSO integration capability via Okta (Credit: Brian W)
-
AIR now supports an integration with Okta allowing customers and partners to login securely with Single Sign-On for user authentication.
-
Enhancements
Security
-
Filter DNS traffic on Linux Isolation
-
The Linux asset isolation feature in AIR now offers more secure protection from any communication other than that coming from the AIR console. This enhancement mechanism mitigates possible attack techniques from:
-
DNS Tunneling
-
DNS Data Exfiltration
-
-
Functionality
-
Editable address for Relay Server
-
Flexibility and improved network management allowing users to set any IP or any FQDN for a registered relay server which provides flexibility and easy management on the network.
-
-
Investigation Hub hash to VirusTotal links
-
In the individual asset or case level Investigation Hub reports, every piece of evidence with a hash is now accompanied by an eye icon. Clicking this icon will direct you to the VirusTotal website for a detailed analysis of the hashes.
-
-
Off-Network Password File availability improvements
-
The BiUnzip tool now offers enhanced access to the passwords file, streamlining the decryption of multiple Off-Network zip files.
-
The Off-Network Asset passwords file will now always be available at; Asset (name) > Tasks > Details > Information Tab.
-
This update facilitates more efficient data extraction for our users. For detailed guidance on using the BiUnzip tool, please consult our Knowledge Base: biunzip
-
-
AIR agent disk space optimization during acquisition-compression
-
The AIR agent's disk space usage during the acquisition's compression phase has been optimized. This, combined with specific conditions, ensures a more efficient process to help the success rate of acquisition tasks.
-
Fixes
-
Column Search in the Investigation Hub now working correctly
-
After conducting a global search in the Investigation Hub any ‘column search’ failed to return results - this is now fixed.
-
AIR 4.0
12 October 2023
Features
Streamlining Workflows - Introducing the all new UI/UX for AIR
-
New floating header at the top of every page to allow immediate access to:
-
Searching across AIR.
-
Recent Cases, Assets, Tasks and Reports.
-
The Quick Start button to launch AIR Tasks.
-
Notifications
-
Current Organization name display, with a dropdown to switch between Organizations.
-
-
Organization selection improvements
-
To eliminate any potential confusion regarding the organization's assets you are currently viewing, the system now displays only one organization at a time.
-
Switching between Organizations has been made simpler via the Organization dropdown menu which provides access to:
-
Organization Settings.
-
Change Organization.
-
Add New Organization.
-
-
-
Main menu bar is now split into two sections:
-
The top section is now home to the core areas for AIR;
-
Home: Full overview of your AIR deployment.
-
Assets: Listing of current Assets.
-
Cases: Listings for open, closed and archived Cases.
-
Libraries: for Acquisition profiles, Triage Rules, interACT Files and Auto Asset Tagging rules.
-
-
-
The bottom section is home to AIR’s supporting functionality;
-
Integrations: API Tokens, Webhooks and Cloud Platforms.
-
Activity: With Insights, Recents, Notifications and Audit Logs all clearly displayed for analysts.
-
Tasks: All of your Console Tasks displayed in one window for searching and filtering.
-
Timelines: To review existing or create new Timelines.
-
Settings: The bottom of the Main Menu is the new home for all of your Settings; Assets, Security, Features, Users/Roles, Evidence Repositories, Policies and Backup.
-
-
New Secondary Menu Bar
-
This new menu appears when a Main Menu item is selected.
-
This is collapsible to maximize your screen’s working space but at the same time, allows users to drill down in AIR functionality at speed.
-
-
New Navigation Bar
-
This allows the user to see exactly where they are in every screen of the AIR platform by showing the ‘path’ to the current view.
-
-
Access to Recents via the Homepage
-
Direct access to Recent Cases, Recent Assets, Tasks and Reports - making it easier to pick up where you left off.
-
-
New Bulk Actions Bar
-
Found at the bottom of the Asset page to count the number of assets selected and provide easy access to the Taskings that can be applied to those assets.
-
-
Settings changes
-
Moving the “Enable Policies” toggle from the Policies page to Settings > Features
-
New Operating System support - IBM AIX
-
IBM AIX Off-Network Agent
-
AIX is a series of widely used Unix operating Systems for business critical applications developed by IBM.
-
These systems have proved tricky to investigate and are not covered well by existing security products, but now AIR provides the necessary support to do so.
-
Investigation
-
Introducing the AIR Investigation Hub, formally known as Consolidated Reports
-
For ease of access and to create a collaborative investigative space, the new Investigation Hub is now available from the secondary menu bar within each individual Case.
-
New Forensic Evidence Collections
-
15 new macOS Evidence Types and a new Evidence Category:
-
Downloads - presents information about downloaded files.
-
IP Route - presents IP route information.
-
Logged Users - shows currently logged in users.
-
Network Interfaces - presents NIC information.
-
Event Taps - reveals items that have a tap into the system.
-
DNS Resolvers - presents DNS resolution information.
-
Quicklook Cache - reveals items previewed with Quicklook.
-
Cron Jobs - presents scheduled/cron jobs
-
Arc History - collects Arc browser history.
-
Reopened Apps - shows apps not installed but in re-opened plist.
-
-
Persistence - New category which groups the following evidence items often essential to macOS DFIR investigations:
-
Mail Rules - collects mail rules that contain AppleScripts.
-
Login Hooks - these hooks can be used to achieve persistence.
-
Logout Hooks - as above.
-
Emond Clients - Emond accepts events from services.
-
Most Recently Run - The MRU lists the most recents files a user accessed.
-
-
Forensic image files in a single Zip file.
-
This release introduces a new toggle switch, giving users the option to enable or disable the consolidation of physical disk or volume image files into a single zip file, eliminating the need to split them into chunks.
-
Integrations
Yet more Webhooks for AIR to supercharge your SOC's automated data collection and analysis capabilities:
-
Webhook parser for SentinelOne. (Credit: Dane Z)
-
Webhook for Microsoft 365 Defender.
-
Cisco AMP/XDR.
Enhancements
Security
-
Password Protection for AIR Agent Uninstallation
-
We already provide Tamper Detection for the AIR Agent - now users can only uninstall the AIR Agent if they have access to the password to do so.
-
Agent uninstallation through the OS UI is disabled. The agent can only be uninstalled using shell commands with the protection password as an argument, locally or remotely (e.g., SCCM).
-
Uninstallation via the AIR UI or API remains possible without requiring a password.
-
Investigation
-
Detailed Browser History and Download History
-
In this release, we've refined the representation of Chrome browser forensic data, particularly within the browser and download history evidence segments, including:
-
Referrer details
-
Signature
-
Hash values
-
Timestamps
-
Visit duration insights, and others.
-
-
These enhancements enable analysts to conduct a more in-depth browser forensic examination.
-
-
Timeline Enhancements
-
Horizontal scrolling functionality has been added, making it simpler to navigate and concentrate on specific dates and times within your timelines.
-
-
Prefetch Parsed Referenced Files
-
Users can now more easily analyze prefetch records as AIR now displays 5 categories of information in a single view.
-
-
Character limitation for single triage rule
-
To prevent the browser becoming unresponsive we have limited the maximum to 350K of characters in a single Triage Rule.
-
Fixes
-
Password Recovery - Email Fix
-
If SMTP is not configured, AIR can not send emails. Previously, users attempting a password reset were told to check their email, leading to confusion when no email arrived. We've updated this to now prompt users to contact the administrator instead.
-
-
Timezone inconsistencies in Investigation Hub
-
Timezone data will now be displayed in the user's local browser time and timezone information will be displayed to the user at the top of the Investigation Hub page.
-
This timezone setting can not be changed by the user.
-
-
YARA rule failed to validate
-
Validation of some correct YARA rules was failing, this has been modified and now works correctly. (Credit: Nick H)
-
-
Improvements to Offline Installer Scripts (Credit: Blake B)
AIR 3.12.4
Hotfix
-
We have made the Consolidated Report button enabled for Cases that were created before version 3.12.3 was released. Users can now use Consolidated Reports as expected without any problem.
-
To learn more about consolidated report- read this article.
-
When a Task is Failed, even though an error message reflects the issue, shown as an “Unexpected Failure” message within the Tasks Details page (by hovering over the “eye” icon in the Status tab); the Console did not report the correct status immediately. We have fixed this issue and the correct status is now reported.
-
When a user chooses a 'Custom Option' to collect evidence and the mode of "Direct Collection" toggle (on Linux or MacOS) is changed while a Task is still running, the agent may crash. We have fixed this issue to avoid the possibility that the agent will crash.
AIR 3.12
Features
Streamline your investigation
-
DRONE analysis for macOS
-
MITRE ATT&CK Analyzer
-
As of v3.12 DRONE now has MITRE ATT&CK rules for macOS.
-
-
Dynamo Analyzer (Credit: Dilek G)
-
Dynamo will parse the AIR report generated as the result of a task assignment and highlight suspicious entries.
-
-
Browser History Analyzer
-
Chrome, Edge, IE (7-11), Firefox, Opera, Safari, Vivaldi, Waterfox and Brave are now all supported for macOS
-
-
Audit Event Analyzer
-
Brings advanced capability to AIR by scanning event records for keywords, hacker tools, and commands, setting verdicts based on criteria, guidelines, or Sigma rules.
-
-
-
Tooltips added to DRONE findings within the Consolidate Report
-
When a user hovers above a Verdict or Score finding listed in the Table view, they will be presented with a to a tooltip that explains how the result is derived.
-
-
Isolation of macOS endpoints
-
Expanding Isolation capability to the last major operating systems -macOS. (Fully supports Windows, Linux & macOS devices).
-
Regardless of the isolation state, the endpoint maintains communication with the AIR console to allow analysts performing their investigation by generating Tasks as usual.
-
-
Addition of a "Retry Upload" action for failed Task Assignments (Credit: Daniel M)
-
Should a failure occur during the evidence upload phase of a task, a "Retry Upload" feature is now available to resolve issues more efficiently. Key benefits include:
-
Elimination of the need for evidence re-acquisition, preserving the original data.
-
No additional disk space consumption.
-
The "Retry Upload" option repurposes the existing task assignment for the re-upload, preventing task duplication.
-
-
-
Simpler access to Off-Network Agent logs & Drone log files
-
Agent logs and Drone log files of Off Network are now saved in the same folder . This makes it easier to find any log files and share them with Binalyze Technical support or for troubleshooting by yourselves.
-
File name format is: Troubleshoot-[TIMESTAMP].zip.
-
Enriching evidence and artifacts
-
New Artifact types collected for macOS:
-
Discord Desktop Cache
-
Discord instant messaging and VoIP social platform with voice calls, video calls, text messaging, media and files in private chats or as part of communities called "servers".
-
-
Parallels Logs
-
Parallels is a software company best-known for Parallels Desktop for Mac that allows users to run Microsoft Windows systems on macOS computers.
-
-
Homebrew Logs
-
Homebrew is a free and open-source software package management system that simplifies the installation of software on macOS, as well as Linux.
-
-
Sophos Events Database
-
Sophos develops products for communication endpoint, encryption, network security, email security, mobile security and unified threat management.
-
-
Sophos Antivirus Logs
-
The AIR agent will now collect Sophos Antivirus logs.
-
-
-
New Evidence types for macOS:
-
Shared File List
-
The SharedFileList (SFL) in macOS is a system feature that manages "recent items" lists for applications and the system itself. These lists could include recently used applications, documents, servers, or even volumes. The files with the extensions .sfl and .sfl2 are plist (property list) files in binary format.
-
-
Shell/Bash History
-
The .bash_history file holds significant value for various reasons including command tracking which may reveal the activity of an attacker. However, note that the .bash_history file can be manipulated, cleared, or even disabled by knowledgeable users.
-
-
Synchronization and collaboration between teams
-
Customizable Banner Message (Credit: Helen T)
Users can now display important announcements via a banner on the console GUI for events like maintenance, upgrades, or config changes. The banner interface allows:
-
Scheduling via Start/End dates
-
Message editing - up to 512 characters
-
Color customization
-
URL linking
-
Banner dismissal to maximize screen space
This feature provides direct communication with AIR users and offers permission controls for message settings.
Enhancements
AIR Core Functions Enhancements
-
-
Timeline
Swipe through a Timeline Bar to view events, dates, or time periods that are outside the current visible area.
-
-
Click-and-drag: The user clicks on the timeline bar and drags it left or right to scroll through the timeline.
-
Swipe wheel: If the device supports a scroll wheel or touchpad gestures, the user can use it to scroll left or right on the timeline bar.
-
-
-
Triage
Many more new triage rule templates are available to assist when constructing triage task assignments including:
-
-
YARA - Find by size range
-
YARA - Find Portable Execution files only
-
YARA - Find PKZIP files only
-
YARA - Find by hash value after filtering by file size
-
Sigma - User account hidden by registry
-
osquery - Unusual Cron entries
-
osquery - Processes running with no binary on disk
-
-
-
Consolidated Reports Enhancements
-
Consolidated Report Module refactoring to provide Generic Report Module
-
This new module generates individual task assignment reports that maintain the same view and structure as the existing Consolidated Reports.
-
-
Triage results from osquery are now available in Consolidate Reports
-
osquery results are now also searchable from the Global Search.
-
Security Enhancements
-
Automatically renew default AIR SSL certificate (Credit: Ramesh P)
-
The Binalyze-generated self-signed certificate will now auto-renew when it's within 10 days of expiration.
-
Fixes
-
Issues connected with CPU limitations have been resolved (Credit: Helen T)
-
Expired Task Assignments will no longer delay subsequent Task Assignments (Credit: Christian K)
AIR 3.11.1
3.11.1 is all about Timeline enhancements and bug fixes. Binalyze team would like to thank its customers who shared their feedback and input to help us improve the quality and usability of the Timeline Bar, Flags and Filters.
Enhancements
-
Several Timeline improvements including;
-
-
Enhanced Date and Time Selection: Users can now specify both start and end dates, with precision down to individual hours, facilitating more granular timeline investigations.
-
User-Defined Navigation: The introduction of arrow-based navigation allows users to move backward and forward through user-specified periods, as determined in the date/time selector.
-
Refined Zoom Capability: The Timeline histogram now supports zoom functionality down to a singular hour for precise analysis.
-
Dedicated Tab for Flagged Items: We have reintroduced a specialized tab within the Timeline view to prominently display flagged items, ensuring streamlined navigation for significant events.
-
Fixes
-
Event Id not displayed in Timeline UI
-
-
The Event ID artifact now populates its details in the Title column of the AIR Timeline UI. (Credit: Grant O)
-
-
Timeline flagging fixes
-
-
We've implemented multiple fixes to the flagging feature in the Timeline, resulting in overall usability enhancements.
-
AIR 3.10
NB: The MongoDB relies on the CPU architecture that runs your AIR server. For this update, AIR v3.10, the CPU has to be newer than 2011 for both Intel and AMD processors. If your processor architecture is older than this, it is not advised to update MongoDB.
Features
-
Disk Space limit configuration for Acquire Evidence Tasks
-
-
When evidence collections are stored on the local machine, this new feature, for macOS and Linux, will allow AIR users to determine the amount of free disk space to always be left available to the local user.
-
If a collection is not complete when the allocated disk space limit is reached, the collection at that point and the .ppc will be available to the analyst in the normal way.
-
The Task Status will be marked ‘Partially Completed’.
-
Task Logs will now be available in the Case Report, under Case Info, and in Consolidated Reports in the Case Summary. These logs will list any uncollected evidence items.
-
-
Bandwidth limit configuration for Acquire & Image Evidence Tasks
-
AIR users now have the ability to determine the amount of network bandwidth they wish to allocate to their AIR collections.
-
-
Ability to purge locally saved acquisition task data
-
This new action, ‘Purge Local Data’, will create a ‘Purge’ Task to remove all data generated for a task assignment on an endpoint.
-
Purge Local Data can also be run from the Case’s page to purge all data generated for a task assignment on an endpoint.
-
Purging local data will not affect the installed AIR agent, so it remains ready for new task assignments.
-
To use Purge Local Data, the privilege “Delete task assignment” is required.
-
Binalyze AIR now supports the collection of over 350 evidence items.
New evidence types collected for Windows:
-
LNK Files
-
AIR will analyze and parse LNK files which are often abused by hackers, who can leverage them to use legitimate applications (such as PowerShell) to download malware or other malicious files.
-
-
Users
-
User accounts are created and stored as objects in Active Directory Domain Services. These accounts can be compromised by bad actors and programs such as system services used to log on to a computer. A successful login generates an access token which includes the security identity and group memberships of the user account associated with the process or thread. Every process executed on behalf of this user has a copy of this access token.
-
-
Timeline
-
Windows 10 Timeline feature enables users to: (i) View their currently running apps and look back at their previous activities such as; opened documents, programs, images, videos or visited websites. (ii) Synchronize activities across devices. (iii) Provide information about applications that were executed within the last 30 days, such as application name, time when it was launched and its duration. This information can be of forensic value, helping to reconstruct events, even if the files, documents or applications have been deleted.
-
-
UAL Logs
-
User Access Logs (UAL) store a lot of information and often present IT admins with privacy concerns. One such feature helps correlate an account and the source IP address with actions performed remotely on systems, so potentially valuable to attackers. (Credit: Daniel M)
-
New Evidence Types For macOS:
-
Apple Audit Logs
-
macOS writes important operational and security information that can be useful to an attacker as a place to obfuscate changes that were recorded. As part of defense-in-depth, the files in /var/audit should be owned only by root with group wheel with read-only rights and no other access allowed. macOS ACLs should not be used for these files.
-
-
AnyDesk Logs
-
AnyDesk is a remote desktop application that provides platform-independent remote access to personal computers and other devices running the host application.
-
-
Teamviewer Logs
-
TeamViewer is a German remote access and remote control software application often concerned with the maintenance of computers and other devices.
-
New Evidence Type For Linux:
-
AnyDesk Logs
-
(See above)
-
-
Filtering of Tasks to determine the presence of DRONE data
-
AIR now creates a metadata flag: ‘hasDroneData’ which indicates that DRONE data exists for a particular Task and reports with DRONE data can be filtered for in the endpoint’s Task listings.
-
-
‘biunzip’ is a new command-line tool from Binalyze specifically designed to extract zip files generated by the AIR Off-Network Agent.
-
You can download the latest release of biunzip from the releases section on GitHub: Let’s build from here
-
Biunzip will either unzip a single zip file or unzip zip files in a directory using a CSV file.
-
This capability will allow running off-network investigation at scale, and at speed with minimum effort.
-
Enhancements
-
Huge Timeline improvements
-
The timeline events bar is now displayed in histogram format, making it clear when activity has taken place.
-
The timeline bar now has zoom-in and zoom-out capabilities allowing users to drill down from decades to individual hours.
-
Findings flags will be shown in the timeline bar.
-
Filtering down via start and end dates is now possible as is filtering by; decades, years, months and days.
-
-
Hash Values for all Event and Registry Files are now shown in all Case and Consolidated Reports.
-
These hash values are searchable via Global Searching.
-
-
Last Used fields added
-
To help better understand analyst’s activity within AIR, a ‘Last Used Field’ has been added to the following pages:
-
interACT Library
-
Evidence Repositories
-
API tokens
-
Webhooks
-
Acquisition (profiles)
-
Triage (profiles)
-
-
-
Backup AIR every 4 hours
-
It is now possible to automate your AIR backups to take place every 4 hours, or or as was available in previous versions; daily, weekly and monthly. (Credit: Daniel M)
-
-
Loading Bar added for Async Commands
-
A loading bar for ongoing asynchronous commands is now displayed in all interACT shell sessions.
-
Fixes
-
No significant fixes needed this month
AIR 3.9.2
Features
-
Acquisition Profiles now display average time taken to complete
-
-
This great new feature displays to the user the average time it takes to run a particular acquisition profile in their own AIR environment. This will help analysts make decisions as to which Profile is best suited to a particular circumstance. (Credit: Daniel M)
-
This feature is unique to the users own environment, so the collection of metrics will start afresh with each new AIR console install.
-
-
New wizard to add endpoints to a Timeline
-
This dedicated Timeline wizard will speed up and simplify the addition of endpoints to your Timelines. The new flow allows you to select endpoints, define the Task and then choose the post acquisition analyzers such as DRONE or any of the other AIR analyzers needed for your specific investigations.
-
This feature is aligned with the new Quick Start feature introduced in v3.8 - Both designed to simplify and speed up your investigations.
-
-
Five new Webhooks available in AIR:
-
Stellar EDR
-
LogicHub SOAR (DEVO)
-
Rapid7 InsightIDR
-
Fortigate SIEM
-
Dynatrace
-
Take advantage of AIR’s Webhooks to increase your SOC’s automated collections and analysis of data from endpoints and dramatically speed up all of your investigations.
-
New macOS evidence support - Apple System Logs
-
Apple System Log Files (.asl files) contain detailed records of various system events, processes, errors, warnings, and activities that occur on a macOS device.
-
-
New macOS evidence support - Apple Unified Logs
-
The Apple Unified Logs (AUL) system was introduced with macOS 10.12. It creates a standard log format used in all Apple operating systems, including macOS, iOS, watchOS, and tvOS. One of the most powerful filtering capabilities of AUL is the predicates.
-
AIR will present unified logs using the comprehensive set of predicates shown below:
-
User login events
-
Tccd events
-
Ssh activity events
-
Command line activity run with elevated privileges
-
Kernel extension events
-
Screen sharing events
-
Keychain unlock events
-
Sessions creation and destruction events
-
Detecting and blocking malicious software events
-
Failed sudo events
-
MDM Clients Events
-
-
Enhancements
-
Consolidated Report improvements
-
To support collaboration between analysts by highlighting important evidence and findings, we have added the option to bookmark items within Consolidated reports.
-
Users can also see who bookmarked an item and when they did so. They can also apply filters to show ‘Bookmarks’ or ‘Bookmarked by’.
-
A new ‘event viewing’ window will display expanded details for any item selected in the main viewing area.
-
Global Search has been enhanced for faster search returns.
-
-
YARA rule scans can be run via interACT
-
It is now possible to run YARA scans inside the AIR cross-platform remote shell, interACT. (Credit: Ramesh P)
-
-
YARA and Sigma rules use the same verification method
-
Binalyze AIR will now use matching validation methodologies for these two different rule types, so YARA and Sigma scanning can no longer be tasked to run any incompatible rules. (Credit: Antonio L)
-
Fixes
-
AWS S3 upload failures
-
Simultaneous upload issues to AWS S3 bucket and all other repositories have been fixed by enforcing sequential uploads only. (Credit: Simon L)
-
-
Reporting a Failed Status
-
When a Task is running, and something causes the agent to restart, a ‘failed’ status will be shown when the agent starts again if any of the tasks fail to complete.
-
-
Timeline imports to Chrome
-
An issue preventing Chrome uploads to the AIR Timeline has been resolved.
-
-
Authentication Errors for Public API's are fixed
AIR 3.8
Features
-
New Quick Start wizard for launching AIR tasks.
-
-
This new feature is available from all AIR Console views, it speeds up and simplifies the launching of AIR tasks; Acquire Evidence, Acquire Image, Triage, interACT, Timeline, Compare and Schedule Acquisition.
-
-
Disk Images
-
AWS S3 and Azure evidence repositories now provide support for forensic disk image acquisitions. (Credit: Daniel M)
-
-
Downloading from Evidence Repositories - For individual endpoint Case Reports, it is now possible to directly download the evidence.zip file associated with that report:
-
A download button will be shown for the following sources:
-
-
AWS
-
Azure
-
-
-
A URL with a copy button will be shown for the following sources:
-
-
Local
-
SFTP
-
FTPS
-
SMB
-
-
-
-
AIR Backup - AWS S3 is now a supported repository for AIR backups (Credit: Daniel M)
-
Relay Server - Not everyone can have direct access from all of their endpoints to the AIR console. This new AIR Relay Server/traffic router capability, will allow network segments which need to remain air-gapped to communicate with the AIR console.
*This feature will be enabled per demand. If you're interested, contact your customer success.
Enhancements
-
Task Naming - Users can customize the individual Tasks' name. In doing so, this will override the default auto-task naming function. If the user decides not to give the task a customized name, AIR will revert to its auto-task naming convention.
-
Settings Menu - Streamlining the main settings menu by relocating the following to the sub-settings tab; Users/Roles, Evidence Repositories and Licence options.
-
The new settings menu is grouped as follows:
-
General - Version, Logging, License, Connection, Console Proxy.
-
Endpoints - Agent updates,, Tamper detection, Active directory.
-
Security - SSL certificate, SSL root CA, Console port, IP restriction, Authentication, SSO.
-
Features - Enable interACT, Resolve Agent Public IP, Case selection, RFC3161 Time-stamping, SMTP, Syslog / SIEM.
-
Users/Roles
-
Evidence Repositories
-
Backup
-
-
-
New artifacts for collection - For macOS, in both ‘Full’ and ‘Quick’ acquisition profiles we have added; Quarantine Events, Sudo Last Run, iMessages, Dock Items (dock.plist) and Document Revisions.
-
UX improvement - In the Timeline view it is now possible to select or deselect all evidence categories with a checkbox found at the top of the evidence category listings.
-
UI improvements - To improve workflow:
-
When creating a New Case in AIR, the Organization field will not be automatically populated anymore, it will remain blank so that the user is ‘forced’ to think about which Organization the New Case should be attributed to.
-
The auto expansion animation has been removed from the left side navigation menu of the UI.
-
-
Evidence Repository - It is now possible to define a Domain Name for any new SMB Evidence Repositories.
-
Triage Rules - There is now no limit to the number of triage rules available to investigators.(Credit Antonio L)
-
Yara - AIR’s version of Yara has been updated to Yara v4.3.1.
-
interACT opens in a new window - allowing users to continue to use the Console UI and have several interACT sessions active simultaneously.
-
interACT auto-complete - Navigation between the auto-complete options is now possible with tab key. (Credit: Christian K)
-
$mft as a .csv improvement - The full file path for each $mft record entry will now be included in the .csv generated by an AIR, ‘$mft as csv’ collection.
-
CPU limit for macOS - Users can now limit the amount of CPU usage available to the AIR agent on the endpoint when assigning a task.
Fixes
-
OSquery on Triage bug fixes. (Credit: Christian K)
-
Timeline bug fixes. (Credit: Ramesh P)
AIR 3.7
Features
-
Triage Match Count Column
-
In the Task window it is now possible to select, from a column selector, to display a column for Match Counts, and if the user filters by Triage the Match Count column will be added automatically to the filtered results.
-
-
New Webhook - Microsoft Sentinel
-
AIR now has built-in support for a Microsoft Sentinel Webhook (Credit to Elisa.com - Finland).
-
-
Mandatory Case Selection Option
-
This new feature allows Enterprise and MSOC customers to enforce the selection of a case for all Acquisition and Triage tasks ensuring that all collections and tasking results are attributed to a case. For FIS customers this feature will always be active by default.
-
-
New Chrome artifacts for Mac Linux and Windows
-
For Mac, Linux and Windows support has been added for parsed evidence from Chrome; Bookmarks, Cookies, Downloads, User Profiles, Extensions and Browsing History
-
-
Isolation Support for Linux
-
Linux endpoints can now be 'Isolated' from within the Endpoints Details UI window.
-
-
New 'Last Seen' Endpoint Filter
-
AIR now allows for the date and time filtering of endpoints by; 'Last Seen After', 'Last Seen Before' and 'Last Seen Between'.
-
-
Apple macOS TCC collection
-
AIR now supports the collection of Mac TCC (Transparency, Consent and Control) data.
-
IMPORTANT: In order to benefit from these new features, you should install our new DataBase. Click here to learn more.
Enhancements
MITRE ATT&CK enhancements
-
MITRE ATT&CK Rules with Drone for Acquisition and Triage Tasks
-
Users can now see and select the MITRE ATT&CK analyzer in both the Acquire Evidence and Triage Tasking windows. In these views it is now also possible to see when AIR last checked our MITRE ATT&CK database to ensure that the user has access to the latest MITRE ATT&CK definitions for AIR.
-
-
MITRE ATT&CK Rules support for off-network tasks
-
The same level of support mentioned above for MITRE ATT&CK is now also available for off-network Evidence Acquisitions and Triaging.
-
-
MITRE ATT&CK Tactics Widget View within Consolidated Report
-
The Consolidated Report now aligns and displays artifacts by the number of times a particular MITRE ATT&CK Tactic, Technique or Finding has been identified. The Technique and Sub-Technique identified will also be displayed along with a direct link to the relevant MITRE ATT&CK webpage.
-
-
MITRE ATT&CK Auto update
-
Binalyze AIR will now automatically check for any new MITRE ATT&CK updates as soon as a user opens the Acquire Evidence or Triage Tasking windows. An internet connected AIR installation is required, ensuring customers always have access to the latest AIR MITRE ATT&CK definitions. (Off-Line support will be coming in future versions)
-
Consolidated Report enhancements
-
Consolidated Report: MITRE ATT&CK Report View
-
The Consolidated Report front page now displays a MITRE ATT&CK overview report.
-
-
Consolidated Report: Event Records Consolidation
-
Event Records are now consolidated in human readable format for investigators.
-
-
Consolidated Report: Global Search
-
Global Searching is now possible across Consolidated Reports. This feature addition is super powerful, and allows users to search across all of the acquisition and triage data that constructs a Consolidated Report from multiple endpoints in any particular case.
-
-
Consolidated Report: Process Details View
-
An event details module has been added at the bottom of the evidence item page, so when an item is selected in the upper window, if there is additional information available it will be displayed in the lower details window.
-
-
Consolidated Report: Process Tree View
-
A Tree view is now available for processes within Consolidated Reports.
-
-
Consolidated Report: CSV export
-
It is now possible to export Evidence Items from within the Consolidated Report to CSV.
-
Fixes
-
Security fix related to endpoint isolation
-
Security fix related to the installation process
-
Security fix related to the password reset process
-
Security fix related to access to server files
AIR 3.6
Features
-
Public key authentication support was added to SFTP evidence repositories
-
Users can use public key authentication on SFTP servers or services such as Amazon Transfer Family to store the evidence and artifacts.
-
Users can use either a username and password authentication or public key authentication on SFTP on Evidence Repository
-
Enhancements
-
N/A
Fixes
-
Minor bug fixes
AIR 3.5.1
Features
-
Consolidated Report.
-
The Consolidated report is a single, easy-to-read DFIR intelligence report, that displays Acquisition and Triage acquired data from multiple endpoints in one report.
-
-
Triage with OSQuery.
-
Analysts can now create, modify and run OSQuery queries across multiple assets in the AIR Triage GUI, along with our pre-existing YARA and Sigma capabilities.
-
-
Timeline support was added for Linux and macOS.
-
Investigators and analysts can add Linux and macOS artifacts to AIR Timelines. Leverage this addition to have just one Timeline with multiple endpoints from all 3 operating systems; Windows, Mac and Linux. This is potentially another massive boost to speeding up investigation times.
-
-
Importing Chrome/Chromebook collections to Binalyze AIR Console
-
Investigators and analysts can now add standalone Chrome evidence acquisition results (PPC file) to Binalyze AIR
-
-
New Artifacts and Evidence for macOS and Linux.
-
More than 35 new artifacts and evidence types, such as Apache, Nginx, MySQL, PostgreSQL, MongoDB, Docker, KnowledgeC, and more system-related logs were added to Binalyze AIR
-
-
Organization Tags
-
Managed SOCs partners (MSSPs) can add, remove, list and group their Organizations by Tags. This would simplify operational day to day needs, since it is much simpler to define and classify each Organization by 1 or multiple Tags. The new capability is available also via the API.
-
Enhancements
-
N/A
Fixes
-
interACT get the command’s unresponsiveness bug fixed
-
interACT session termination bug fixed
AIR 3.4.3
Features
-
Network Capture for Linux and macOS
-
Beginning in version 3.4, the network capture feature is available on Linux and macOS operating systems.
-
-
Display Real IP Addresses of Endpoints by using XFF (Credits: Aaron V.)
-
AIR Console can read and parse the HTTP requests and XFF headers from the Forward Proxy and associate them with the assets to determine the assets' real IP.
-
-
x64 support for Off-Network Microsoft Windows
-
Beginning in version 3.4, Microsoft Windows 64-bit Off-Network binary package is available and can be run on supported 64-bit architectures.
-
-
Disk Imaging
-
Binalyze AIR provides disk imaging which we call “Acquire Image”, for Microsoft Windows, Linux, and macOS operating systems.
-
-
The last Seen Endpoints filter parameter was added to API (Credits to Garmin)
-
“Get Endpoint” API request now has the Last Seen Endpoints filter parameter. So the assets can be listed by the last seen date.
-
-
AIR for Chrome
-
AIR For Chrome is the evidence collector extension for Chrome and ChromeOS. AIR For Chrome extension allows investigators and analysts to capture forensically sound data with a single click at machine speed.
-
Enhancements
-
The character limitation on the hostname field of the Endpoints is removed.
-
Beginning in version 3.4, there will be no character limitation for assets' hostnames. Assets that have hostnames longer than 15 characters won't be trimmed and shown as they are.
-
-
The Endpoint Details page has been improved
-
The new endpoint details page is more organized and practical and provides more information about the asset.
-
The name of the System Resources tab has been changed to Hardware, and Volume and disk information will be shown here.
-
Acquire button function has been expanded. When it is clicked, Acquire Evidence and Acquire Image options will appear, and users can select any of them to start a data acquisition or disk/volume imaging task.
-
Disk and volume imaging, what we call Acquire Image tasks, can be performed in Volume or Disk tabs under the Hardware section of the Endpoint Details page.
-
AIR 3.3.1
Features
-
Multiple Sigma Rule Upload
-
Investigators and Analysts can upload multiple Sigma rules to AIR Console at once
-
-
Taking Full Logical Volume Images by using the user interface
-
Investigators and Analysts can create full logical volumes of images using either a user interface or a secure remote shell interACT.
-
Microsoft Windows, Linux, and Apple macOS operating systems are supported
-
-
x64 support for Windows Agent
-
Beginning in version 3.3 64-bit version of the Microsoft Windows AIR Agent is available.
-
-
Case ID Prefix
-
Customers using more than one Binalyze AIR Console instance can now add a prefix to their Case IDs. Therefore there will not be experienced any confusion about Case IDs anymore.
-
-
Progress monitoring added to Get & Put commands on the interACT
-
Investigators and Analysts can see the file download progress from an endpoint (get command) and file upload to the endpoint from the library (put command) command outputs while using secure remote shell interACT.
-
-
MITRE ATT&CK Scanner was added to Binalyze AIR Automated Threat Analyzer, DRONE
-
When Investigators and Analysts scan their systems with DRONE, they can see the MITRE ATT&CK mapped results in the report. DRONE rules are continuously developed and mapped to the MITRE ATT&CK framework.
-
Enhancements
-
Some security improvements on AIR Console
-
Some performance improvements on AIR Console
Fixes
-
Minor bug fixes
AIR 3.2.4
Hotfix
-
Binalyze AIR uses the JWT library that was compromised, immediate actions have been taken to remediate and AIR v3.2.4, containing the hot-fixes for the related vulnerabilities, has been released as of today. This includes fixes for the indirect vulnerabilities due to second-level dependencies.
Therefore, it is strongly recommended to update your existing AIR deployments to this latest version AIR v3.2.4 at your earliest convenience.
AIR 3.2.2
Features
-
Activity Overview Dashboard added
-
Activity Overview Dashboard is a dynamic dashboard that provides tabular and graphical information about the usage, benefits, and return on investment of the Binalyze AIR in the enterprise company.
-
-
Progress Monitoring was added to InterACT secure remote shell
-
Investigators can track the progress of the command and estimate how much time is left on the interACT shell
-
-
AIR Agent Proxy Support
-
AIR agent automatically identifies the proxy configuration on the endpoint and configures itself to access the required services over the proxy service.
-
Enhancements
-
Miscellaneous package and dependency updates
Fixes
-
Several bugs fixed
AIR 3.1
Features
-
Golden image option was added to AIR Agent installation
-
AIR agent is now compatible with installation via a golden image for new device deployment. With this feature enabled, an administrator can prevent potential connection and availability problems that may have previously occurred on the AIR console for machines installed from a golden image.
-
-
New File System Enumeration evidence for Linux and macOS
-
Investigators can list the creation, modification, and access dates and times of the files and folders on the Linux and macOS filesystem as CSV files.
-
Enhancements
-
Baseline Comparison Reporting
-
Collapse/Expand All items under the Acquisition Profile section.
-
Acquisition Profile information was added to the Tasks list under the Endpoint details page.
-
YARA 4.2 update
-
FTPS support for full disk image
-
SSL/TLS proxy server support was enhanced
AIR 3.0.5
Features
-
RFC-3161 compatible evidence signing for the chain of custody
Enhancements
-
New Asset status, "Off-Network," added
-
AIR Console domain address updates are enhanced
-
New evidence types added
-
Docker Artifacts for Linux OS
-
Browser History Artifacts for Linux OS
-
Browser History Artifacts for macOS
-
RAM image collection for Linux
-
-
Agent uninstallation and purge operations are enhanced
-
Multi-file upload for Off-Network devices
-
Path of the evidence files added
-
Local IP addresses added to the endpoint details page
-
The full disk image for macOS
Fixes
-
Case activity reporting to Binalyze cloud services [credit: Nixu]
-
DNS and ICMP Protocols are filtered when Endpoint Isolation
AIR 2.10.2
Features
-
AWS EC2 one-click agent deployment
-
Cloud forensics - Azure VM support
-
Azure VM one-click agent deployment
-
Auto Asset Tagging based on hostname, IP address, and subnet
-
Auto Asset Tagging based on custom rules with osquery builder
-
Linux full disc image via interACT
Enhancements
-
7x speed improvement for most evidence acquisitions on macOS and Linux
-
You can now upload multiple YARA rules at once
-
Improved troubleshooting logs
-
Token support for MFA
Fixes
-
Fixed an issue where sometimes recycle bin collection would fail
-
Fixed an issue that prevented baseline comparison on unreachable endpoints
-
Other minor bug fixes
AIR 2.9.1
Features
-
Added ability to enumerate Amazon AWS EC2 assets
-
Added Yara triage support to macOS assets
-
Added Baseline comparison for macOS assets
-
Added full disk image collection with interACT for Windows assets
Enhancements
-
Added ability to duplicate acquisition profiles
Fixes
-
Fixed an issue where notifications were not shown about tasks in non-default Organisations
-
Fixed the wrong warning message when deleting a task from a case.
-
Fixed an issue where the user couldn't see the baseline comparison report even though the baseline acquisition task was finished.
-
Fixed the name column sorting in the interACT Library
AIR 2.8.2
Features
-
Added off-network Acquisition and Triage with portable agent
-
Added interACT for macOS
-
Added Tamper Detection for macOS agent
Enhancements
-
API now includes endpoints for Policy, Auto Asset Tagging, Triage Rules, and Users (Docs)
-
interACT shell now supports backslash (\) for newline
-
Updated and improved the powershell deployment script
-
Improved efficiency of e-Discovery and custom content collections
Fixes
-
Fixed an issue where some users were not able to upload files to the interACT library
-
Fixed an issue where sending the same acquisition twice to the same timeline would result in duplications
-
Fixed an issue where an evidence repository that’s in use in a policy could be removed from the console
-
Fixed limitation on username length
AIR 2.7.0
Features
-
Added support for Apple macOS assets
-
Added Chromebook standalone collector (credit: Yuta K.)
-
Added ESXi standalone collector (credit: Andres S. and Mason T.)
Enhancements
-
Case selection is now optional with an Enterprise or MSOC license
-
API now includes endpoints for Repositories, Baseline, Case and Organizations (Docs)
-
Improved the retry process for interACT’s get and put commands
Fixes
-
Fixed issue with downloading files with special characters via interACT
-
Fixed acquisition history graph on the dashboard
-
Fixed other minor functionality and UI issues
-
Fixed UTC time mismatch in DRONE for Windows event logs and event records
-
Fixed DRONE stability issue when using keyword search
AIR 2.6.1
Features
-
Added asset baseline forensic comparison
-
Added support for FTPS evidence repositories
-
You can now have interACT sessions with isolated Windows endpoints
Enhancements
-
Added new evidence and artifact types to Windows acquisition
-
All active interACT sessions are now ended when interACT is disabled from settings
-
Added "New Rule" shortcut to Triage assignment screen
-
Added keyboard support for confirming and dismissing popups (Enter/Esc)
-
Improved evidence compression performance
-
Enabled option not to compress evidence on collection
-
Upgraded interACT curl executable to version 7.83.1
-
Upgraded interACT osquery executable to version 5.2.3
-
Improved performance of agent installation on Windows
Fixes
-
Improved Auto Asset Tagging task assignment
-
Improved UI performance in various locations
-
Improved security of sensitive credentials saved in the AIR setting
-
Fixed an issue with the status of the agent update task
-
Fixed a bug in the interACT zip command
-
Fixed a minor bug in unique case directory creation on endpoints
-
Fixed other minor bugs
AIR 2.4.0
-
Added DRONE support for Linux
-
Added Sigma rule triage to Linux
-
Added shareable deployment feature
-
Added new organization management page
-
Added osquery command to interACT
-
Added mkdir command to interACT
-
Added sort and tree options to interACT pslist command
-
Added SSL Enforcement for accessing AIR.
-
Added auto asset tag rules for Apache, Redis, Mysql and Rabbitmq
-
Added tamper detection type to audit log description
-
Added filtering endpoints by label
-
Added filtering audit logs by endpoint name
-
Added TACTICAL and DRONE KB download links
-
Added required privileges section to interACT command help pages
-
Improved endpoint update performance
-
View and Update Organization privileges moved from system privileges to user privileges
-
Hardened to prevent less-privileged users from accessing sensitive settings data
-
Upgraded interACT curl executable to version 7.82.0
-
Improved tamper detection
-
Improved triage to allow the same Yara rule name in different rulesets
-
Added time frame limit to DRONE Event Records Analyzer
-
Improved DRONE Ransomware Analyzer performance. Added total and per channel limit for Events of Interest and Event Records analyzer.
-
Fixed a minor issue on global search
-
Fixed evidence repository path validation bug
-
Fixed Endpoint label delete issue
-
Fixed e-Discovery patterns search issue
-
Fixed interACT curl command's missing CA certificates on Windows
-
Fixed a bug in sigma triage to kill DRONE process when task is canceled
-
Fixed an issue with the DRONE Linux x86 build.
-
Fixed other minor bugs
-
UI/UX improvements
AIR 2.4.0
Features
-
Added e-Discovery collection to acquisition profiles (credit Yalkin D.)
-
Added Tamper detection to agent
-
Added agent support for Linux arm64 (aarch64)
-
Added curl command to interACT
-
Added hex command to interACT
Enhancements
-
Added IP Address column to Endpoint table
-
Added silent installation tooltip for SCCM agent deployment
-
Added endpoint name to audit log filter
-
DRONE keyword search capability is now more visible
-
Improved zip command in interACT - Now zips to folder
-
Added new metrics for case report memory section
Fixes
-
Fixed unquoted service path issue after a config update (CVE-2021-42563)
-
Fixed minor issues on timeline export
-
Fixed duplicated user validation issue
-
Fixed evidence repository name and path validation issue
-
Fixed system resource usage not updating in interACT session issue
-
Fixed renaming evidence repository issue
-
Fixed an issue that allowed task assignment to endpoints with an old agent
-
Fixed webhook addresses not updated after a change of console address
-
Fixed SFTP current directory support
-
Fixed opening report issue in Safari browser
-
Fixed minor issue on Sigma rule parser
-
Fixed minor issue on Drone table
-
Fixed minor UI issues
AIR 2.3.5
Features
-
Added Sigma rule triage for Windows
-
Added autocomplete functionality to interACT
-
Added ServiceNow support to webhooks
-
Added new privilege to allow changing endpoint label
-
Added auto asset tag rules for Docker and Kubernetes
-
Added version information to settings
-
Added ability to handle Unicode file paths in YARA scanner
-
Added ability to specify a temporary staging directory for acquisition tasks that use evidence repository
-
Improved evidence collection on low capacity endpoints by letting AIR automatically select the volume with the greatest available free space (credits: Babak M.)
-
Improved evidence repository background upload mechanism with persistent retries
-
Improved case export functionality
-
Fixed minor memory leak of canceled tasks
-
Fixed minor logging issues
-
Fixed interACT exec command stdin issues on Windows
-
Fixed a bug related to listing unsupported drone analyzers
-
Fixed case filter issue
-
Fixed policy list on task creation, missing policies
-
Fixed case-sensitive username issues
-
Fixed case day counter
-
Fixed minor bugs on the report
-
Fixed other minor bugs
AIR 2.3.0
Features
-
InterACT: A cross-platform remote shell session capability that allows the users to run commands on remote endpoints for triage, mitigation, and remediation purposes in situations such as cyber incident response activities.
-
Improved windows agent installation
-
Improved endpoint tag assignment
-
Increased timeout duration for Azure Blob Storage
-
Fixed incorrect tag-endpoint count
-
Fixed scheduled instant execution
-
Fixed invalid SFTP port
-
Fixed returning wrong http status code for invalid evidence repository Id
-
Fixed organization search criteria
-
Fixed timeline wrong date range issue on export
-
Fixed multiple role assignment issue on UI
-
Fixed showing "Reset filter" button in the timeline
-
Fixed organizations tag gaps on the UI
-
Fixed privilege hierarchy issue between organization and global admin roles
-
Fixed not showing 404 page for case section
-
Fixed webhook URLs display issue in some cases
-
Fixed duplicated start date field in scheduled task detail
-
Fixed no link issue on "see details" text on Settings > Connection page
-
Fixed broken KB links for Webhooks and SSO
AIR 2.2.1
9 December 2021
-
Added Slack integration support
-
Added Mattermost integration support
-
Fixed timeline sort issue
-
Fixed viewing case.ppc issue on failed tasks
AIR 2.1.5 (RC)
25 November 2021
Features
-
Added exporting endpoints as CSV
-
Added exporting cases as CSV
-
Added exporting case activities as CSV
-
Added exporting case notes as CSV
-
Added exporting case endpoints as CSV
-
Added exporting audit logs as CSV
-
Added exporting timeline events as CSV
-
Added Yara external variables and removed yara+ modules (file, process)
-
Upgraded Yara to 4.1
-
Enriched triage case report for file matches for Linux
Enhancements
-
Added webhook support for Elasticsearch Logstash Kibana (ELK)
-
Added webhook support for SumoLogic
-
Improved task queues
-
Improved triage performance
-
Improved handling of cancel tasks
-
Improved connection timeouts
-
Improved log rotation
-
Improved log format
-
Improved logging
-
Improved Triage case report
-
Updated the application icon for the Windows agent
-
Added timeout for evidence repositories on agent
Fixes
-
Added retry for agent HTTP requests
-
Added retry for failed case file uploads
-
Introduced Linux systemd service restart on failure
-
Fixed compression progress reporting
-
Fixed HTTP response close
-
Fixed a race condition for HTTP transport
-
Fixed progress reporting
-
Fixed self match possibility of custom content collection for Linux
-
Fixed misc. minor bugs
AIR 2.1.5
18 November 2021
-
UI/UX improvements on case containers
-
Fixed minor bugs related to case containers
-
Fixed drone autopilot issue on scheduled tasks and webhooks.
-
Fixed a bug about using azure storage as evidence repository on linux agents
AIR 2.1.0 (RC-2)
9 November 2021
-
Added additional functionality to cases feature
-
Minor fixes and improvements
AIR 2.0.5
1 November 2021
-
Added FQDN support for console address
-
Added a Quick Intro guide to help new users get started with AIR
-
Fixed an issue on SSO with 8443 port
-
Console migration process moved to task logic
-
Minor Linux agent fixes:
-
Minor http timeout fix
-
Minor triage command line parameter fix for excluded files
-
Visit poll interval overflow fix for 32bit architectures
-
-
Minor Windows agent fixes:
-
Minor improvement on isolation
-
AIR 2.1.0 (RC)
12 October 2021
New:
-
Added case container feature
-
Added FIS license support
Fixes:
-
Fixed a minor issue related to the auto-asset-tagging feature
-
Fixed organization admin privileges issue
-
Minor UI/UX fixes
AIR 2.0.1
22 September 2021
This is the stable version of the latest RC (v2.0-RC)
In this version;
-
Added new predefined acquisition profile: Compromise Assessment
-
Added deployment script support for Windows agents
-
Added webhook parser for Cortex XSOAR and Splunk Phantom
-
Added new evidence type for Windows agents: Collecting USB Storage History
-
Improved license validation messages
-
Improved temporary path usage for Windows agents
-
Fixed a bug related to timeline event count
-
Fixed a bug related to sending events to syslog
-
Fixed a bug related to canceling Auto Tag Asset task on Windows agents
-
Major performance improvements
AIR 2.0 (RC)
9 September 2021
New:
-
Added AIR-DRONE Integration (available only for acquisition and timeline for now) - rapid keyword searching, anomaly finding, scanning SIGMA rules live directly on any endpoint, and many other DRONE features are available now in AIR.
-
Added Auto Asset Tagging feature - tag your assets automatically by the conditions you provide.
-
Added Off-Network Endpoints feature - add and filter off-network endpoints.
-
Added PPC Import to Timeline feature - import PPC files collected from offline or online environments to Timeline.
-
Added IP Restrictions feature - restrict access to the AIR Console based on IP addresses or IP blocks.
-
Added UI Port Splitting feature - enables you to serve AIR Console and Endpoint requests from separated ports. With this feature, you can create separate firewall rules in AIR.
-
Added Drone findings on the Timeline
-
Added SMB Repository Support for Linux
-
Added Pardus Linux Support
-
Added Super glob meta (double star) support for custom content
-
Added IP Restriction Reset Script
-
Added an ability to download case reports from the endpoint detail task page
-
Added hashes.csv file that contains hashes of the files in the case report
-
Added detailed step by step task statuses (Processing, Compressing, Uploading, Analyzing)
-
Added support for .pfx, .der SSL certificate types
-
Added supported Linux distributions information to deploy the page
-
Added "Send to Timeline" action to Acquisition tasks
-
Added displaying support for PPC file metadata
-
AIR UI has a new design layout now
Improvements:
-
Improved more user-friendly error messages
-
Improved database connection functionality on backend
-
Improved case report view options on the endpoint detail page
-
Improved global search bar visibility for each page
-
Improved notification module "Mark All as Read" accessibility
-
Improved showing EULA in AIR setup
-
Improved and simplified AIR deployment with Docker for Linux
-
Improved performance while opening the Case Report.
-
Improved SSL Certificate installation
-
Minor improvements/fixes on case report
-
Upgraded MongoDB version to 4.4.7
Fixes:
-
Fixed an issue related to uninstallation of windows agent manually
-
Fixed LDAP issue occurring while trying to login AIR with:
username@domain format -
Fixed task queue cancellation
-
Fixed Proxy SSL issue
-
Fixed organization name update issue
-
Fixed organization filter bug on the policy creation page
-
Minor UI/UX fixes
AIR 1.8.3
18 August 2021
-
Minor changes and improvements
Go to knowledgebase to learn how to migrate from v1.7.61 to v1.8
AIR 1.8.2
17 August 2021
This is the stable version of the latest RC (v1.8.0-rc)
In this version;
-
Added AIR CLI Support
-
Added to restore using a backup file support
-
Added to reset local user password support
-
-
Improved AWS S3 Bucket upload on Windows agent
-
Improved Custom Content Collection on Windows agent
-
Fixed some minor bugs
Go to knowledgebase to learn how to migrate from v1.7.61 to v1.8
AIR 1.8.0 (RC)
14 July 2021
New:
-
Added Docker-based installation support. Once a stable version of v1.8 is released, docker will be the only deployment option. Since then, the MSI installer will no longer be available. Our knowledge base page is available to show how to install the new version of AIR
-
Added multiple organization support.
-
Added stateless queue-based background worker system.
-
Added device name and os on agent visit requests.
-
Added deployment token to deploy endpoints more secure way.
-
Added some rules to prevent confusion and irregularity on users/roles (Only Global Admins can create Roles, predefined roles cannot be updated).
Improvements:
-
Added ability to unisolate an endpoint, whether it's already isolated or not, for easier troubleshooting.
-
Added predefined roles: Organization Admin, L1&L2 Analyst, L3&L4 Analyst, Maintenance Engineer.
-
Added authorization guard for unauthorized users while accessing organization-specific resources and deployment-related pages.
-
Optimized all database indexes for the organization system.
-
Moved policy priority-based config to order-based config.
-
Improved the stateless task scheduler.
-
Improved create tag rest endpoint for organization system.
-
Improved policy-endpoint match stats.
-
Improved caching by moving it from in-memory to a queue-based infrastructure.
-
Improved the backup feature.
-
Updated policy priority/order to clear up the confusion
-
Removed default SMTP connection, users have to enable the SMTP settings to send emails such as password reset
-
Improved auto-isolate operation after reboot
Fixes:
-
Fixed task data error on getting task by id.
-
Added aborting existing TCP connections after Isolate operation
Additional instructions for existing customers:
-
Once a stable version of v1.8 is released, migration documentation and technical support will be provided for existing customers.
AIR 1.7.61
12 July 2021
-
Fixed NATS blocking call problem.
-
This is the last AIR Console version that supports the MSI installer. In future releases, Docker will be the only deployment option.
AIR 1.7.60
2 July 2021
-
Fixed password reset bug.
-
Improved endpoint console address migration feature.
AIR 1.7.55
21 June 2021
-
Added ability to change the console address to migrate endpoints to a new AIR instance.
AIR 1.7.50
This is the stable release of the previous RC version (v.1.7.45)
9 June 2021
-
Fixed a bug upgrading endpoints with old version to newer version
-
Fixed notifying NATS for the endpoints that need to be upgraded to the new version
-
Fixed a bug regarding database backup
-
Added support for validating settings for Azure Blob Storage and AWS S3
AIR 1.7.45 (RC)
27 May 2021
-
New Feature: CSV import support for Timeline
-
New Feature: Amazon S3 Bucket evidence repository support
-
New Feature: Azure Blob Storage evidence repository support
-
New Feature: LDAPS integration support
-
Changed Triggers to
Webhooks -
Added Sources field for Investigation
-
Added support for deleting timeline resources
-
Added LimaCharlie Webhook support
-
Added new predefined YARA rule:
NSA Mitigating Webshells -
Added name field to evidence repositories
-
Improved timeline filtering
-
Improved timeline performance
-
Improved progress reporting based on percentage and time on Linux agent
-
Improved recursive directory walk when compressing case directory on Linux agent
-
Improved isolation task assignment validation
-
Improved task cancellation for network share evidence repository on Windows agent
-
Improved SFTP upload on Windows agent
-
Fixed delay on task receiving after an agent is upgraded to a new version
-
Fixed deploy script bug for non-HTTPS servers
-
Fixed minor bugs on Linux agent
-
Fixed an issue in YARA scanner on Windows agent
AIR 1.7.41
6 May 2021
-
Minor bug fixes
AIR 1.7.40
27 April 2021
-
New feature: AIR-QRadar integration. Now, an acquisition can be started by triggering AIR via QRadar (credits: Esra Kulüp)
-
New feature: Added Roles and Privileges. Starting from this version AIR contains 70+ user privileges for more fine-grained control
-
New feature: Added backup support for case reports and config files. (Database backup is already available beginning from v1.7.16)
-
New feature: Added AES encryption option for backups
-
New feature: Added SFTP support to store backups on the remote server
-
New feature: Added performing bulk operations on the selected endpoints (adding/removing tags, deleting endpoints, starting acquisition triage, and much more. credits: Babak Mirzahosseiny)
-
New feature: Added triage support to Linux. Now, the file system and memory can be scanned using YARA rules. (credits: Hilko Bengen (https://github.com/hillu/) Author of go-yara (https://github.com/hillu/go-yara))
-
New feature: Added Custom Content collection from Linux distributions
-
Added progress update for compression and SFTP upload process on Linux
-
Added sending matched triage rules to Syslog
-
Added advance filter options to data grids
-
Added auto-generated shell script to facilitate Linux deb and rpm packages deployment
-
Added AIR integration guideline to documentation
-
Improved policy creation UI & UX
-
Improved setup process UI & UX
-
Improved custom SSL certificate information
-
Improved task completion status UX
-
Improved nats communication in agent
-
Implemented more secure cookie-based authentication
-
Optimized Audit logging performance
-
Optimized Syslog bulk processing performance
-
Fixed changing proxy settings when the license is lockdown
-
Fixed an issue in the agent installer
-
Fixed some security vulnerabilities
-
Minor changes and bug fixes
AIR 1.7.35
31 March 2021
-
New feature: GNU/Linux support for Debian and Redhat based distributions (Preview)
-
New feature: Added compression and encryption support for evidence
-
New feature: Added policy support that gives you the ability to manage evidence repository location, compression, encryption, and CPU limit based on rules (credits: Turkcell CDC)
-
Added extended file information for triage files
-
Added dependecy checking to evidence repository deletion process
-
Added linux acquisition evidence list
-
Added "Use options provided in policies" and "Use custom options" choices to the acquisition, triage, trigger process
-
Added platform column to endpoint datagrid
-
Added platform, isolation status, and policy filters to endpoint page
-
Added Linux deploy steps to deploy page
-
Added assigning log retrieval task to offline endpoints.
-
Optimized caching to minimize performance bottlenecks caused by high request load
-
Optimized security token check performance
-
Optimized concurrent message handling on Nats server
-
Refactored worker pool to works based on priority
-
Refactored the endpoint task queue to work with the task configs in policies and custom configs
-
Removed patrol from AIR
-
Fixed XSS exploit on audit logs
-
Fixed the performance bottleneck on the task progress update process
-
Fixed a memory leak in the visit process on the windows agent
-
Fixed a problem in windows agent installation version check
-
Updated EULA
-
Minor UX improvements
-
Minor bug fixes
AIR 1.7.31
1 March 2021
-
Fixed the bug related to task assignment to endpoints that are associated with multiple tags
AIR 1.7.30
25 February 2021
-
Improved triage match results
-
Improved AD sync performance
-
Improved audit log db write transactions
-
Improved license capacity checks
-
Improved LDAP login
-
Highly optimized task core module performance
-
Highly optimized endpoint task queue memory usage
-
Highly optimized audit log storage
-
Highly optimized realtime task assignment to endpoints
-
Optimized logging on agent
-
Optimized debugging log on worker tasks
-
Optimized Agent Installer download performance
-
Optimized task result upload performance
-
Optimized db bulk operations
-
Optimized triage rule storage
-
Optimized task storage
-
Refactored worker core module
-
Fixed an issue related to sending triage task result
-
Fixed performance issue caused by Patrol module
-
Fixed disappearing endpoint tags after AD sync issue
-
Fixed loading up tasks to endpoint queue issue caused by db migration
-
Fixed the register required bug that is caused by latency on endpoint registration
-
Fixed the performance issue on visit requests caused by agent update load balancer
-
Fixed investigating same endpoints multiple times in the same investigation
-
Fixed security token mismatch bug on visit requests
-
Fixed the bug caused by reloading task details on the UI
-
Fixed the bug related to license validation for online and offline environments
AIR 1.7.24
27 January 2021
-
Fixed a critical issue on the task assignment module
AIR 1.7.23
24 January 2021
-
Improved endpoint connection error logging
-
Changed max memory cache size to maximum
-
Highly improved memory usage of the endpoint task queue
-
Increased node's memory usage limit to 6GB
-
Reduced effect of long-running tasks on the starting speed of the application
-
Fixed performance and memory issue on sending events to Syslog and audit logs
-
Fixed a minor bug on the endpoint registration issue
-
Fixed a minor bug on fix endpoint issue task
-
Fixed a minor bug on the installer
AIR 1.7.21
18 January 2021
- Fixed an issue in UI
- Other minor bug fixes and improvements
AIR 1.7.20
14 January 2021
-
Fixed minor bugs
AIR 1.7.16 (RC)
11 January 2021
-
Added getting endpoint system resources feature
-
Added database backup feature that allows admin to create database backups regularly (credits: Turkcell CDC)
-
Added version column to the endpoint page
-
Added two new endpoint issue types
-
Added agent update management feature (credits: Turkcell CDC)
-
Added capability to fix registration issue for endpoints that re-installed
-
Improved error report sending on the installer
-
Improved offline license check
-
Improved endpoint issue filter
-
Improved dashboard page statistics
-
Improved automatic page data polling
-
Highly improved backend and agent logs
-
Improved re-upload task mechanism
-
Fixed an issue on triggers that cause not to ignore recurring requests
-
Fixed getting 404 when trying to download an external resource from the report
-
Fixed an issue in task fail upload condition
-
Fixed an exception in downloads collector
-
Other minor bug fixes and improvements
AIR 1.7.13 (RC)
29 December 2020
-
Fixed an issue in agent installer
-
Other minor bug fixes and improvements
AIR 1.7.12 (RC)
22 December 2020
-
Highly improved Yara Scanner speed
-
Improved getting agent logs from AIR
-
Improved process collector
-
Fixed an issue in Yara Scanner
-
Fixed an issue in Prefetch collector
AIR 1.7.11 (RC Sunburst Edition)
17 December 2020
-
Fixed minor typo
AIR 1.7.10 (RC Sunburst Edition)
17 December 2020
-
Added FireEye Red Team Tool Countermeasures Yara Rule
-
Added FireEye Mandiant SunBurst Countermeasures Yara Rule
-
Added support for both filesystem and memory triage
-
Added support for getting agent logs from AIR
-
Added support for agent log rotating
-
Highly improved AIR backend for concurrent operations
-
Fixed an issue in triage results
-
Fixed a minor issue in license
-
Other minor bug fixes and improvements
AIR 1.7.8 (RC)
14 December 2020
-
Fixed an issue in event log parser
AIR 1.7.7 (RC)
10 December 2020
-
Added Log Retrieval action to endpoint
-
Added Timeline action to endpoint group and endpoint tag tree
-
Added Reset Password support for users
-
Added scroll support for timeline
-
Added downloading case entries from report
-
Improved TimelineIR experience
-
Fixed minor install/uninstall bugs
-
Fixed trigger recurrence bug
-
Fixed other minor bugs
-
Removed setting AD and proxy configs from the installer
AIR 1.7.6 (Beta)
3 December 2020
-
Minor improvements and bug fixes
AIR 1.7.4 (Beta)
30 November 2020
-
Fixed an issue in event log parser
AIR 1.7.3 (Beta)
27 November 2020
-
Added support for downloading report as HTML (credits: Turkcell CDC)
-
Improved Quick Acquisition Profile
-
Improved agent update mechanism (credits: Orhan Solak - Barikat Cyber Security)
-
Fixed an issue in agent task processing mechanism (credits: Burak Karapınar - HAVELSAN)
-
Fixed an issue in agent manual uninstallation (credits: Orhan Solak - Barikat Cyber Security)
AIR 1.7.1 (Beta)
20 November 2020
-
Added TimelineIR feature
-
Added Binalyze Patrol feature
-
Added audit logs feature
-
Added role-based access control
-
Added "Acquire Evidence", "Schedule Acquisition", "Triage" and "Delete Endpoint" actions by tag
-
Highly improved agent performance
-
Highly improved agent memory usage
-
Improved settings page to separate The Users, License, and Evidence Repositories pages
-
Improved case file upload to handle .ppc files
-
Improved the installer prerequisites to handle the newer version of NodeJS
-
Improved debug logs
-
The minimum memory requirement for the AIR server increased to 8GB
-
Other minor bug fixes and improvements
AIR 1.6.14
13 October 2020
-
Added support for parsing SRUM Application Resource Usage
-
Added support for parsing SRUM Network Data Usage
-
Added new event records
-
Added MAC time to crash dumps
-
Added Custom Content collection from all drives (credits: Mason Toups)
-
Added Triage on all disk drives (credits: Mason Toups)
-
Added host content to report
-
Added export process table as CSV (credits: Alexander Jarvis)
-
Added Last Write Time for Installed Applications
-
Added support for CPU usage limitation (credits: Turkcell CDC)
-
Added Refresh button to the endpoint groups section
-
Added Delete All Tags button to the endpoint tags section
-
Added Delete button to all detail pages
-
Improved settings page design
-
Improved design of table action buttons
-
Improved Browser History acquisition
-
Improved Network Share connection check
-
Improved exception handling
-
Fixed an issue with event logs
-
Fixed WMI query exception problem
-
Fixed Downloads section processed count
-
Fixed an issue with timestamping
AIR 1.6.11
27 September 2020
-
Improved endpoint tags
-
Improved installer (credits: Babak Mirzahosseiny)
-
Fixed LDAP user login authentication (credits: Turkcell CDC)
-
Fixed LDAP endpoints register problem (credits: Turkcell CDC)
-
Fixed enable/disable debug logging bug
AIR 1.6.9
17 September 2020
-
Added feature of adding tags to endpoints (credits: Yalkın Demirkaya)
-
Added LDAP Sync option to endpoint group tree
-
Added refresh button to the endpoint tags section
-
Added delete tag action to the endpoint tags section
-
Added New Profile button to acquisition profiles dropdowns
-
Improved server logger to make logs more readable
AIR 1.6.8
8 September 2020
-
Added the Recent Tasks section to the dashboard
-
Added task assignment delete option
-
Added Scheduled Acquisition edit option
-
Added confirmation modal to Active Directory settings
-
Added status line to the task detail page
-
Added select all option to triage list of the endpoint
-
Added uninstall task assignment for unmanaged endpoints on a visit request
-
Added onetime scheduled task removal after execution
-
Added task execution history to dashboard backend API
-
Added task assignment removal to backend API
-
Added nats server port status checker job
-
Added match count stats to task details
-
Added support to login with an LDAP account
-
Added sending user deleted event to Syslog
-
Added e-mail field for the user
-
Improved task removal
-
Improved LDAP sync (credits: Babak Mirzahosseiny)
-
Improved SMTP validation logic
-
Improved server restart logic (credits: Babak Mirzahosseiny)
-
Improved agent https connection (credits: Babak Mirzahosseiny)
-
Refactored task assignment and scheduler
-
Fixed changing LDAP endpoint group after visit request (credits: Babak Mirzahosseiny)
-
Fixed https redirection bug (credits: Babak Mirzahosseiny)
-
Fixed report process tree view
-
Minor improvements and bug fixes
AIR 1.6.4 (Code Name: Sirius)
14 August 2020
-
New backend in NestJS (TypeScript) with 100% unit test coverage
-
New frontend in Vue.js
-
Added auto-complete support for YARA rule editor
-
Added support for YARA rule validation
-
Added group triage feature
-
Added global search feature
-
Added filtering support to all tables
-
Added local search for each page
-
Added security token refresh for triggers
-
Added new evidence types
-
Added new Custom Content collection editor
-
Added required port detection to the installer
-
Added Active Directory server setting alongside domain name
-
Added Memcache for decreasing response times
-
Added support for the upcoming Compromise Assessment feature (PPC file)
-
Added retry feature to agents in case there is no connection to evidence repository
-
Highly improved evidence selection page
-
Highly improved UX for task actions
-
Fixed minor issues in installer
-
Fixed minor issues in the Case report
-
Fixed an issue in NATS
-
Fixed an issue in license handling
-
Fixed Smart Screen warning on agent installation
AIR 1.4.1
17 May 2020
-
Added collection of Autorun locations
-
Added collection of Downloaded Files information
-
Added collection of RDP Cache Files
-
Added port availability check for the installer
-
Added new license models
-
Added support for offline licensing
-
Added support for task cancellation
-
Highly improved report
-
Highly improved calculation on visit interval
-
Improved UI/UX
-
Fixed an issue with timezone handling
-
Fixed an issue in group task assignments
-
Fixed app manifest problem for console service
-
Removed internet dependency from the installer
-
Minor updates and improvements
AIR 1.4
13 April 2020
-
Added support for Triage on FileSystem and Memory using YARA+
-
Added support for installation on Windows 7+ OSes
-
Added support for assigning a task to all endpoints in endpoint groups
-
Added support for sending case report after the task completion
-
Added support for anonymous network share connections
-
Added support for send notifications for failed tasks
-
Added Online filter into endpoints page
-
Added support for network share folder permissions check
-
Added support for updating endpoint details for upgraded OSes
-
Added support for filtering with endpoint groups are added
-
Added resilience to case report sending
-
Added sending match count after triage task completes
-
Added Yara rule validation
-
Added validating Yara rule file
-
Added sending Yara rule error message if the wrong rule provided
-
Added sending duration during the task
-
Highly improved evidence acquisition to network shares
-
Improved agent logs
-
Improved exception handling
-
Improved uninstall task
-
Improved fetching array from JSON
-
Improved network share authentication
-
Fixed an issue in LDAP Sync
-
Fixed unhandled exception with JSON GetValue
-
Fixed unhandled exception
-
Fixed wrong function usage for JSON
-
Fixed an issue with agent log
-
Removed unnecessary console API calls
-
Removed console out messages
-
Removed .NET Core dependency
-
Minor updates and improvements
AIR 1.3.6
26 December 2019
-
Fixed an issue in agent update
-
Fixed an issue in license handling
-
Fixed a UX issue in agent register
AIR 1.3.5
25 December 2019
-
Improved UI/UX
-
Highly optimized client connection handling
-
Highly optimized database operations
-
Added support for Custom Content
-
Added support for Syslog
-
Added console auditing logs
-
Added support for DB migration
-
Added edit button to tables
-
Added endpoint filter links to dashboard statistics
-
Improved license handling
-
Performance optimizations
-
Fixed an issue in LDAP synchronization
-
Fixed an issue leading to duplicate domain
-
Fixed an issue in tasks page showing incorrect endpoint
-
Fixed an issue in task scheduler
-
Fixed an issue in installer test LDAP button
-
Fixed an issue in installer test proxy button
-
Minor updates and improvements
AIR 1.3.3
21 November 2019
-
Improved UI/UX
-
Added validation to settings save
-
Fixed screenshot not captured issue
-
Fixed clipboard not captured issue
-
Fixed UsnJournal not retrieved issue
-
Fixed Active Directory paging issue
-
Fixed multiple Active Directory groups issue
-
Added scroll to Active Directory groups
AIR 1.3
19 November 2019
-
Major architectural improvements
-
Major security enhancements (credits: Mehmet İNCE & https://invictuseurope.com)
-
Improved NATS real-time messaging
-
Improved email template
-
Added support for generic Webhook integration with SIEM, SOAR, and EDR products.
-
Added Custom Content Collection
-
Added administrator manifest to installers
-
Added logging for prerequisities
-
Added LDAP / Proxy test buttons to settings
-
Added support for SSL
-
Added 404 Not Found pages
-
Fixed an issue with forgot password dialog
-
Fixed an issue with Console updater
-
Fixed an issue with client IP handling
-
Fixed an issue with environment variables
-
Other minor bug fixes and improvements
Today
30/07/2025
Hotfix 4.43.7
-
Improved FortiAuthenticator SSO integration by fixing group resolution logic for users assigned to a single group, ensuring accurate role and permission mapping during login.
-
Fixed a memory leak in the offline registry hive preparation process, improving stability and memory efficiency during evidence collection.
-
Fixed an intermittent issue in SaaS environments where task files failed to import into IH due to incomplete disk writes, ensuring reliable task processing and archive handling.
-
Fixed an issue where the Interact session worker goroutine could hang indefinitely due to unsent close session requests or network issues, causing WebSocket connections to remain open until a machine reboot, service restart, responder update/uninstall, or task cancellation.
21/07/2025
Hotfix 4.43.6
-
Fixed an issue where the Responder failed to handle certain error or exit codes during specific evidence collection scenarios. This bug caused the Responder to stop the entire evidence collection process prematurely. With this fix, the Responder now handles these errors gracefully, allowing it to continue collecting all remaining artifacts and complete the process partially when needed.
-
Fixed a bug caused by an incorrectly implemented fallback mechanism during page file evidence collection. This fix ensures more reliable behavior in cases where the primary method fails.
-
Fixed an issue that caused an unhandled error in the UAL log parser under certain conditions. The parser now handles such cases more gracefully to prevent unexpected termination.
21/07/2025
08/07/2025
Version 4.43
Features
New Multi-Asset interACT capability
AIR 4.43 introduces a completely redesigned experience for interACT, Binalyze’s remote live shell feature. This update significantly improves productivity by allowing analysts to manage multiple live sessions within a single, intuitive interface, reducing cognitive load and streamlining interactive investigations.
This short video shows Multi-Asset interACT in action.
What’s New?
-
Multi-Asset Sessions: Analysts can now open multiple simultaneous interactive shell sessions (up to 50 assets) in a single AIR console window.
-
Command Broadcasting: A new "ALL" tab enables users to send a single command to all live sessions with a single action, eliminating the need to repeat commands.
-
Flexible Layout: The new dockable interACT drawer is:
-
Resizable and movable (top, bottom, left, or right of the screen),
-
Collapsible or maximizable based on user preference or screen space.
-
-
Launch interACT from anywhere: A new interACT button is now permanently available in the AIR header bar, allowing analysts to initiate sessions from any screen.
-
Additionally, in-context launching is supported directly within the Investigation Hub, allowing for live responses without interrupting the current investigation workflow.
-
Session Visibility & Reporting:
-
Flexible session output display: View interACT results per individual asset or use the consolidated “All” tab to see responses from all connected assets in one place.
-
Reports can be generated or exported as PDF or HTML directly from the interACT window.
-
These improvements are already resonating with users and threat-hunting teams who rely on AIR for high-speed investigations. This release positions interACT as a true analyst-first feature with native multi-session awareness.
Real-Time User Online Status Indicators
AIR now displays user presence across the UI to help with team coordination and case visibility:
-
A green dot under the avatar indicates a user is currently online.
-
A gray dot means the user is offline.
-
This indicator appears in the user management table, case views, and other screens where user details are displayed.
This improvement supports collaboration in larger teams and across time zones.
Acquisition Profile Type Visibility
To reduce errors when assigning acquisition profiles to assets, AIR now displays the associated platform(s) for each profile:
-
Windows
-
Linux
-
macOS
This small but impactful change helps ensure analysts select valid profiles for each target asset, especially during baseline or full acquisitions.
Enhancements
Investigation Hub - Global Filters Repositioned
To improve efficiency, the Global Filters have been relocated from the secondary menu to the top of the Investigation Hub, immediately below the section title, ensuring permanent visibility and immediate access.
Also new:
-
‘Evidence Category’ has been added as a Global Filter.
-
These global filters persist throughout user interactions at both asset and case levels.
Investigation Hub - Relative Date/Time Filtering
AIR now supports relative time selection to apply date and time filters in the Investigation Hub. Analysts can quickly select dynamic ranges, such as “Last 5 minutes,” “Last 7 days,” or “Next 30 minutes,” by clicking on the timestamps in Investigation Hub tables.
This enhancement complements the existing absolute date/time filtering (e.g., 00:00–23:59 on a specific date) by offering more flexible, context-aware filtering, particularly useful in timeline reviews and live evidence analysis.
Investigation Hub - Improved Text Selection Actions
We've improved the visibility of contextual search tools that appear when text is selected in tables or details views.
Now clearly visible:
-
Search in the current table
-
Search in the Investigation Hub
-
Google Search
-
VirusTotal Lookup
These actions are now represented with intuitive icons and light animation to reduce the risk of being overlooked.
Binalyze MITRE ATT&CK Analyzer is now at version 9.6.1
Recent updates to the MITRE ATT&CK Analyzer and Dynamo module introduce improved coverage for emerging threats and evasive behaviors:
-
Expanded Detection of MCP Server Activity
New rules detect Model Context Protocol (MCP) server behaviors on Windows endpoints, covering configuration files, environment variables, processes, and network activity, to help identify unauthorized AI assistant access and potential data exfiltration. -
IIS Malware Coverage
Added YARA-based detection for multiple native IIS malware families, including IIS-Raid, RGDoor, IIStealer, ISN, IISpy, and IISerpent, each tuned to the unique traits of these stealthy web server threats. -
ConfuserEx Detection Improvements
Updated rules improve the detection of samples protected by the ConfuserEx .NET obfuscator, enhancing coverage of heavily packed malware. -
Suspicious Service Path Detection
Dynamo now queries all fields when identifying suspicious service paths, improving accuracy in identifying abuse scenarios. -
Minor rule refinements and false-positive reductions were included across the YARA and Dynamo rule sets.
These updates enhance DRONE’s automated assessments and MITRE ATT&CK mapping for faster, more accurate investigations. Full changelog available here.
Fixes
-
Minor UI/UX adjustments across the Investigation Hub, including feedback from usability testing.
-
Stability and layout improvements in task creation screens.
-
Interactive shell drawer display issues resolved for specific browser sizes.
10/06/2025
Version 4.41
New Features and Enhancements
Repository Explorer – Centralized Forensic Image and File Access
A new main menu item, the AIR Repository Explorer, now centralizes access to all disk image data and repository files, replacing the previous per-asset image file management.
Once selected, the Repository Explorer will reveal a secondary menu which lists the available repositories and their contents under Global or Organizational assignments.
Key benefits of this new feature include:
-
A single interface to browse and manage repositories.
-
Download individual files directly to the user's machine.
-
Directly upload files into existing repositories using the Upload File action button.
-
Import any compatible file in the repository to mount as a ‘disk image asset’ using the new "Import Disk Image" action.
-
Improved navigation between global and organization-specific repositories across Azure, AWS S3, SFTP, and SMB.
NB: The Repository Explorer only displays repositories that are configured and available to the logged-in user. For example, FTPS will not appear unless it has been added previously.
This enhancement significantly improves visibility, usability, and operational efficiency.
Fleet AI – AI Agents for Rule Generation and Guided Investigation
Fleet AI marks Binalyze's first major step into Agentic AI for investigation and response automation, introducing our Multi-Expert Agent System (MEAS) architecture to embed specialized AI expertise directly into AIR’s investigation workflows—if and when the user chooses to activate it.
The first of these agents, Fleet Detection Engineer, debuts in AIR 4.41. It can generate validated YARA, Sigma, and osquery rules based on natural language prompts. A contextual memory system enables secure, persistent conversations, enhancing rule accuracy and usability.
If the Triage Rule wizard is open during a Fleet AI session, you can instantly accept and inject a generated rule directly into the wizard for immediate use.
Coming Soon:
-
Deeper AIR integration and task automation, including a DFIR-specific assistant to answer investigation-related questions.
-
Security guardrails for scope control, sensitive data filtering, and secure access.
-
Scalable architecture built with FastAPI, Redis (with pgvector), and Docker/ECS deployment.
-
Bring Your Own AI (BYOAI): Option to deploy Fleet AI on-premise with no Binalyze Cloud connectivity, ensuring complete data privacy.
Search in AIR’s Settings
You can now search across AIR’s Settings section and subsection titles using the new search box located at the top of the Settings secondary menu.
Selecting a result takes you directly to the relevant configuration page, where the matching item will be highlighted.
This small but powerful enhancement makes navigating complex settings faster, easier, and far more intuitive.
User Profile Photos
Users can now upload their own profile images. These will be displayed across the AIR console UI in user-facing areas, such as the user menu, case history, and activity logs. Supported for both regular and SSO-authenticated users, although not synced from the identity provider.
Event Subscription UI Improvements
The Event Subscription configuration interface, found under Main Menu > Integrations > Event Subscriptions, has been refined for improved usability. Enhancements include:
-
Categorized grouping of events.
-
Searchable interface for faster configuration.
-
Improved multi-select and toggle options for greater clarity and control.
Exclude Responder(s) from Updates
The Exclude from Updates feature allows users to prevent selected assets from receiving responder updates. This can be done individually via the More actions menu or in bulk using the bulk action bar—ideal for maintaining a state, managing phased rollouts, or excluding specific assets.
Excluded assets are hidden from update-related actions and skipped by auto-update processes. Their status is clearly indicated on the asset detail page.
To re-enable updates, use the Include in Updates action. The asset will be included in the next update cycle, and update controls will reappear.
NB Any scheduled or manual update tasks are discarded when exclusion is applied. These are not restored automatically—new tasks must be created.
Investigation Hub - Multiple Findings per Evidence
Evidence items can now display more than one finding:
-
A plus (“+”) indicator in the Finding Type column indicates when multiple findings are present for that item.
-
A dedicated "Findings" tab in the details view allows each Finding to be examined independently.
This resolves prior inconsistencies in the representation of evidence and improves investigative accuracy.
Investigation Hub - Contextual Time Filtering
You can now filter any Investigation Hub table by date directly from the column view:
-
Click a date to access options such as “before,” “after,” or “exact.”
-
Applied filters are automatically added to Advanced Filters as additional criteria.
-
Supports all date columns within the Investigation Hub.
Investigation Hub - Launch Asset Actions in the Investigation Hub
You can now launch core AIR actions—such as Acquire Evidence and Triage—directly from the asset name column within the Investigation Hub.
Simply hover over an asset name to reveal a gear icon, then click it to access quick actions instantly.
This streamlined interaction eliminates the need to return to the Quick Start screen, making task initiation faster and more intuitive.
Binalyze MITRE ATT&CK Analyzer is now at version 9.5.0
This update expands AIR’s detection capabilities through improvements to YARA and Dynamo rules:
-
YARA: Added detection for KoiLoader/KoiStealer and hacker tools used in recent campaigns. Includes false positive fixes and new rules targeting Initial Access IOCs.
-
Dynamo: Broadened tool coverage to improve context and correlation in forensic evidence.
These updates enhance DRONE’s automated assessments and MITRE ATT&CK mapping for faster, more accurate investigations. Full changelog available here.
Fixes
This release includes minor fixes and polish items from AIR 4.40 and 4.41, including UI refinements and background performance improvements.
10/06/2025
08/05/2025
Version 4.39
New Features and Enhancements
AIR UI Improvements to Main Navigation
-
Main Menu icons design refresh with written titless visible or hidden option.
-
General Settings, Theme selection, and Account Settings have moved to the Header Bar.
-
The organization settings are relocated to the left side of the Header Bar.
-
The Recent activity and notifications remain in the header bar but as icons only, and when selected, are now in drawers, not pop-up windows.
-
Frank AI has moved from the Main Menu to the header bar.
To see these improvements in action, click here.
MITRE ATT&CK Heatmap
A new MITRE ATT&CK heatmap has been added to the Findings page in the Investigation Hub, providing a visual overview of tactic coverage based on the volume of mapped findings.
-
The heatmap view is configurable: sort techniques by volume (ascending or descending), and toggle the display of empty techniques and sub-techniques to focus your analysis.
New Artifact Parser: Jump Lists (Windows)
We’ve added Jump List parsing to AIR’s existing Jump List collection capabilities, providing critical insight into user activity and file access history on Windows systems. This new parser supports analysis of user behavior by linking applications to accessed files with reliable timestamped evidence.
Jump Lists track files and applications opened by a user, whether it’s a document, a config file, or an executable. Even if the original file is deleted or moved, the artifact remains, offering invaluable forensic context for investigations.
Key capabilities include:
-
Accessed file paths and associated application names
-
Timestamps: first and last access
-
Access frequency counts
-
Link metadata including hostnames, MAC addresses, volume info, and more
When is it useful? - some examples:
-
Insider threat cases: Confirm if a user accessed a sensitive document they deny interacting with.
-
Ransomware investigations: Validate which application or file was opened just before an infection.
-
Deleted file tracing: Reconstruct file access even if the original file is no longer present on disk.
Note:This parser supports analysis of user behavior by linking applications to accessed files with reliable timestamped evidence.
Tornado 1.2.2: Major Upgrade with New Microsoft Collectors + DRONE Analysis Integration
The latest version of Binalyze Tornado brings a significant boost to cloud forensics with powerful new data sources and automated analysis capabilities, making Tornado 1.2.2 our most advanced release yet.
50+ New Microsoft 365 Collectors
This update dramatically expands Tornado's coverage to 99 collectors across the Microsoft ecosystem. Investigators can now collect a wide range of new cloud artifacts, including:
-
Azure Active Directory logs
-
Defender for Office 365 alerts
-
Exchange Online message traces
-
Mailbox audit and permission logs
-
Policy configurations and sign-in events
The full list of collectors is always available directly in the Tornado application.
All available collectors under both admin and user consent modes are now visible before login, improving visibility and ease-of-use when configuring collections.
DRONE Now Integrated with Tornado
Tornado collections can now be automatically analyzed using DRONE, our powerful rule-based analysis engine.
Use DRONE to:
-
Detect suspicious email content (e.g., shortened URLs, unusual attachments)
-
Identify MITRE ATT&CK techniques in Microsoft 365 activity.
-
Automatically tag and score findings (Low/Medium/High) before ingesting them into AIR.
This integration turns raw cloud data into actionable insights without manual triage.
Findings Automatically Appear in AIR’s Investigation Hub
For existing AIR customers, once analyzed, DRONE findings from Tornado are automatically sent to AIR’s Investigation Hub, giving analysts immediate visibility and context alongside other evidence sources.
Read more about Tornado here in the Knowledge Base.
User Groups for Organization Management
We’ve introduced User Groups to simplify and scale user management across organizations in AIR.
With this new feature, Global Admins can create and assign user groups—collections of users that can be linked to one or more organizations. This is especially valuable for environments with complex structures or where group-based access is managed via SSO (Azure AD or Okta).
Key benefits:
-
Centralized control: Assign entire groups to organizations instead of managing users one by one.
-
SSO integration: Groups can sync with AD or Okta groups for seamless role mapping and access management.
-
Role-aware: Users inherit access and roles from their group memberships.
-
Visibility & safeguards: Group-assigned users cannot be removed from an organization directly, ensuring clarity and consistency in access control.
Note: Only Global Admins can create, edit, and manage user groups.
Killswitch – Cancel All Running Tasks
A new "Killswitch" option has been added to the AIR Console under Settings > Danger Zone, allowing users to instantly cancel all currently running, cancellable tasks across the platform—no selection of Assets or Tasks is required.
To prevent accidental use, confirmation is required by typing a case-sensitive phrase, ‘Cancel All Tasks” before execution.
Personal Access Tokens (API)
We’ve improved how users can orchestrate AIR programmatically with new Personal Access Tokens (PATs).
Unlike existing API tokens, which operate independently of user accounts, PATs are directly linked to individual users. Any API actions performed using a PAT are logged as if they were executed by the user themselves, providing clearer audit trails and more substantial alignment with user permissions.
Key benefits:
-
User-bound: PATs inherit the user’s roles, permissions, and organization memberships automatically.
-
Lifecycle awareness: Delete the user, and the PAT disappears. Modify the user’s permissions, and the PAT’s capabilities adjust accordingly.
-
Audit clarity: All actions appear as performed by the user, not just a token.
Note: This is an API-only feature for now—there is no UI available yet.
Confirmation Warning for Large-Scale Tasking
To help prevent accidental bulk operations, AIR now includes a confirmation prompt when tasking affects 70% or more of all assets.
This new safeguard is triggered whenever a task, such as isolation, acquisition, or triage, is set to run against the majority of your asset inventory. Instead of executing immediately, the platform now displays a clear confirmation message, asking you to verify that the large-scale task is intentional.
Key benefits:
-
Accidental prevention: Avoid costly mistakes like unintentionally isolating thousands of assets due to a misconfigured API call.
-
Better control: Reinforces situational awareness before executing high-impact actions.
-
API included: The confirmation requirement also applies to API-based tasking, further reducing automation risk.
Note: This feature is automatically enabled and currently cannot be turned off. We are exploring configurability in future updates to better support smaller environments.
Binalyze MITRE ATT&CK Analyzer is now at version 9.2.2
Here is a summary of the updates since 9.0.1, which was covered in our last release notes:
YARA Enhancements: New detection rules have been added for a diverse range of advanced threats, expanding forensic coverage and improving incident response accuracy:
-
Anubis (Python): A stealthy backdoor linked to FIN7, now detectable through signature-based analysis.
-
QDoor: Backdoor malware targeting Windows systems, often used in persistent attack chains.
-
SectopRAT (ArechClient2): A powerful RAT with surveillance and remote control capabilities.
-
Lazarus APT - BeaverTail & Infostealer: Detection of both command components and information-stealing modules used in high-profile espionage campaigns.
-
StealcStealer (variant): A new strain of credential and data-stealing malware now actively detected.
-
Dunloader (Earth Kurma APT): Detection added for this staging malware used in targeted campaigns.
Dynamo Enhancements - We've also bolstered forensic detection with new rules to identify risky Windows Registry settings, including:
-
Enabled RDP: Flagging systems where Remote Desktop Protocol is active.
-
Unsecure SMB configurations: Detection of outdated or vulnerable SMB protocol usage.
-
Unencrypted WDigest: Identifying legacy authentication methods still in use—often exploited for credential theft.
These additions support faster, deeper compromise assessments and ensure security teams can respond more confidently to complex threats.
Learn more in the Knowledge Base page for MITRE ATT&CK Analyzer changelog
Fixes
Database Migration Performance Issue Resolved
This release addresses the migration performance issue introduced in AIR 4.37 during the transition from MongoDB to PostgreSQL. In certain environments, large volumes of timeline data caused increased database load, potentially leading to application unresponsiveness immediately after upgrade. This issue has now been fully resolved, so upgrades can now proceed as normal.
Flag Export Issue Resolved
We've fixed an issue that caused exported flag files to generate empty ZIP archives, even when multiple flags were selected. You can now export flags reliably for reporting and review.
08/04/2025
Version 4.37
Important Notice: Database Migration
This is a major release that includes a database migration step. As a result, the upgrade process may take longer than usual.
To minimize disruption, we strongly recommend scheduling this upgrade outside of business hours. If you need assistance or have any concerns, please contact Binalyze Support before proceeding.
New Features and Enhancements
Bulk Task Cancellation and Deletion
Managing large volumes of tasks is now faster and more efficient with the introduction of Bulk Task Cancellation. This new capability allows users to cancel one or more tasks directly from the Tasking view using the familiar bulk action toolbar.
To help users narrow down which tasks to cancel, all advanced filters are fully supported, making it easier to locate and select specific task types, names, sources, or statuses. Once multiple tasks are selected, the bulk action bar will automatically appear, along with a task count to indicate how many have been selected for cancellation (note: this refers to the number of tasks, not assets).
As part of the same enhancement, we’ve also introduced Bulk Task Deletion. When using the Delete Tasks option in the bulk action bar, users can choose between:
-
Delete Task Only – Removes the task from the console without affecting the asset.
-
Delete and Purge Local Data – Deletes the task and purges any associated local data from the asset.
These enhancements streamline the cleanup of redundant or misconfigured task assignments, helping maintain a more organized and accurate tasking environment while offering greater control over retained data.
Read more about task cancellation and deletion here in the Knowledge Base.
Investigation Hub – Regex Support Added to Advanced Filters
The Investigation Hub now includes regex (regular expression) operator support within the Advanced Filters section. This enhancement enables more powerful and flexible data filtering across cases, triage results, and evidence views.
How It Works
Regex filtering is available via the existing Contains filter dropdown, with the following operator options:
-
Matches RegEx (case insensitive)
-
Does not match RegEx (case insensitive)
-
Matches RegEx (case sensitive)
-
Does not match RegEx (case sensitive)
These options allow you to create highly granular search conditions, ideal for forensic analysts dealing with variable or loosely structured data inputs.
Read more about RegEx in Advanced Filters here in the Knowledge Base.
Investigation Hub – Import Status Progress Display
Users can now monitor import progress directly within the Investigation Hub as the status is shown in real time next to the case title, providing immediate visibility into the current state of ongoing or newly added tasks.
When hovering over the data import icon, users will now see a clear visual status:
-
A green tick indicates that the import has successfully completed.
-
A spinning circle of dots signifies that the import is still in progress.
This small but impactful addition makes it easier to track case activity at a glance, helping investigators stay informed without switching views or refreshing pages.
Read more about the Secondary Menu here in the Knowledge Base.
Investigation Hub – Keyboard Navigation Now Refreshes Details Pane
We've added this ‘quality-of-life’ improvement to the AIR Investigation Hub based on customer feedback.
Previously, when navigating between artifacts in the center pane using keyboard arrows, the Details Pane did not update accordingly, requiring a manual click to refresh the content. We’ve now addressed this.
With this release:
-
The Details Pane now automatically refreshes when navigating through artifact line items using the keyboard arrow keys.
-
This behavior also applies when the details pane is detached in a separate window, ensuring a consistent experience across both views.
This enhancement makes artifact review faster and more intuitive—just the way it should be.
(Credit: Adam D, Josh T)
Investigation Hub – User Attribution for Individual Exclusions
We've enhanced the Individual Exclusions feature in the Investigation Hub by adding user attribution. Now, when a user manually excludes a Finding, their name is recorded and displayed in the Exclusion Table. This update brings greater transparency and auditability to the exclusion process.
Why it matters:
Users can now easily identify who excluded specific findings—helping teams maintain accountability and better understand investigation decisions.
This builds on the original feature introduced in v4.35, which allowed analysts to exclude findings on a case-by-case basis without needing to define a rule.
Read more about Exclusions here in the Knowledge Base.
API Support for Creating Tags in Triage Rules
Users can now create and categorize triage rules using the public API. This new capability allows tags to be programmatically added during triage rule creation, eliminating the need for manual tagging and enabling more scalable, automated workflows.
Key Benefits:
-
Streamlines triage rule management via automation.
-
Enhances organization with consistent, tag-based categorization.
-
Reduces manual overhead in rule setup.
Binalyze MITRE ATT&CK Analyzer is now at version 9.0.1
Here is a summary of the releases since our last release notes, 5 March – 2 April 2025:
Version 9.0.1
-
Updated detection for SystemBC proxy malware.
-
Enhanced detection of Play ransomware variants and related tools.
-
Additional minor fixes and improvements.
Version 9.0.0
-
New YARA rules targeting China-based APT tools:
-
HUI Loader (S1097), ShadowPad (S0596), SodaMaster (S0627)
-
SparowDoor backdoor and ABYSSWORKER rootkit
-
-
Detection improvements for:
-
Credential theft, brute-force utilities, network discovery, and reverse proxy tools
-
Malware using compromised or revoked digital signatures
-
-
Dynamo has been updated to better recognize commonly used hacker tools in forensic artifacts.
Versions 8.7.0 – 8.7.1
-
Added detection for Winos, a C2 framework used in recent Taiwan-focused campaigns.
-
Improved coverage of ESXi-targeting ransomware variants.
-
New detection for Sosano, a backdoor aimed at aviation, satellite, and critical transport sectors.
These updates continue to strengthen Binalyze’s threat detection arsenal with broader coverage and enhanced forensic insight. For more details, visit the Binalyze MITRE ATT&CK Analyzer changelog.
Fixes
None of note
08/04/2025
13/03/2025
Version 4.35
New Features and Enhancements
Findings - Individual Exclusions
Previously, in the Investigation Hub, ‘Findings exclusions’ were limited to defined rules based on path and description. With this update, AIR now offers greater flexibility with two exclusion methods:
-
Exclusion Rules – The existing capability that excludes an item either only when found in a specific location or regardless of its location based on the finding itself.
-
Individual Exclusions – A new method that allows users to manually exclude any Findings within individual cases, based on their specific needs or investigation requirements without the need to create a rule.
This AIR v4.35 enhancement provides greater control and adaptability when managing exclusions in AIR.
Key Benefits: With this new enhancement, users can now:
-
Individually exclude items with no need for defined rules.
-
Easily view and manage these exclusions through the Exclusion Table in the Investigation Hub. Here the table will show if the exclusion is made by a rule or individual Finding.
-
Bulk removal of individual exclusions can be performed directly within the Exclusion Table.
-
Continue using rule-based exclusions alongside the new method for greater flexibility.
Read more about Exclusions here in the Knowledge Base.
Persistent Saved Filters for Asset Management
Managing large-scale asset inventories is now easier with the introduction of Persistent Saved Filters.
What’s New?
Previously, users could filter assets using preset filters (e.g., Managed Assets, Isolated Assets). However, these preset options were often insufficient for organizations handling thousands of assets, and custom filtering did not persist in the browser between sessions.
Key Benefits:
-
Save custom filters for frequently used asset searches.
-
Quickly apply saved filters to streamline asset management.
-
Take bulk actions or monitor asset status without re-entering the same filter conditions.
-
Use quick actions directly on saved filters for even faster asset selection.
Important Details:
-
Saved filters are ‘per-user’ – Users can only see and manage their own filters.
-
Preset filters remain unchanged – The existing predefined filters are still available.
-
Filters persist across sessions, allowing users to maintain their preferred filtering setup effortlessly.
This enhancement provides greater efficiency, ensuring that users can categorize and take action on assets more effectively.
Read more about using Persistent Saved Filters here in the Knowledge Base.
Bulk User Management Enhancements in Organization Settings
Managing users in Binalyze AIR just got easier! Previously, organization administrators had to remove users one by one, which was time-consuming, especially for large organizations.
Key Benefits:
We have introduced several improvements to streamline user management:
-
Bulk user removal – Select multiple users at once for removal.
-
One-click removal – Remove all users selected on a page in a single action.
-
Advanced user filtering – Filter users by email, username, and role on the Users page and organization settings.
-
Bulk user addition and removal – Easily manage large numbers of users by adding or removing them in bulk.
Why This Matters?
These improvements were developed in response to customer feedback, and mark a further step in enhancing user management efficiency in AIR. Administrators can now manage users more effectively, reducing manual work and improving overall operational efficiency.
Binalyze Tornado - updates and improvements
Version 1.0.12 (5 March 2025)
System Improvements
-
General enhancements to system stability and performance, ensuring a smoother and more reliable experience.
Version 1.0.11 (25 February 2025)
Microsoft 365 Collectors – Expanding forensic visibility in cloud environments:
-
Unified Audit Logs Collector – Added support for collecting Unified Audit Logs from Microsoft 365, providing a comprehensive audit trail for security investigations.
-
Risky Events Collector – Introduced a collector for risky users and risk detections, improving threat monitoring and security analytics.
-
MFA Configuration Status Collector – New collector to retrieve Multi-Factor Authentication (MFA) settings across all users in an organization, helping assess security configurations.
-
OAuth2 Permission Grants Collector – Implemented a collector to gather OAuth2 permission grants, offering better visibility into application permissions and access controls.
Binalyze MITRE ATT&CK Analyzer is now at version 8.6.3
These enhancements bring cutting-edge threat intelligence to your compromise assessments, allowing for faster and more accurate identification of advanced persistent threats (APTs), malware, and evasive attack techniques.
Expanded APT & Malware Threat Intelligence
-
New backdoor detections:
-
Sagerunex (Lotus Blossom APT) – Used against government, telecom, and media targets since 2012.
-
InvisibleFerret & BeaverTail (Lazarus APT) – Deployed in job scam attacks against developers.
-
LightSpy (APT41) – A Windows variant of the well-known espionage tool.
-
Sosano – Targeting organizations in aviation, satellite communications, and critical transport infrastructure.
-
Winos C2 framework – Recently used in attacks on Taiwan-based entities.
-
-
New Rust-based backdoor detection, actively targeting the cryptocurrency sector.
-
Gh0stRAT & FatalRAT updates – Strengthened detection of remote access trojans used in cyber-espionage.
Advanced Forensic Detection & Evasion Countermeasures
-
PowerShell & Scheduled Tasks Enhancements – Stronger identification of malicious command execution and obfuscated scripts.
-
Improved ransomware detection, including ESXi-focused variants and a macOS ransomware masquerading as LockBit.
-
New privilege escalation techniques tracked, such as the Truesight driver abuse used in large-scale defense evasion.
-
Enhanced detection of crypto wallet stealers, securing against browser extension-based threats.
Why This Matters for Your Compromise Assessments and Investigations
Stronger, Faster Threat Detection – Identify sophisticated APTs and malware variants with increased precision.
-
Better Forensic Visibility – Gain deeper insight into cross-platform threats and evasive attack techniques to guide investigations
-
Improved Security Posture – Strengthen defenses to protect high-value assets from emerging cyber threats.
For more details, visit the Binalyze MITRE ATT&CK Analyzer changelog.
Fixes
The following bug fix has been applied:
Asset Duplication Prevention: To prevent asset duplication, we have introduced a new validation mechanism. Assets now send a ‘responderId’ during both registration and visits, allowing the system to detect and block duplicate entries. This enhancement ensures better asset integrity and consistency in AIR.
12/02/2025
Version 4.33
New Features and Enhancements
Dark Mode
A Dark Mode UI is now available in AIR. This feature provides a more comfortable and visually appealing experience, especially in low-light environments. It reduces eye strain during extended sessions and enhances usability while aligning with modern UI standards. Users can now switch between light and dark modes in the main AIR menu based on their preference, improving usability and overall satisfaction.
Data Usage Dashboard - Hierarchical Sunburst View
Understanding data usage in complex environments can be challenging, especially with large datasets. The new Hierarchical Sunburst View in the Data Usage Dashboard offers an intuitive, hierarchical visualization that makes it easier to identify key usage patterns, trends, and anomalies at a glance.
Key Benefits:
-
Clear, Visual Breakdown – Navigate data relationships more effectively than with traditional tables or linear charts.
-
Interactive Exploration – Click on segments to drill down into deeper data layers for detailed insights.
-
Consistent Filtering – All global filters apply to the Sunburst visualization for a seamless analysis experience.
-
Save to Dashboard – Easily save your customized Sunburst views for quick access and ongoing monitoring.
Where to Find It?
The Sunburst View is available under; Settings>Actual Disk Usage in the Hierarchical View tab on the Actual Usage page.
Read more about Disk and Data Usage here in the Knowledge Base.
Enhanced API Token Management with Role-Based Access Control
To improve security and flexibility, API Token Management now supports role-based access control (RBAC), reducing the need for excessive permissions.
Key Enhancements:
-
Global Admins continue to create and modify API tokens.
-
Granular Permissions: Tokens now inherit only the privileges of their assigned role (e.g., read-only or custom roles), preventing over-permissioning.
-
Post-Creation Role Updates: Token permissions can be modified after creation, allowing for dynamic access control.
-
Governance & Security:
-
The role assigned to a token and its creator cannot be deleted unless the token is reassigned or removed.
-
Improved auditability and compliance with least privilege principles.
-
The primary enhancement in this release is the revised role of the API token. Previously, API tokens were automatically assigned the Global Admin role, granting unrestricted access to all APIs. This update introduces role-based limitations, allowing API usage to be tailored according to the selected role. This improvement refines automation workflows and strengthens access control policies.
Event Subscription for Automated AIR Workflows
To enhance automation workflows, AIR now supports Event Subscriptions, allowing users to receive real-time notifications when specific events occur. Previously, while AIR actions could be triggered via API, there was no way to retrieve results automatically, requiring users to log in manually. This limitation made it occasionally challenging to integrate AIR with other tools for fully automated workflows.
Key Enhancements:
-
Event Subscription Mechanism: Users can subscribe to specific events in AIR and receive instant notifications.
-
HTTP Callbacks: When an event occurs, AIR sends a POST request with relevant event data to the user’s specified HTTP endpoint.
-
Seamless Automation: These triggers enable users to automate follow-up actions, such as initiating workflows in external tools.
-
Improved API Integration: Reduces the need for manual intervention, making end-to-end DFIR automation more efficient.
This update ensures that users can build fully automated incident response processes, improving efficiency and operational flexibility.
Read more about Event Subscription in the Knowledge Base.
Security Update for AIR Console Access Control
To address a security vulnerability involving Host header injection, we have implemented more stringent controls on AIR Console access.
Key Points:
-
Access Restriction: The AIR Console will now only be accessible through the specific address registered during the initial setup, ensuring that only legitimate requests are processed.
-
Technical Enforcement: This measure counters manipulations of the Host header that could potentially allow unauthorized access.
-
Configuration Flexibility: For legitimate access needs from multiple domains or IP addresses, users can specify allowable entries via the AIR_CONSOLE_ADDRESSES environment variable.
-
Enhanced Security: This change not only prevents unauthorized access but also aligns with best practices for secure network management.
This update enhances security protocols and provides administrators with better control over access settings.
AIR Responder Support in Windows Safe Mode
The Binalyze AIR Responder can now function in Safe Mode, allowing forensic acquisition even when a system is booted in a restricted state. To enable this functionality, users must register the Binalyze AIR Agent Service before entering Safe Mode.
Key Details:
-
If the machine enters Safe Mode with Networking, the AIR Console connection remains active.
-
Users must add the two Registry Keys before Safe Mode is active to allow tasking via the console.
-
Without these additions, interACT and remote tasking will not work until the Registry keys are added.
-
When using an off-network collector, users can perform acquisitions in Safe Mode without modifying the registry unless remote tasking is required.
Read more about AIR Responder in Windows Safe Mode here.
Binalyze MITRE ATT&CK Analyzer is now at version 8.5.0
Recent enhancements included:
Yara
Enhanced Detection Capabilities:
-
Deceptive Development Backdoor: Detection added for Lazarus APT group's custom backdoor targeting developers via fake job offers.
-
Veeam Credential Dumping Tools: Now detects tools extracting Veeam credentials from MSSQL databases, addressing technique T1555.
-
ValleyRAT Backdoor: Introduced detection for the ValleyRAT backdoor linked to the Silver Fox cybercrime group.
Dynamo
Forensic Analysis Enhancements:
-
Enhanced identification and analysis of hacking tools found during forensic investigations for more efficient threat assessment and response.
We have also implemented minor fixes and performance enhancements to improve system stability and detection accuracy, strengthening our security solutions against emerging threats and enhancing investigation processes.
For more details, visit the Binalyze MITRE ATT&CK Analyzer changelog.
12/02/2025
29/01/2025
Version 4.31.5 Hotfix
AIR version 4.31.5 fixes an issue with our LDAP integration where domain assets did not appear in the Assets section after starting a sync despite successful credential verification. This is fixed, please update to the latest version to see the domain assets correctly displayed.
15/01/2025
Version 4.31
New Features and Enhancements
Investigation Hub Historical Disk Usage Statistics Dashboard
AIR version 4.29 introduced a comprehensive Disk Usage Dashboard in the Investigation Hub. This feature offers real-time, detailed insights into disk usage within the Investigation Hub, categorized by cases, organizations, and evidence types. Additionally, a new Historical Insights view has now been added, providing an enhanced perspective for trend analysis.
Key Benefits:
-
Granular Insights combined with Filters: View breakdowns by organization, case, evidence type, etc.
-
Improved Storage Management: Easily visualize data with pie charts and detailed tables.
-
Historical Views: Analyze trends over time.
-
Report Generation: Export insights as PDF reports for sharing or as CSV files directly from table views.
User Guidance:
-
Access: Available exclusively to Global Admins via the AIR console:
-
Navigate to: Settings > Investigation Hub Disk Usage > Actual Disk Usage or Historical Disk Usage.
-
-
Summary and Filters:
-
Total disk usage is summarized at a glance.
-
Filters include organization, investigation type, platform, evidence type, and category.
-
-
Visual Representation:
-
Pie charts highlight the top nine usage categories, with the remaining items visible via scrolling arrows.
-
This update enhances usability, supports trend analysis, and streamlines disk usage monitoring for better resource management. Read more in the Binalyze KB.
New Data Collectors
-
The following Browser based Data Collectors have been added:
-
Linux: Firefox Extensions
-
macOS: Chrome Extensions, Edge Extensions, Opera Extensions, Firefox extensions, DHCP Settings
-
Windows: Firefox Extensions
-
Tornado - Preview Version
We’re thrilled to announce the Tornado Preview, a standalone desktop application designed to streamline and enhance evidence collection from cloud platforms such as Google Workspace and Microsoft Office 365.
Tornado equips investigators with the tools to effortlessly gather critical artifacts, including email records, user access logs, and administrative actions—key elements for Business Email Compromise (BEC) investigations.
Key Highlights
-
Multi-Platform Support:
Tornado currently supports Google Workspace and Microsoft Office 365, with additional platforms planned for future releases. -
Advanced Collection Capabilities:
Gather essential data types such as email and activity logs across supported platforms. -
Investigation-Centric Design:
Tailored for BEC investigations with rapid evidence collection, optimized workflows, and enhanced incident response capabilities. -
User-Friendly Evidence Collection Interface:
Intuitive design ensures precise, efficient, and reliable evidence gathering. -
Data Analysis Options:
Export data to SQLite for detailed analysis, integrate seamlessly with Binalyze AIR and leverage the Investigation Hub for advanced use cases.
Availability
The Tornado Preview is:
-
For AIR Customers: Available alongside the release of AIR version 4.31 on January 15, 2025, via the Tornado Preview button in the AIR console.
-
For non-AIR customers: A dedicated landing page offers a free preview starting February 10, 2025. Early registration is available to join the mailing list and receive the download link.
For comprehensive details on Tornado’s features and usage, please visit our Knowledge Base.
Binalyze MITRE ATT&CK Analyzer is now at version 8.2.4
Recent enhancements included:
-
Added detection for malicious extensions involved in the Cyberhaven compromise and a broader campaign targeting Chrome extensions for credential-stealing purposes. Blog Post here.
For more details, visit the Binalyze MITRE ATT&CK Analyzer changelog.
15/01/2025
12/12/2024
Version 4.29
New Features and Enhancements
Investigation Hub Disk Usage Statistics Dashboard
-
Overview: AIR version 4.29 introduces a comprehensive Disk Usage dashboard in the Investigation Hub. This feature provides detailed, current insights into your AIR’s Investigation Hub disk usage across cases, organizations, and evidence categories, with a “historical insights” view planned for the next release.
-
Key Benefits:
-
Provides granular insights with breakdowns by organization, case, evidence type, and more.
-
Enhances storage management by simplifying visualization through pie charts and detailed tables.
-
Historical views are available for analysis trends (historical functionality to be added in upcoming releases).
-
Users can generate PDF reports for sharing and record-keeping, as well as export CSV files directly from the table views.
-
-
User Guidance:
-
Accessible exclusively to Global Admins via the AIR console; Settings > Investigation Hub Disk Usage > Actual Disk Usage or Historical Disk Usage
-
Total disk usage summary available at a glance.
-
Filters include organization, investigation type, platform, evidence type, and category.
-
Pie charts display the top nine usage categories, grouping the remainder under “Others.”
-
Clarifying Backward Compatibility in AIR 4.29+
Overview
With AIR 4.29, we introduced a major improvement: decoupling AIR console updates from Responder updates. This gives teams greater flexibility when deploying AIR updates, especially in large-scale environments.
-
What This Means (and What It Doesn’t)
-
Starting with AIR v4.29, the AIR console can be updated independently of Responder updates.
-
All future AIR versions (4.29 and onward) will maintain backward compatibility with Responders that are also on version 4.29 or newer.
-
Responders running versions older than 4.29 (e.g., 2.54.3) are not compatible with certain key features such as:
-
Evidence acquisition
-
Triage
-
interACT
-
Users with older Responder versions will see messages like:
"The asset’s AIR Responder must be updated to accept tasks."
To summarize:
Backward compatibility begins from version 4.29 onwards. If your Responders are still on versions earlier than 4.29, they must be upgraded at least once to benefit from this compatibility model going forward.
Why This Matters
Once all Responders are updated to v4.29+, you’ll no longer need to upgrade Responders with every new AIR console release — simplifying upgrades and reducing operational friction.
Binalyze MITRE ATT&CK Analyzer is now at version 8.1.0
Recent enhancements include:
-
GHOSTSPIDER detection: Added detection for Earth Estries APT's sophisticated backdoor activity. (T1059.003)
-
Driver exploitation identification: Enhanced detection of vulnerabilities like malicious Avast driver usage for defense evasion. (T1547.001)
-
Kernel exploit detection: Improved detection of STEALHOOK and CVE-2024-30088 kernel-level attacks, ensuring quicker response prioritization. (T1068)
-
Real-time threat identification: Live YARA and Sigma scanning now address advanced threats like Medusa ransomware with greater speed and precision.
For more details, visit the MITRE ATT&CK Analyzer changelog.
26/11/2024
Version 4.27.6
AIR now provides configurable encryption for off-network collections. By default, encryption is disabled to streamline the post-collection ingestion process, enabling faster and more efficient evidence handling.
However, for scenarios requiring enhanced security, you can enable encryption during the setup of the off-network collector package. This ensures that sensitive data remains protected while giving you the flexibility to prioritize efficiency when needed.
We believe this update will improve your workflows while maintaining the highest level of security for your investigations.
For more details please see the Binalyze Knowledge Base page Off-Network Responder and please don’t hesitate to reach out to our team if you need further information.
26/11/2024
19/11/2024
Version 4.27
Enhancements
Support for Accounts in Azure AD SSO without Associated Email Addresses
New enhancements to SSO functionality in Binalyze AIR:
-
Editable Organization Details: SSO-authenticated users can now edit user organization details directly within the platform Settings page which will allow the alignment of individual organizations with separate AD groups, providing greater flexibility and improving usability.
-
Automated Azure/OKTA Integration: Organization information will now automatically synchronize from Azure Active Directory and OKTA groups, ensuring consistent, up-to-date user data without manual intervention.
Learn more about SSO integrations here in the Knowledge Base.
New Docker Log Data Collectors
-
Windows, Linux & macOS: Collect Docker Container Logs
-
Linux & macOS: Collect Docker Logs
Learn more about supported evidence and artifacts here in the Knowledge Base.
Binalyze MITRE ATT&CK Analyzer is now at version 7.2.0
Recent YARA enhancements include:
-
Added detection for BianLian ransomware. (T1486)
-
Enhanced identification of credential stealers that collect browser data. (T1005)
-
Enhanced detection of Cobalt Strike. (S0154)
-
Enhanced detection of memory dumpers and scripts designed to extract and decrypt Kerberos tickets. (T1558)
For a deeper dive into our MITRE ATT&CK Analyzer visit the changelog in the Binalyze Knowledge Base.
Fixes
The following bug fixes have been applied:
-
$mft CSV import column ordering issues.
-
Investigation Hub UI options were not always visible.
25/10/2024
Version 4.25.3 Hotfix
Several issues have been addressed today with this Hotfix release two that may have affected costumes are outlined below:
1. Issue Addressed: interACT progress communication with AIR console (VOC-1472)
There was an issue in Responder v2.50.5 where certain interACT commands (get, put, zip, YARA, image) were missing progress information in the Console, though the commands still functioned properly. This is fixed in Responder v2.53.6.
2. Issue Addressed: Case Tasks missing (VOC-1463)
When navigating to a Case with multiple Acquisition, Triage, and InterACT records, the entries briefly appear but then disappear from the screen. This affects all data types, and even refreshing the page does not fix the issue. The count for each category (e.g., Acquisition: 45) also drops to zero unexpectedly.
Recommendations:
Update to AIR v4.25.3 when released to benefit from these improvements.
25/10/2024
22/10/2024
Version 4.25
Enhancements
Edit Scheduled Tasks
The new "Edit Scheduled Task" feature, gives users the flexibility to modify scheduled tasks without starting over. Now, you can easily add or remove assets from a scheduled task on the fly, saving time and improving workflow efficiency.
With the assets selected, the user can proceed to modify the scheduled task’s Setup, Customization, and Follow-up.
This update makes scheduled task management completely adaptable, ensuring a smoother and faster investigation process.
Use offline (off-network) acquisitions for comparison
Baseline analysis with the Compare feature is an innovative feature for proactive forensics and it is now enhanced to support collections from offline assets.
Compare identifies and highlights artifacts added, changed, or deleted between asset snapshots, even when the evidential acquisition occurred while the asset was offline. This proactive approach strengthens security by addressing vulnerabilities early.
Pre-validate Evidence Repository connection before initiating evidence collection
To improve task reliability and save time, we’ve introduced a connection check feature for evidence repositories when initiating acquisition tasks (both scheduled and immediate).
How It Works
When creating tasks such as Acquisition and Acquire Image, if an evidence repository (SFTP, FTPS, Azure, or AWS) is selected, the AIR console will now automatically perform a connection check to ensure the repository is accessible.
If the connection check takes longer than 10 seconds, the check will be canceled, and a warning message will appear, but the task creation will not be blocked.
Users can choose to proceed with the task, even if the repository is temporarily inaccessible, or cancel the task creation.
The connection check does not apply to SMB repositories at this time.
Expanded Color Palette for Custom Flags
Flagging evidence items in AIR has been a popular feature, allowing users to easily categorize and prioritize key findings in the Investigation Hub. However, customers have requested more flexibility with color options for better organization, especially in complex investigations.
We’ve listened! You can now choose any color from a palette for your custom flags. This enhancement gives you more control, enabling better visual distinction of flagged items and improving workflow efficiency. Tailor your flagging system to fit your needs and manage investigations with greater clarity and precision.
Event Log collections now support date configuration for timezone offsets
The new event log collection wizard, introduced with AIR v4.23, has been a great success with users, and we've now enhanced it further by adding the option to select a time zone for collections.
The asset’s browser time zone setting will be used if no time zone is selected.
New Browser Extension Data Collectors
We have expanded the evidence-collection capabilities in AIR by adding several new browser extension collectors for Windows:
-
Edge Extensions
-
Opera Extensions
-
Brave Extensions
-
Vivaldi Extensions
-
QQ Extensions
Binalyze MITRE ATT&CK Analyzer is now at version 7.1.0 (18/10/24)
Recent YARA enhancements include:
-
Added detection for DragonForce ransomware binaries. (T1486)
-
Added detection for Angry IP Scanner. (T1018)
-
Added detection for Clop and MedusaLocker ransomware binaries observed in September 2024. (TA0040)
-
Enhanced detection of Defender Control hack tool often used to disable Microsoft Defender. (T1562.001)
-
Added detection for HRSword, which threat actors use for defense evasion. (T1562)
-
Multiple minor FP fixes and performance improvements.
-
Added detection for Bugsleep backdoor attributed to Iranian MuddyWater threat actor.
For a deeper dive into our MITRE ATT&CK Analyzer visit the changelog in the Binalyze Knowledge Base.
Fixes
The following bug fixes have been applied:
-
The acquisition reports icon was not always displayed in the AIR Console UI.
-
Exporting Flags resulted in errors in some instances.
-
Searching in the Investigation Hub was not always displaying the resultant hits.
-
Scheduled tasks in some cases launched before the correct start date/time.
25/09/2024
Hotfix
This hotfix addresses the following issues:
-
FSEvents Collection: The macOS Artifact Collection - FSEvents was not providing complete event data in the Investigation Hub. We have improved collection and removed the 3-day limit, ensuring all events are now captured.
-
Incorrect Asset Status: Assets were incorrectly marked as ‘Offline’ when they were actually ‘Online’. The fix ensures real-time and accurate status updates.
-
Report Viewing Issue: Users were unable to properly view reports in the Investigation Hub. The issue has been resolved, ensuring full access to reports.
-
Event ID Description Error: In the Investigation Hub, the description for every Event ID was incorrectly showing as "Windows is starting up". This issue has been resolved, and the correct descriptions are now displayed.
Recommendation: Apply the latest update to benefit from these fixes.
25/09/2024
23/09/2024
Version 4.23
Enhancements
New Improved Windows Event Log Collections
AIR v4.23 introduces a flexible and customizable event log collection feature, enabling users to collect event records in a fully configurable way by specifying channels, event IDs, and collection parameters.
Users can now:
-
Define specific channels for event log collection.
-
Select specific event IDs or add custom event IDs.
-
Set parameters such as:
-
Number of records to collect.
-
Date ranges for event log collection.
-
How It Works:
An “Event Log Records” configuration tab has been added to the “New Acquisition Profile” wizard in AIR. Users can enable this feature via the toggle switch and:
-
Select predefined event IDs from a list of over 200 of the most commonly used DFIR event IDs, or
-
Manually input custom channel IDs and event IDs of their choice using the “Add New Event Type” option.
Once configured, the new Acquisition Profile with Event Log Records settings can be saved to the AIR Acquisition Profiles library for future use. When running an Acquisition Profile that includes Event Log Records, users can select the profile and choose from two additional task options:
-
“Collect last N records”: The system will collect the specified number (N) of the most recent records for each event ID selected.
-
“Collect records between start and end dates”: This allows users to capture logs within a specific time range. (Note: This option is not available for scheduled acquisitions.)
These enhancements empower users to gather only the most relevant event logs for their investigations, significantly reducing the manual effort involved and ensuring critical events are not overlooked.
Fine-tuned and enhanced AIR’s Sigma engine
Significant backend improvements have successfully reduced unwanted noise and false positive findings by approximately 40%. Our efforts continue, with future releases aimed at reducing unwanted findings by 70-80%, enabling analysts to focus more quickly and efficiently on the most critical events.
Scan Local Drives Only Feature for triage tasks
The "Scan Local Drives Only" feature improves triage efficiency by focusing scans on local drives, excluding data from external or network drives.
-
Available for all AIR-supported operating systems.
-
Disabled by default but can be enabled as an organizational policy.
-
Also configurable by selecting the custom options during individual triage task creation.
This feature ensures faster, more focused scans by reducing unnecessary data collection.
Keyword-List Files can be added to DRONE searches
This release introduces the ability to upload keyword lists for the DRONE search capability, allowing users to efficiently search through data within their collections.
-
There is no character limit for keyword lists; the file size limit is 1 MB.
-
Each keyword must be on a new line.
-
Keyword searches operate only on data within the Case.db, not within CSV files.
-
Keyword search is extended to event log data, which is collected by the following Sigma analyzers:
-
Windows: Event Record Analyzer
-
Linux: Syslog Analyzer
-
macOS: Audit Event Analyzer
-
This feature enhances the search capabilities within the DRONE module, offering more flexibility and precision.
Investigation Hub Real-Time Disk Usage Visibility
This feature provides real-time visibility into disk space usage, allowing investigators to easily track storage utilization for both Cases and individual Tasking Assignments on the AIR database server (not assets or evidence repositories):
-
On the AIR Cases page, a new column shows the total space occupied by collections across all assets in a case.
-
In the Task Details window, the space occupied by each specific task assignment is now displayed.
These enhancements help investigators manage storage efficiently and prevent overloading environments, ensuring optimal performance.
Azure Blob supports image files for use in AIR’s File Explorer
Many customers store their evidence collections and forensic image files in Azure Blob Storage but until now AIR File Explorer could not access these image files to present (mount) them for investigation in the AIR console.
VHD and VHDX disk image support in AIR File Explorer
Investigators can now use the AIR File Explorer feature to create assets from VHD and VHDX disk images. You can then browse through files and folders within VHD and VHDX files.
This complements the functionality we already have for RAW, E01 Ex01, and VMDK disk image files. Please read more in our File Explorer FAQ’s.
Fixes
-
No notable issues, aside from those related to overall speed and performance.
21/08/2024
Version 4.21
Enhancements
We have expanded the evidence-collection capabilities in Binalyze AIR by adding several new browser-related items for Linux, macOS, and Windows:
For Linux, we now collect:
-
Browser Bookmarks (Chromium, Edge, Opera, Vivaldi, Brave)
-
Browser User Profiles (Chromium, Edge, Opera, Vivaldi, Brave)
-
Browser Local Storage (Chromium, Edge, Opera, Vivaldi, Brave)
-
Dump Browser Indexed DB (Chromium, Edge, Opera, Vivaldi, Brave)
-
Browser Web Storage (Chromium, Edge, Opera, Vivaldi, Brave)
For macOS, the following items have been added:
-
Browser Bookmarks (Edge, Opera, Vivaldi, Arc, Brave, QQ)
-
Browser User Profiles (Edge, Opera, Vivaldi, Arc, Brave, QQ)
-
Browser Local Storage (Edge, Opera, Vivaldi, Arc, Brave, QQ)
-
Dump Browser Indexed DB (Edge, Opera, Vivaldi, Arc, Brave, QQ)
-
Browser Web Storage (Edge, Opera, Vivaldi, Arc, Brave, QQ)
For Windows, we now collect:
-
Browser Bookmarks (Edge, Opera, Vivaldi, Brave, QQ)
-
Browser User Profiles (Edge, Opera, Vivaldi, Brave, QQ)
-
Browser Local Storage (Edge, Opera, Vivaldi, Brave, QQ)
-
Dump Browser Indexed DB (Edge, Opera, Vivaldi, Brave, QQ)
-
Browser Web Storage (Edge, Opera, Vivaldi, Brave, QQ)
We have also further enhanced evidence collection capability by adding a new artifact group for Windows focused on Docker.
The new "Docker" group includes the following items for collection:
-
Docker Changes
-
Docker Containers
-
Docker Image History
-
Docker Images
-
Docker Info
-
Docker Networks
-
Docker Processes
-
Docker Volumes
This addition ensures that Docker-related artifacts can now be collected and analyzed from Windows systems, further extending the capabilities of Binalyze AIR for environments leveraging containerization.
For a full list of the evidence and artifacts supported by AIR please visit our Knowledge Base.
Security
2FA for LDAP users from account settings
-
You can enable 2FA for LDAP users even if 2FA is enforced for all users, and now you can configure 2FA for LDAP users directly from account settings.
Fixes
-
Fixed: Repeat Mechanism in Schedule Task for Case Selection
-
A fix has been applied for the issue that arose when the user selected 'Case' after configuring the ‘repeat’ option in the Schedule Task settings, the repeat mechanism did not function as expected.
-
-
Fixed: 'Select All' in Case Includes Only Case Assets
-
A fix has been applied for the issue that arose when selecting all assets from a case as it included all assets from the organization rather than only those within the case when 'select all records' was chosen. (Credit: Mustafa D)
-
-
Fixed: Potential PostgreSQL CVE-2024-7348 Vulnerability in AIR
-
We have resolved the PostgreSQL security vulnerability detailed in CVE-2024-7348 within Binalyze AIR. This vulnerability could potentially allow unauthorized access or data leakage due to improper handling of database permissions in PostgreSQL. Our update addresses this issue, ensuring that our platform remains secure and your data is fully protected. This fix reflects our commitment to maintaining the highest security standards in AIR.
-
21/08/2024
07/08/2024
Version 4.19
Features
VMDK support in AIR File Explorer
-
Investigators can now use the AIR File Explorer feature to create assets from VMDK disk images. You can then browse through files and folders within VMDK files. This functionality is available regardless of whether the images are segmented or contained in a single file.
-
This complements the functionality we already have for RAW, E01 and Ex01 image files. Please read more in our File Explorer FAQ’s.
AWS S3 bucket support in AIR File Explorer
-
Many customers store their evidence collections and forensic image files in AWS S3 and until now AIR File Explorer could not access these image files to present (mount) them for investigation in the AIR console.
-
This complements the functionality we already have for RAW, E01 and Ex01 image files. Please read more in our File Explorer FAQ’s.
Enhancements
Investigation Hub
The Investigation Hub in AIR continues to evolve at pace, offering enhanced workflows with comprehensive insights and collaborative tools. New features include a detachable evidence details window that can be resized and repositioned for improved clarity. The addition of fullscreen evidence tables and sticky column headings ensures efficient case management and significantly boosts productivity across all investigative activities:
-
Detachable Evidence Details Window
-
Allows users to detach the evidence details window into a standalone window, providing flexibility to place it anywhere on the screen(s) for improved clarity.
-
This window can be reshaped and resized to the user's preference, maintaining its form even when displaying new evidence items.
-
Clicking on a new row in the table will update the detached details view to match the newly selected item.
-
-
Fullscreen window for evidence tables
-
Users can now ‘go full-screen’ with their evidence tables, which is especially valuable for large, multi-column data sets.
-
-
Sticky column headings are saved in the Investigation Hub
-
Both column selection and position will remain saved/static within your browser for all user-based AIR sessions, even if you log out, unless you choose to clear your browser cookies.
-
New AIR audit log retention policy
-
AIR v4.19 introduces a new AIR audit log retention policy aimed at optimizing platform performance and data management. Users are encouraged to back up their audit logs regularly to ensure no loss of data.
-
With AIR v.4.19 and later, all AIR audit logs are saved to PostgreSQL and retained for 3 months after which they are deleted.
-
Please see this KB page to learn more.
Frank.AI Copilot configuration (Credit: James W)
-
Users can now choose to switch Frank.AI on or off from the AIR ‘Settings > Features’ page.
-
Frank.AI is active by default. You can learn more about it and our future development plans here in the Knowledge Base.
Binalyze MITRE ATT&CK Analyzer has been updated to version 6.3.0 (07/08/24)
Yara enhancements include:
-
Added detection for IOCs linked to North Korean Lazarus/Andrariel groups (G0032, G0138).
-
Added detection for APT group StormBamboo/Evasive Panda.
-
Improved detection of shellcode loaders.
-
Added detection for the SharpSploit post-exploitation tool.
-
Added detection for the open-source Lilith RAT (T1219).
-
Improved detection of Metasploit implants for Linux.
-
Added detection for Java-based STRRAT and related IOCs.
-
Other minor fixes and improvements.
-
For details please see the changelog in the Binalyze KB.
In addition to the updates listed above, we have fixed several minor issues and made improvements to enhance performance and user experience.
25/07/2024
Hotfix v4.17.9
This hotfix improves database migration stability by addressing data inconsistencies in investigation activities (comments, notes, etc.). This version aims to minimize potential migration issues.
25/07/2024
11/07/2024
Version 4.17
Features
EWF2 (Expert Witness Format 2) support
-
AIR now supports the creation of forensic disk and volume images in the EWF2 format. These images can be directly uploaded to your AIR Evidence Repositories.
-
EWF2 is commonly used in digital forensics to store and compress digital evidence and the format supports the inclusion of metadata.
-
Investigators can now use the AIR File Explorer feature to create assets from EWF disk images. You can then browse through files and folders within both E01 and Ex01 formats. This functionality is available regardless of whether the images are segmented or contained in a single file.
-
This compliments the functionality we alread have for RAW image files. Please read more in our File Explorer FAQ’s.
New Browser Data Collectors:
-
Thumbnails: Now includes support for Vivaldi, Brave, Chromium, Opera, Edge, QQ, and Arc.
-
Form History: Collect form history data from Vivaldi, Brave, Chromium, Opera, Edge, QQ, and Arc.
-
Cookies: Enhanced cookie collection capabilities for Vivaldi, Brave, Chromium, Opera, Edge, QQ, and Arc.
-
Favicons: Collect favicons from Vivaldi, Brave, Chromium, Opera, Edge, QQ, and Arc.
New ESXi Collectors:
-
Cross Active Connections: Monitor and collect data on active connections.
-
Datastores: Gather information from ESXi datastores.
-
Hardware Clock: Access and collect hardware clock settings.
-
Networks: Collect detailed network configuration and activity data.
-
VMware Version: Track and collect information on the VMware software version.
Enhancements
Investigation Hub
The Investigation Hub in AIR is the central point for all your investigations, enhancing workflows with comprehensive insights and collaborative tools. It includes advanced search options and a new dynamic filter, making it essential for efficient case management and boosting productivity across investigative activities.
-
New Evidence Category for ‘Other Evidence’, these items being Findings without an Evidence Category in AIR
-
This enhances the clarity of the Findings displayed to users. Previously, some findings identified by the DRONE did not correspond to any of the available evidence categories.
-
With this change, all findings without a specific category will be grouped under 'Other Evidence'. This ensures every finding is allocated an evidence record within a category, allowing the total count of findings on the Investigation dashboard to accurately match the number shown in the evidence list.
-
-
New filter option for flagged items
-
Users can now use the advanced filter to include or exclude flagged items in the Investigation Hub table views, enhancing the ability to focus on prioritized or highlighted evidence.
-
-
Windows FAT file system support
-
AIR now supports the FAT filesystem, expanding our compatibility for logical imaging with ext4, ext3, and NTFS file systems.
-
-
Nested Asset Tagging
-
Nested Tagging has been added for your Assets, providing tag grouping for the organization of assets. This new feature allows for a more structured and detailed structuring of assets within AIR, making navigating the more complex network structures easier.
-
To create a nested tag, go to the Asset Info page and use a colon (:) to separate each level of the hierarchy. For deeper nesting, simply add additional colons between each subsequent tag level:
-
Fixes
-
Cross-Site Scripting (XSS) Vulnerability Patched
-
We have addressed and resolved a critical vulnerability that allowed attackers to potentially take over accounts through Cross-Site Scripting (XSS) in compromised hosts. This fix significantly strengthens the security of our system against unauthorized access.
-
24/06/2024
Hotfix
Today we released a hotfix that provides a Responder update to solve tactical incompatibility issues with other security products.
24/06/2024
11/06/2024
Hotfix
Issue Addressed:
In the AIR Investigation Hub, a materialized view in the PostgreSQL database related to exclusion and finding relations was identified as the root cause of performance degradation. This view was being refreshed every time a field within it was updated. Due to the resource-intensive nature of this refresh transaction, frequent updates often caused database-level deadlocks. These deadlocks, in turn, slowed down the database and degraded application performance.
Impact:
The issue does not necessarily affect all customers uniformly. The likelihood of encountering performance problems depended on the number of assets being managed, the volume of investigations being actively conducted, and the frequency of asset name changes. Consequently, while some customers have experienced performance issues, others did not.
Resolution:
We have today implemented a hotfix to optimize the refresh process for the materialized view, reducing the likelihood of deadlocks and improving overall database and application performance.
Recommendations:
Customers experiencing performance issues are advised to apply this hotfix to benefit from the optimizations. For further assistance, please contact our team via; support@binalyze.com
04/06/2024
Version 4.15
Features
Investigation Hub - New Features
The Investigation Hub in AIR is the central point for initiating and concluding all your investigations. As the core of AIR, it enhances your investigative process by integrating comprehensive insights and prioritized data with robust collaboration features. Equipped with advanced navigation features like sophisticated search options and dynamic filters, the Investigation Hub is indispensable for smooth and efficient case management, boosting productivity and connecting all investigative activities seamlessly.
New Activity Feed
-
The Activity Feed enhances team collaboration and transparency by logging actions taken by investigators. This includes creating; exclusions, findings, flags, comments, and notes. Each entry includes user identification and timestamp information to ensure a comprehensive audit trail.
-
All of the activities are labeled and linked to the individual activity simply by clicking on it. In the example below we can see how Comment Added, Note Added, Flag Added, and Exclusion Rule Created have all been tracked as activities
Add Comment to evidence
-
Comments enhance communication by allowing analysts to directly comment on findings or/and tag relevant colleagues. This ensures that all discussions are captured and documented within the activity feed, promoting effective collaboration and transparent activity tracking.
-
Right-click on an item and select ‘Comment’ to attach your comment to that item.
Event Logs View and Filtering Improvements
-
To manage the extensive data from Event Logs, we've introduced a Column Chooser feature. This allows users to customize their view by selecting specific data fields from the Details view that they want to display in columns. This makes it easier to sort, filter, and analyze the desired relevant log data.
Search Options for selected text
-
Users can highlight text within tables and instantly search for it within the same table, across the entire Investigation Hub, or externally on Google or VirusTotal. This feature streamlines the research process and eliminates the need to toggle between different platforms.
Away from the Investigation Hub other new features include:
Tagging added to Triage Rules
-
Triage rules in the AIR console can now be associated with Tags, which help in organizing rules and filtering when required. This enhancement aids in managing the rules more efficiently and allows for streamlined searches and better organization within the console.
-
When creating a Triage Rule the UI allows the user to filter existing rules by their associated Tags.
-
The Triage Rule Library now includes Preset Filters in the secondary menu, allowing users to organize rules hierarchically.
ESXi parser added
-
The ESXi parser has been added to the AIR platform, allowing for the import of tasks from off-network ESXi collectors and their presentation in the Investigation Hub.
-
Learn more about our ESXi collector here.
Enhancements
Binalyze MITRE ATT&CK Analyzer has been updated to version 5.3.1 (31/05/24)
-
For details please see the changelog in the Binalyze KB.
Expose more action buttons on the Asset Info page
-
Additional Action Buttons have been introduced to the Asset page to improve usability and immediate access to the most commonly selected actions.
Improvements to the Details view
-
Each item's title is displayed in light grey text, making the more critical information in darker text stand out for easier reading and quick reference.
-
The "Show or Hide Empty Fields" view option helps to declutter the display by allowing users to hide fields that contain no data, thus reducing visual noise and focusing attention on fields with relevant information.
Advanced Filter improvements
-
The advanced filter save feature boosts efficiency by enabling users to save and share custom filters within an AIR organization. This functionality streamlines data analysis, promotes consistency, and enhances collaboration throughout the investigative process.
-
The Advanced Filter window remains visible as you build the filter and you can reposition it.
-
Each Advanced Filter is specific to the table it is built in eg; an advanced filter you build in Findings will not be available to you in the Browser Artifact table.
-
Filters can be saved and then later selected from the drop-down list.
-
Add items to Advanced Filters directly from the Details window using the filter icon.
Fixes
-
Timeline date/time picker bug is fixed
04/06/2024
09/05/2024
Version 4.13
Features
Investigation Hub - New Features
The Investigation Hub has been updated with a new look and feel, now aligned with the rest of AIR to provide a consistent navigation experience. It also features enhanced and new features, as well as improved overall performance.
-
New Dashboard & Widgets
-
Global search with tabbed search for AIR or the Investigation Hub
-
Export user-generated flags to .csv
-
Clickable Finding Types for new re-mapped 4 severity levels:
-
High
-
Medium
-
Low
-
Matched
-
-
New user-generated Flags widget
-
-
New Secondary Menu with the ability to:
-
Search for evidence in the comprehensive categories listings
-
Hide empty pages, and categories with no return
-
Show only evidence with Findings
-
Show only the evidence with flags
-
-
Global Filters for:
-
Assets including the ability to filter by individual taskings
-
Finding Types; High, Medium, Low, and Matched
-
Flags
-
Dates & Times via a ‘picker’ and some presets
-
Created By
-
-
New table layout and functionality:
-
Introducing a Flags column
-
Column header searching and filtering
-
Column header date & time ‘picker’
-
Dockable Details pane, horizontal, vertical, or minimized
-
Flags
-
It is now possible to create custom flags by right-clicking on an evidence item, selecting ‘Add/Remove Flag’, and then creating a name, description, and color for your Flag.
-
Select multiple items to perform Bulk Flagging operation.
-
Flags are saved at the Organization level in Libraries
User-generated Findings
-
AIR 4.13 has added user-generated Findings to complement AIR’s DRONE Findings
-
Right-clicking on an evidence item will allow users to allocate a Finding to the item
-
Exclusions
-
It is now possible to select any evidence items from your Findings for exclusion.
-
Three options:
-
Right-click on a Finding and select ‘Exclude’
-
Select the ellipsis at the end of the row
-
Bulk Actions will allow you to exclude more than one item at a time
-
-
The Exclusion Rule allows you to exclude by:
-
Path or Finding
-
For the Case or whole Organization
-
For selected assets or all assets in the case
-
Notes
-
Notes can now be added to every evidence item - the item does not have to be bookmarked to have a note attached.
-
The new table view now has a Notes column for all items
-
Notes can be included in your reports
Improved Reports
-
The new flagging capability in the Investigation Hub improves reporting by enabling users to include specific Findings and further filter by individual Flags for a more targeted output:
-
This enhanced granularity extends to the next step of report generation, where users can now add and filter non-finding evidence items by Flags for even more precise reporting:
-
Reports can be managed, edited, generated, exported, and deleted from the Reports tab in the Secondary Menu.
-
For more information about the Investigation Hub please visit our Knowledge Base:
Away from the Investigation Hub other new features include:
-
New Windows, macOS, and Linux evidence types:
-
Edge Sessions
-
Opera Sessions
-
Brave Sessions
-
Vivaldi Sessions
-
-
New Windows evidence types:
-
Powershell ConsoleHost History
-
QQ Sessions
-
-
New macOS evidence type:
-
QQ Sessions
-
Arc Sessions
-
-
New Linux evidence type:
-
Chromium
-
-
A full list of the 500+ items now supported in AIR is available in the Knowledge Base.
-
osquery can be added to an Acquisition Profile
-
A new "osquery" tab has been added to the acquisition profiles for each supported OS, enabling users to enhance evidence collection by incorporating osquery capabilities into their evidential acquisitions.
-
NB: This unique feature allows users to send data collected via osquery directly to a timeline, an option not available in previous osquery implementations for triage.
-
-
AIR Isolation ‘allow’ lists
-
Users can now specify a list of pre-approved processes, IP addresses, and ports that remain active on an isolated asset. This ensures that essential services and connections, such as EDR, continue uninterrupted, supporting ongoing SOC processes.
-
Enhancements
-
Binalyze MITRE ATT&CK Analyzer has been updated to version 5.0.1
-
For details please see the changelog in the Binalyze KB.
-
-
User Privileges for Task Scheduling:
-
AIR administrators can now restrict users from scheduling tasks or editing existing ones:
-
Schedule Task: Enables users to "Schedule for later." Without this privilege, this option is disabled, and a tooltip explains the restriction.
-
Update Scheduled Task: Allows users to edit scheduled tasks. If this privilege is not granted, the "Edit" button is disabled with an explanatory tooltip.
-
-
-
Scheduling options for responder updates
-
New scheduling options for responder updates to streamline the process, ensuring that updates do not disrupt ongoing investigations.
-
Scheduled Manual Updates: Users can now schedule updates for a specific time for an individual asset or a group of assets. Setting a new update time for an asset will override any previously scheduled time for that asset.
-
Scheduled Auto Updates: Users can establish a recurring schedule to automatically check for and apply updates within a designated timeframe.
-
-
-
File Explorer - Calculate Hash for disk images
-
When a disk image is added as an asset to AIR, users can now calculate the hash value of that image file either through the Asset Actions button or from the Disk Image Details window.
-
MD5, SHA1 and SHA256 are all calculated simultaneously.
-
This hash function can be carried out at any time.
-
-
File Explorer - Recursive Search
-
Recursive searching is now possible in the AIR File Explorer via the Global Search box where the File Explorer tab will display any hits found in the File Explorer.
-
Fixes
-
Timeline date filtering issue has been fixed (Credit: Josh T)
-
Column widths changing automatically with no user interaction has been fixed. (Credit: Guo Y)
-
Off-line users Windows Registry data will now be parsed (Credit: Mark CD)
02/04/2024
Version 4.11
Features
-
Introducing Frank.AI, your investigation copilot
-
Frank is an AI Assistant designed to enhance forensic investigations within the AIR console. Frank.AI offers instant forensic assistance across all console pages, for example, providing insights, without leaving AIR, on subjects such as YARA, Sigma, and Osquery rule writing.
-
In this preview version, Frank leverages the ChatGPT API without additional fine-tuning, setting the stage for future enhancements. Future updates aim to expand Frank's capabilities through Retrieval Augmented Generation (RAG) for accessing broader data sources and deeper integration with the AIR ecosystem, including direct data retrieval from the AIR database and collaborative analysis with the AIR's AI module for advanced insights, such as anomaly detection and behavioral correlations.
-
You can reposition, resize, and minimize it just like any standard window, ensuring it fits seamlessly into your workflow without obstructing your view.
-
There are no additional domain requirements as Frank.AI is hosted on one.binalyze.com.
-
Stay tuned for evolving features and improvements based on user feedback.
-
-
New evidence types:
Windows
-
Parse LNK Files
-
Collect LNK Files
Linux
-
Systemctl Services
Browser evidence types across Windows, Linux and macOS
-
Chrome Sessions
-
Chrome Login Data
-
Chrome Local Storage
-
Chrome IndexedDB
-
Chrome Web Storage
-
Chrome Form History
-
Chrome Thumbnails
-
Chrome Favicons
-
Default Browser
-
Firefox Cookies
Credit: Ashok K
-
A full list of the 584 items now supported in AIR is available in the Knowledge Base.
Enhancements
-
Binalyze MITRE ATT&CK Analyzer has been updated to version 4.3.1
-
For details please see the changelog in the Binalyze KB.
-
-
Disk imaging errors reported in metadata.yml
-
AIR’s disk or volume imaging feature produces a file that captures the metadata related to the imaging process. This now includes a log of any errors encountered, which are documented within the metadata.yml file for comprehensive tracking and analysis. (Credit: Charlotte H)
-
Please see this KB article for a full explanation.
-
-
Scheduling Based on Asset Timezone
-
AIR now enables users to schedule tasks according to the asset's local time zone. This ensures that tasks are executed at the specified time relative to each asset's geographical location, allowing for synchronized operations across different time zones. For example, when choosing this option, instructing the system to perform a task at 01:00 will result in the task being carried out at 01:00 in the local time of each asset, regardless of their global positions. (Credit: Ramesh P)
-
Please see this KB article for more information.
-
-
Auto Asset Tagging Rules: New wizard and Organizational Saving
-
The new Auto Asset Tagging (AAT) wizard allows rules to be saved specifically for individual organizations or universally across all organizations. This enhancement supports users in creating and applying incident-specific AATs selectively, avoiding unnecessary use or exposure of a rule outside the intended organizational context. (Credit: Caleb T)
-
Please read this Auto Asset Tagging KB page for more information.
-
-
AIR version information is again displayed in the main menu
-
The AIR console version number has returned to the main menu to stop users from having to locate it on the settings page.
-
Fixes
-
A timestamp issue with the Event log content has been fixed. (Credit: Jon F, Grant O and Ben H)
-
Some incorrect "Match Counts" under the "Case Triages" Page have been resolved.
-
In previous versions, AIR displayed the "KeyLastWriteTime" in the evidential Amcache CSV files in local time instead of UTC. This has now been corrected to show times in UTC, ensuring consistency and accuracy. (Credit: Guo Y)
-
Tornado, crucial for AIR's File Explorer integration, retries registration until successful. A bug affecting success confirmation was fixed, enhancing reliability. (Credit: Nuno P)
02/04/2024
07/03/2024
Version 4.9
Features
-
New Task Scheduling capability integrated into the AIR tasking wizard.
-
Investigators can now use the tasking wizard to schedule the following activities:
-
Evidence collections.
-
Triage/Threat Hunting. (Credit: Turgut Ö)
-
Disk and Volume Imaging.
-
Auto Asset Tagging.
-
-
Scheduled tasks can be assigned to a Case.
-
The timezone for task execution can be adjusted.
-
The recurrence rate can be set to Daily, Weekly, or Monthly.
-
The sequence can be stopped at a particular date and time or after a defined number of occurrences.
-
-
New Windows evidence type
-
AIR now parses the Window $USN Journal and saves this file to the evidence repository as a .csv file for easy analysis (Credit: David C)
-
Enhancements
-
ESXi collections
-
We have extended the list of what we collect from ESXi from 10 to 100 items. For the full list please visit the Binalyze KB (Credit: Guo Y)
-
-
MacOS Agent - Full Disk Access requests
-
When installing an AIR responder on a T2 or later Mac, Full Disk Access is required for it to have the necessary permissions for all AIR collection types. AIR’s responder will now display a message to advise the installer to:
-
Open System Settings -> Privacy & Security -> Full Disk Access to grant permission to ”air”.
-
The user will need to toggle the switch 'on' to enable Full Disk Access for the AIR responder. (Credit: Caleb T)
-
-
-
Auto Asset Tagging Rules added to Task Details
-
Users can now see in the Task Details window, the Auto Asset Tag(AAT) rules which were checked during individual AAT task assignments.
-
Binalyze MITRE ATT&CK Analyzer has seen the following updates since the last release of AIR: 4.1.0, 4.2.0, 4.2.1, 4.2.2 and 4.2.3.
For details please see the changelog in the Binalyze KB.
Fixes
-
Bulk Action Bar re-sized and re-positioned
-
The new size and location of the Bulk Action Bar means that it no longer interferes with other information displayed in the UI. (Credit: David C)
-
20/02/2024
Version 4.8.1
Hot Fix
-
Attention to users of AIR 4.8.0: Some users may experience difficulty logging into AIRConsole. This issue affects only users assigned to specific organizations (but not those who select “All” organizations).
Please see the example below for reference.
In version 4.8.1, we have addressed and resolved this issue. We recommend all customers currently using AIR 4.8.0 to upgrade to AIR 4.8.1 at your earliest convenience
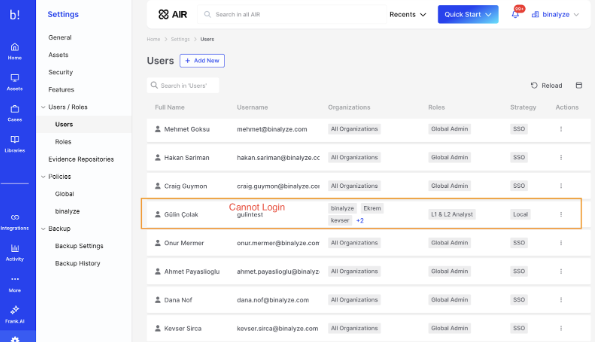
20/02/2024
14/02/2024
Version 4.8
In AIR version 4.7 and above, we've added a new Docker container specifically for enabling the new File Explorer feature in AIR. If you're not interested in using File Explorer, you can proceed with the upgrade as usual. However, if you do wish to utilize the File Explorer and haven't received assistance with migration yet, please reach out to our support team for guidance on updating to either version 4.7+. Kindly note that contacting our support team is only necessary if you intend to activate the File Explorer feature.
Enhancements
-
Isolate multiple assets simultaneously
-
Users now have the capability to select multiple assets simultaneously and execute bulk actions to isolate any desired number of assets concurrently. (Credit: Samer H)
-
-
Task renaming
-
Tasks can now be easily renamed via the edit pencil icon located within the Task Details Information tab, streamlining the renaming process for enhanced efficiency and convenience.
-
-
Columns Headings order & stickiness
-
We've enhanced the Investigation Hub tables, enabling users to choose and easily rearrange columns by dragging and dropping them into their preferred order. This selected layout will remain 'sticky' for each user, providing a personalized experience.(Credit: Allesando G)
-
-
Auto Asset Tagging Rules added to Task Details
-
The Auto Asset Tags used in a Tasking Assignment are now displayed under the Information tab in the Task Details window.
-
-
Enhanced Responder Uninstallation
-
By default, the responder uninstallation process now includes a purge/clean-up operation where certain responder application files that were not removed in earlier versions of AIR will now be purged during the process. It's important to note that evidence saved on the local asset or any external evidence repositories will remain unaffected.
-
Fixes
-
Agent Update Task Errors
-
A recent Windows update affected the ability of some AIR agents ability to auto-update. Fixed in AIR v4.8 (Credit: Blake B)
-
-
Asset labeling/editing issue fixed
-
Typing a new or editing an existing asset label was problematic as the UI was not allowing time to complete typing in some instances. Fixed in AIR v4.8 (Credit: Zainal B N)
-
05/02/2024
Version 4.7
Features
In AIR version 4.7 and above, we've added a new Docker container specifically for enabling the new File Explorer feature in AIR. If you're not interested in using File Explorer, you can proceed with the upgrade as usual. However, if you do wish to utilize the File Explorer and haven't received assistance with migration yet, please reach out to our support team for guidance on updating to either version 4.7+. Kindly note that contacting our support team is only necessary if you intend to activate the File Explorer feature.
Investigation
-
Introducing AIR's new File Explorer.
AIR can now be used to explore the file systems of Windows, macOS, and Linux systems where full disk or volume images have been acquired in the RAW format.
The forensic image can be added to AIR as a new Asset in a three-step process:
-
1. On the Assets page, click on the ‘Add New’ button and then select Disk Image:
-
2. Select your connected repository and then the raw disk image you wish to explore:
-
3. Select ‘Create Asset’:
The image must be supplied to AIR from an SMB or SFTP shared location, where it needs to be saved as a single contiguous file. Segmented files are not currently supported.
The next step is to select File Explore from the secondary menu:
Now you can browse the asset’s directory structure which is now expanded in the secondary menu (highlighted below) and then go on to select individual files for closer inspection:
A file can be selected with a right-click to download it locally or calculate its hash values.
Advanced filters can be applied to filter the files displayed.
This is just the beginning of our File Explorer project - many more features are planned and your feedback is most welcome.
-
Advanced Filter capability for all evidence category tables
We have added and standardized our advanced filter functionality across all Investigation Hub evidence category tables to:
-
Ensure consistency across AIR's data analysis capabilities.
-
Empower users with flexible advanced query options.
-
Enhance overall data analysis efficiency.
The example above demonstrates the versatility of crafting filters that cater to both simple and intricate requirements. These filters offer support for compound logic by using AND/OR Boolean operators, applicable to any of the available columns. This empowers investigators with robust and flexible filtering capabilities.
-
New collection of remote tool artifacts:
macOS
-
Splashtop Mac Logs
Windows
-
Xeox Logs
-
ZohoAssist Logs
-
Supremo Remote Desktop Logs
-
TightVNC Logs
-
AmmyAdmin Logs
-
GoTo Logs
-
Kaseya Logs
-
Level Logs
-
Remote Utilities Logs
-
RealVNC Logs
-
Splashtop Windows Logs
-
UltraVNC Logs
Enhancements
Investigation
-
Improved visibility to DRONE’s verdicts.
-
V4.7 provides valuable transparency by reducing noisy findings and improving visibility into DRONE’s detection logic helping streamline investigations and boost confidence in DRONE's methodology. (Credit: Garett C)
-
The example below shows how, in the details tab, DRONE will now highlight each finding with:
-
Its description.
-
A reference to learn more about the findings.
-
The actual string that was detected.
-
Investigation Hub - Consolidated View of Bookmarked Items.
-
With this new feature, AIR users can easily access their bookmarked items, bypassing the need to navigate through multiple sections. This simplifies the workflow and saves time. (Credit: Grant O)
-
The ‘bookmarks-only’ view is accessed via the button in the Investigation Hub page header. Findings and evidence categories with bookmarks can be viewed via drop-down arrows.
-
Additionally, the note-taking capability enables users to capture extra context and insights, contributing to a more comprehensive understanding of their bookmarked content. Notes can be added via the edit pencil in the Bookmark Notes column.
Functionality
-
Windows direct collection
-
With the introduction of Windows support, which complements our existing macOS and Linux capabilities, it is now feasible to transmit evidential collections from all three operating systems directly to external evidence repositories, thereby efficiently minimizing the utilization of local disk space.
-
New API functionality
-
Acquisition profiles can be created directly with the API with ‘Get Acquisition Profiles’.
-
Asset Tags can be created or removed with the API (Credit: Blake B)
-
AIR API documentation is found at: docs.binalyze.com
MITRE ATT&CK Analyzer changelog
4.0.1
Yara
-
Added detection for C# and dictionary-based webshells.
-
Enhanced detection of JSP webshells.
-
Enhanced detection of directory traversal and XSS injection indicators found in server logs.
-
Enhanced detection of ProxyShell and ProxyNotShell vulnerabilities.
-
Added detection of various Linux exploits.
-
An updated list of vulnerable and malicious drivers from LOL Drivers project.
-
Added detection for binaries using potentially compromised AnyDesk certificate.
-
Other minor fixes.
Dynamo
-
Minor FP fixes.
(Full changelog is here: AIR MITRE ATT&CK Changelog)
Fixes
-
We are pleased to announce a critical fix regarding some of the NTFS categories of evidence collections, which were causing collection tasks to sometimes become unresponsive. The root of the issue was traced back to our backend library, which encompasses a range of NTFS-related evidence types, including:
-
Page File
-
Hibernation File
-
Swap File
-
Hosts
-
Recent File Cache
-
We have taken steps to address and rectify this issue, and users should no longer experience any issues with these collections. (Credit: Guo Y)
-
Fix applied for an issue regarding the console backup process via the optimization of our backup compression logic. (Credit: Ben H)
05/02/2024
09/01/2024
Version 4.5
Features
Investigation
-
Preview our new Customizable Reporting feature in the Investigation Hub.
-
This initial version is just the beginning, with many more enhancements in functionality and capacity planned for future updates.
-
Users can, at speed, automatically generate an insightful and shareable comprehensive Compromise Assessment PDF report based on DRONE’s findings.
-
This report is fully customizable, enabling users to choose specific elements for inclusion in their bespoke reports:
-
The Verdicts or Scores as determined by DRONE
-
A Company logo
-
An Executive Summary
-
The Methodology Overview
-
The Data Source Statistics
-
An Asset Overview
-
-
Post-generation, the report remains editable via our built-in browser editor, allowing for the addition of analyst-led notes and supplemental details such as observations, recommendations, and conclusions.
-
-
New macOS Evidence Types:
-
FS Events - On macOS 10.17 and later, files with an extension '.fseventsd' (File System Events Daemon) are used to record many file system events, such as file creation, modification, and deletion. This log acts like a 'black box flight recorder' and can be extremely useful in reconstructing the timeline of activities on a Mac.
-
Browser Download data for:
-
Chrome
-
Edge
-
Firefox
-
Opera,
-
Safari
-
Vivaldi
-
Waterfox
-
Brave
-
Arc
-
-
-
New Windows Evidence Types:
-
Browser Download data for:
-
Chrome
-
Edge
-
Firefox
-
Opera
-
Brave
-
Vivaldi
-
-
-
New Linux Evidence Types:
-
Browser Download data for:
-
Chrome
-
Chromium
-
Edge
-
Firefox
-
Opera
-
Brave
-
Vivaldi
-
-
Enhancements
Investigation
-
AIR UI Improvements include:
-
Secondary menus now consistently display drop-down arrows or sub-menu indicators, providing a clear visual cue that additional options are available.
-
Enhanced discoverability by setting menus to expand automatically by default.
-
We have enhanced the Quick Start menu by adding "New Case" and "New Asset" options for streamlined access to these features.
-
-
New Flags for interACT download commands:
-
With these new flags, users can speed up workflows by having the following extra functionality for files they want to download using the ‘get’ command in interACT.
-
Compression: ‘-zip’
-
Password protection: ‘-zip-password’
-
File name change: ‘-name’
-
-
Functionality
-
Investigation Hub Improvements:
-
The import status of task data into the Investigation hub is now displayed. There are four states:
-
Pending task completion.
-
Importing to the case.
-
Import completed.
-
Failed (a ‘Retry’ option is also presented to the user)
-
-
Auto refresh on-demand button (Credit: Ben H)
-
This update introduces an on-demand refresh button, notified via a banner message in the Investigation Hub, when new evidence is available for the current case. This reduces distractions from auto-updates, allowing analysts to refresh the page at their convenience and stay focused during investigations.
-
-
Audit logs for Evidence Imports into the Investigation Hub
-
These new logs detail who accessed the Investigation Hub import feature, when, and what actions they took, enhancing accountability by linking activities to specific users.
-
Fixes
-
Asset names are now included for User Access Logs downloaded from Investigation Hub as CSVs (Credit: Ben H)
-
Asset names are now featured in User Access Logs (UALs) downloaded from the Investigation Hub as CSV files, providing analysts with clear visibility of the originating assets for these logs.
-
07/12/2023
Version 4.3
Features
Investigation
-
Enhanced Data Integration into the Investigation Hub:
-
Seamlessly import .csv files into the Investigation Hub using our data mapping service, accommodating all forms of structured .csv data.
-
Efficiently import and analyze .pst files, enabling the display of email data within the Investigation Hub for a more comprehensive examination.
-
-
2 New Windows Evidence Types:
-
Winrar History - This application history is valuable as it tracks file compression/extraction, revealing user actions, timelines, and data movement. (Credit: Ashok K)
-
Windows Error Reporting Files - WER files provide insights into system crashes and application failures, helping to identify potential security breaches or system vulnerabilities. Additionally, they are instrumental in malware detection and constructing accurate timelines for security incidents.
-
-
7 New IBM AIX Evidence Types:
-
MySQL Logs - These logs are critical for tracing database transactions, analyzing user activities, establishing timelines, and detecting unusual or malicious query patterns. They provide key insights into data modifications and user behavior.
-
SSH Server Logs - These logs are invaluable for tracking authentication attempts, identifying user access patterns, and detecting potential unauthorized or malicious activities.
-
DHCP Server Logs - provide crucial information on network device connections, including IP address assignments, timestamps, and MAC addresses, aiding in tracking device movements and identifying unauthorized network access.
-
System Logs - Records system activities, user actions, and error messages.
-
Auth Logs - These track authentication activities, such as login attempts and user privileges, providing insights into potential unauthorized access, user behavior, and security policy violations.
-
Boot Logs - Used to analyze system startup sequences, identifying unauthorized changes or failures during boot processes.
-
Mail Logs - Tracks email transactions, identifying senders and recipients, analyzing timestamps, and detecting anomalies or potential security breaches.
-
Enhancements
Investigation
-
Comparison report improvements
-
The Progress window now displays the status of the comparison, including a count for Added, Changed, or Deleted items. When an evidence item is selected, it filters the main viewing window to show the detailed comparison results for that specific item exclusively.
-
The comparison report now also makes it clear when no changes have been detected.
-
-
Exporting DRONE Findings
-
Users can export the DRONE findings table out of the Investigation Hub into a .csv file.
-
This will allow the use of DRONE findings in reports, SIEM, or other security tools where custom alerts can be developed based on the results of DRONE’s analysis.
-
-
AIR’s MITRE ATT&CK Analyzer version 3.1.0 includes the following:
✅ Every detection now links to an MITRE ATT&CK Technique instead of Tactic only.
Yara:
✅ Added coverage for various malware families mentioned in our latest reports.
✅ Enhanced detection of anomalies for various techniques such as masquerading, defense evasion, credentials access, suspicious PowerShell scripts, and more.
Dynamo:
✅ Enhanced detection of HTML Smuggling technique for more Chromium-based browsers.
✅ Enhanced detection of suspicious Firewall rules, Scheduled tasks, and Services.
Functionality
-
Ability to adjust timezones in Investigation Hub
-
By default, the Investigation Hub will use UTC as the timezone to display all timestamps.
-
With this release, Investigation Hub users can adjust timezones, improving analysis accuracy in investigations involving diverse geographic and timestamp data.
-
-
New Asset window for UI
-
Individual assets will now have a dedicated larger window to display more information, appear less cramped, and prepare for future developments.
-
Each Asset page now includes a secondary menu featuring preset filters, providing users with a count and instant access to all past tasking assignments associated with that asset.
-
In this new window, users can view and access all of the cases in which the current asset appears.
-
Tasks can be created from the Asset Action button or by clicking on the ‘+’ revealed when hovering on any of the task names listed in the secondary menu.
-
-
Adjustable Secondary Menu
-
The user can now manually adjust the secondary menu width in AIR, allowing it to expand up to half of the display window's width through a simple drag action.
-
Double-clicking the secondary menu border will return it to its default size.
-
-
New advanced filter to identify servers
-
Users can now filter assets based on whether or not any of their assets are servers. (Credit: Jon F)
-
-
Custom Message Banner available via API
-
Users can use all custom banner capabilities via API - the latest posted message, by UI or API, will prevail.
-
-
Removal of a default value from the acquisition profile selection field
-
When initiating a new Acquisition, the Acquisition Profile field will now be blank by default, requiring the user to actively choose a profile. The placeholder text in this field now reads, "Select/create an Acquisition Profile." (Credit: James S)
-
Fixes
-
Data grid issue with Organization Updates
-
Data grids now refresh correctly when Organizations are updated.
-
07/12/2023
02/11/2023
Version 4.1
Features
Investigation
-
6 new macOS Evidence Types:
-
SSH Known Hosts - Collects SSH Known Hosts used to store the SSH server key fingerprints of the servers that you have connected to in the past.
-
SSH Authorized Keys - Collects SSH Authorized Keys which grant user account access and are crucial for SSH key-based access.
-
SSH Configurations - Collects SSH Configurations which record remote IP addresses, different usernames, non-standard ports, and various used command-line options.
-
SSHD Configurations - Collects SSHD Configurations which indicates the locations of host key files and users' authorized_keys files.
-
Brave History - Collects Brave browser history.
-
Vivaldi History - Collects Vivaldi browser history.
-
-
3 new Windows OS Evidence Types:
-
Registry SAM Users - Collects Users and Groups from the SAM file. (Credit: Ashok K)
-
Brave History - Collects Brave browser history.
-
Vivaldi History - Collects Vivaldi browser history.
-
-
Persistence - A new Windows Evidence category for AIR which groups the following evidence items often essential to Windows DFIR investigations:
-
Active Script Event Consumers - Dump WMI Active Script Event Consumers.
-
Command Line Event Consumers - Dump WMI Command Line Event Consumers.
-
Registry Items - Enumerate Registry Items.
-
Scheduled Tasks - Enumerate Scheduled Tasks.
-
Service List - Enumerate Service List.
-
Startup Items - Enumerate Startup Items.
-
Security
-
New SSO integration capability via Okta (Credit: Brian W)
-
AIR now supports an integration with Okta allowing customers and partners to login securely with Single Sign-On for user authentication.
-
Enhancements
Security
-
Filter DNS traffic on Linux Isolation
-
The Linux asset isolation feature in AIR now offers more secure protection from any communication other than that coming from the AIR console. This enhancement mechanism mitigates possible attack techniques from:
-
DNS Tunneling
-
DNS Data Exfiltration
-
-
Functionality
-
Editable address for Relay Server
-
Flexibility and improved network management allowing users to set any IP or any FQDN for a registered relay server which provides flexibility and easy management on the network.
-
-
Investigation Hub hash to VirusTotal links
-
In the individual asset or case level Investigation Hub reports, every piece of evidence with a hash is now accompanied by an eye icon. Clicking this icon will direct you to the VirusTotal website for a detailed analysis of the hashes.
-
-
Off-Network Password File availability improvements
-
The BiUnzip tool now offers enhanced access to the passwords file, streamlining the decryption of multiple Off-Network zip files.
-
The Off-Network Asset passwords file will now always be available at; Asset (name) > Tasks > Details > Information Tab.
-
This update facilitates more efficient data extraction for our users. For detailed guidance on using the BiUnzip tool, please consult our Knowledge Base: biunzip
-
-
AIR agent disk space optimization during acquisition-compression
-
The AIR agent's disk space usage during the acquisition's compression phase has been optimized. This, combined with specific conditions, ensures a more efficient process to help the success rate of acquisition tasks.
-
-
Column Search in the Investigation Hub now working correctly
-
After conducting a global search in the Investigation Hub any ‘column search’ failed to return results - this is now fixed.
-
12/10/2023
Version 4.0
Features
Streamlining Workflows - Introducing the all new UI/UX for AIR
-
New floating header at the top of every page to allow immediate access to:
-
Searching across AIR.
-
Recent Cases, Assets, Tasks and Reports.
-
The Quick Start button to launch AIR Tasks.
-
Notifications
-
Current Organization name display, with a dropdown to switch between Organizations.
-
-
Organization selection improvements
-
To eliminate any potential confusion regarding the organization's assets you are currently viewing, the system now displays only one organization at a time.
-
Switching between Organizations has been made simpler via the Organization dropdown menu which provides access to:
-
Organization Settings.
-
Change Organization.
-
Add New Organization.
-
-
-
Main menu bar is now split into two sections:
-
The top section is now home to the core areas for AIR;
-
Home: Full overview of your AIR deployment.
-
Assets: Listing of current Assets.
-
Cases: Listings for open, closed and archived Cases.
-
Libraries: for Acquisition profiles, Triage Rules, interACT Files and Auto Asset Tagging rules.
-
-
-
The bottom section is home to AIR’s supporting functionality;
-
Integrations: API Tokens, Webhooks and Cloud Platforms.
-
Activity: With Insights, Recents, Notifications and Audit Logs all clearly displayed for analysts.
-
Tasks: All of your Console Tasks displayed in one window for searching and filtering.
-
Timelines: To review existing or create new Timelines.
-
Settings: The bottom of the Main Menu is the new home for all of your Settings; Assets, Security, Features, Users/Roles, Evidence Repositories, Policies and Backup.
-
-
New Secondary Menu Bar
-
This new menu appears when a Main Menu item is selected.
-
This is collapsible to maximize your screen’s working space but at the same time, allows users to drill down in AIR functionality at speed.
-
-
New Navigation Bar
-
This allows the user to see exactly where they are in every screen of the AIR platform by showing the ‘path’ to the current view.
-
-
Access to Recents via the Homepage
-
Direct access to Recent Cases, Recent Assets, Tasks and Reports - making it easier to pick up where you left off.
-
-
New Bulk Actions Bar
-
Found at the bottom of the Asset page to count the number of assets selected and provide easy access to the Taskings that can be applied to those assets.
-
-
Settings changes
-
Moving the “Enable Policies” toggle from the Policies page to Settings > Features
-
New Operating System support - IBM AIX
-
IBM AIX Off-Network Agent
-
AIX is a series of widely used Unix operating Systems for business critical applications developed by IBM.
-
These systems have proved tricky to investigate and are not covered well by existing security products, but now AIR provides the necessary support to do so.
-
Investigation
-
Introducing the AIR Investigation Hub, formally known as Consolidated Reports
-
For ease of access and to create a collaborative investigative space, the new Investigation Hub is now available from the secondary menu bar within each individual Case.
-
New Forensic Evidence Collections
-
15 new macOS Evidence Types and a new Evidence Category:
-
Downloads - presents information about downloaded files.
-
IP Route - presents IP route information.
-
Logged Users - shows currently logged in users.
-
Network Interfaces - presents NIC information.
-
Event Taps - reveals items that have a tap into the system.
-
DNS Resolvers - presents DNS resolution information.
-
Quicklook Cache - reveals items previewed with Quicklook.
-
Cron Jobs - presents scheduled/cron jobs
-
Arc History - collects Arc browser history.
-
Reopened Apps - shows apps not installed but in re-opened plist.
-
-
Persistence - New category which groups the following evidence items often essential to macOS DFIR investigations:
-
Mail Rules - collects mail rules that contain AppleScripts.
-
Login Hooks - these hooks can be used to achieve persistence.
-
Logout Hooks - as above.
-
Emond Clients - Emond accepts events from services.
-
Most Recently Run - The MRU lists the most recents files a user accessed.
-
-
Forensic image files in a single Zip file.
-
This release introduces a new toggle switch, giving users the option to enable or disable the consolidation of physical disk or volume image files into a single zip file, eliminating the need to split them into chunks.
-
Integrations
Yet more Webhooks for AIR to supercharge your SOC's automated data collection and analysis capabilities:
-
Webhook parser for SentinelOne. (Credit: Dane Z)
-
Webhook for Microsoft 365 Defender.
-
Cisco AMP/XDR.
Enhancements
Security
-
Password Protection for AIR Agent Uninstallation
-
We already provide Tamper Detection for the AIR Agent - now users can only uninstall the AIR Agent if they have access to the password to do so.
-
Agent uninstallation through the OS UI is disabled. The agent can only be uninstalled using shell commands with the protection password as an argument, locally or remotely (e.g., SCCM).
-
Uninstallation via the AIR UI or API remains possible without requiring a password.
-
Investigation
-
Detailed Browser History and Download History
-
In this release, we've refined the representation of Chrome browser forensic data, particularly within the browser and download history evidence segments, including:
-
Referrer details
-
Signature
-
Hash values
-
Timestamps
-
Visit duration insights, and others.
-
-
These enhancements enable analysts to conduct a more in-depth browser forensic examination.
-
-
Timeline Enhancements
-
Horizontal scrolling functionality has been added, making it simpler to navigate and concentrate on specific dates and times within your timelines.
-
-
Prefetch Parsed Referenced Files
-
Users can now more easily analyze prefetch records as AIR now displays 5 categories of information in a single view.
-
-
Character limitation for single triage rule
-
To prevent the browser becoming unresponsive we have limited the maximum to 350K of characters in a single Triage Rule.
-
Fixes
-
Password Recovery - Email Fix
-
If SMTP is not configured, AIR can not send emails. Previously, users attempting a password reset were told to check their email, leading to confusion when no email arrived. We've updated this to now prompt users to contact the administrator instead.
-
-
Timezone inconsistencies in Investigation Hub
-
Timezone data will now be displayed in the user's local browser time and timezone information will be displayed to the user at the top of the Investigation Hub page.
-
This timezone setting can not be changed by the user.
-
-
YARA rule failed to validate
-
Validation of some correct YARA rules was failing, this has been modified and now works correctly. (Credit: Nick H)
-
-
Improvements to Offline Installer Scripts (Credit: Blake B)
12/10/2023
18/09/2023
Version 3.12.4
Hot Fix
-
We have made the Consolidated Report button enabled for Cases that were created before version 3.12.3 was released. Users can now use Consolidated Reports as expected without any problem.
-
To learn more about consolidated report- read this article.
-
When a Task is Failed, even though an error message reflects the issue, shown as an “Unexpected Failure” message within the Tasks Details page (by hovering over the “eye” icon in the Status tab); the Console did not report the correct status immediately. We have fixed this issue and the correct status is now reported.
-
When a user chooses a 'Custom Option' to collect evidence and the mode of "Direct Collection" toggle (on Linux or MacOS) is changed while a Task is still running, the agent may crash. We have fixed this issue to avoid the possibility that the agent will crash.
07/09/2023
Version 3.12
Features
Streamline your investigation
-
DRONE analysis for macOS
-
MITRE ATT&CK Analyzer
-
As of v3.12 DRONE now has MITRE ATT&CK rules for macOS.
-
-
Dynamo Analyzer (Credit: Dilek G)
-
Dynamo will parse the AIR report generated as the result of a task assignment and highlight suspicious entries.
-
-
Browser History Analyzer
-
Chrome, Edge, IE (7-11), Firefox, Opera, Safari, Vivaldi, Waterfox and Brave are now all supported for macOS
-
-
Audit Event Analyzer
-
Brings advanced capability to AIR by scanning event records for keywords, hacker tools, and commands, setting verdicts based on criteria, guidelines, or Sigma rules.
-
-
-
Tooltips added to DRONE findings within the Consolidate Report
-
When a user hovers above a Verdict or Score finding listed in the Table view, they will be presented with a to a tooltip that explains how the result is derived.
-
-
Isolation of macOS endpoints
-
Expanding Isolation capability to the last major operating systems -macOS. (Fully supports Windows, Linux & macOS devices).
-
Regardless of the isolation state, the endpoint maintains communication with the AIR console to allow analysts performing their investigation by generating Tasks as usual.
-
-
Addition of a "Retry Upload" action for failed Task Assignments (Credit: Daniel M)
-
Should a failure occur during the evidence upload phase of a task, a "Retry Upload" feature is now available to resolve issues more efficiently. Key benefits include:
-
Elimination of the need for evidence re-acquisition, preserving the original data.
-
No additional disk space consumption.
-
The "Retry Upload" option repurposes the existing task assignment for the re-upload, preventing task duplication.
-
-
-
Simpler access to Off-Network Agent logs & Drone log files
-
Agent logs and Drone log files of Off Network are now saved in the same folder . This makes it easier to find any log files and share them with Binalyze Technical support or for troubleshooting by yourselves.
-
File name format is: Troubleshoot-[TIMESTAMP].zip.
-
Enriching evidence and artifacts
-
New Artifact types collected for macOS:
-
Discord Desktop Cache
-
Discord instant messaging and VoIP social platform with voice calls, video calls, text messaging, media and files in private chats or as part of communities called "servers".
-
-
Parallels Logs
-
Parallels is a software company best-known for Parallels Desktop for Mac that allows users to run Microsoft Windows systems on macOS computers.
-
-
Homebrew Logs
-
Homebrew is a free and open-source software package management system that simplifies the installation of software on macOS, as well as Linux.
-
-
Sophos Events Database
-
Sophos develops products for communication endpoint, encryption, network security, email security, mobile security and unified threat management.
-
-
Sophos Antivirus Logs
-
The AIR agent will now collect Sophos Antivirus logs.
-
-
-
New Evidence types for macOS:
-
Shared File List
-
The SharedFileList (SFL) in macOS is a system feature that manages "recent items" lists for applications and the system itself. These lists could include recently used applications, documents, servers, or even volumes. The files with the extensions .sfl and .sfl2 are plist (property list) files in binary format.
-
-
Shell/Bash History
-
The .bash_history file holds significant value for various reasons including command tracking which may reveal the activity of an attacker. However, note that the .bash_history file can be manipulated, cleared, or even disabled by knowledgeable users.
-
-
Synchronization and collaboration between teams
-
Customizable Banner Message (Credit: Helen T)
Users can now display important announcements via a banner on the console GUI for events like maintenance, upgrades, or config changes. The banner interface allows:
-
Scheduling via Start/End dates
-
Message editing - up to 512 characters
-
Color customization
-
URL linking
-
Banner dismissal to maximize screen space
This feature provides direct communication with AIR users and offers permission controls for message settings.
Enhancements
AIR Core Functions Enhancements
-
-
Timeline
Swipe through a Timeline Bar to view events, dates, or time periods that are outside the current visible area.
-
-
Click-and-drag: The user clicks on the timeline bar and drags it left or right to scroll through the timeline.
-
Swipe wheel: If the device supports a scroll wheel or touchpad gestures, the user can use it to scroll left or right on the timeline bar.
-
-
-
Triage
Many more new triage rule templates are available to assist when constructing triage task assignments including:
-
-
YARA - Find by size range
-
YARA - Find Portable Execution files only
-
YARA - Find PKZIP files only
-
YARA - Find by hash value after filtering by file size
-
Sigma - User account hidden by registry
-
osquery - Unusual Cron entries
-
osquery - Processes running with no binary on disk
-
-
-
Consolidated Reports Enhancements
-
Consolidated Report Module refactoring to provide Generic Report Module
-
This new module generates individual task assignment reports that maintain the same view and structure as the existing Consolidated Reports.
-
-
Triage results from osquery are now available in Consolidate Reports
-
osquery results are now also searchable from the Global Search.
-
Security Enhancements
-
Automatically renew default AIR SSL certificate (Credit: Ramesh P)
-
The Binalyze-generated self-signed certificate will now auto-renew when it's within 10 days of expiration.
-
Fixes
-
Issues connected with CPU limitations have been resolved (Credit: Helen T)
-
Expired Task Assignments will no longer delay subsequent Task Assignments (Credit: Christian K)
07/09/2023
24/08/2023
Version 3.11.1
3.11.1 is all about Timeline enhancements and bug fixes. Binalyze team would like to thank its customers who shared their feedback and input to help us improve the quality and usability of the Timeline Bar, Flags and Filters.
Enhancements
-
Several Timeline improvements including;
-
-
Enhanced Date and Time Selection: Users can now specify both start and end dates, with precision down to individual hours, facilitating more granular timeline investigations.
-
User-Defined Navigation: The introduction of arrow-based navigation allows users to move backward and forward through user-specified periods, as determined in the date/time selector.
-
Refined Zoom Capability: The Timeline histogram now supports zoom functionality down to a singular hour for precise analysis.
-
Dedicated Tab for Flagged Items: We have reintroduced a specialized tab within the Timeline view to prominently display flagged items, ensuring streamlined navigation for significant events.
-
Fixes
-
Event Id not displayed in Timeline UI
-
-
The Event ID artifact now populates its details in the Title column of the AIR Timeline UI. (Credit: Grant O)
-
-
Timeline flagging fixes
-
-
We've implemented multiple fixes to the flagging feature in the Timeline, resulting in overall usability enhancements.
-
21/08/2023
Version 3.11.0
Important Security Update (Credit - Caleb T and Tyler B)
We have added ACL settings to a driver object to prevent unauthorized access and potential privilege escalation.
Users should urgently deploy the updated agents to address this high-severity vulnerability
21/08/2023
08/08/2023
Version 3.10
NB: The MongoDB relies on the CPU architecture that runs your AIR server. For this update, AIR v3.10, the CPU has to be newer than 2011 for both Intel and AMD processors. If your processor architecture is older than this, it is not advised to update MongoDB.
Features
-
Disk Space limit configuration for Acquire Evidence Tasks
-
-
When evidence collections are stored on the local machine, this new feature, for macOS and Linux, will allow AIR users to determine the amount of free disk space to always be left available to the local user.
-
If a collection is not complete when the allocated disk space limit is reached, the collection at that point and the .ppc will be available to the analyst in the normal way.
-
The Task Status will be marked ‘Partially Completed’.
-
Task Logs will now be available in the Case Report, under Case Info, and in Consolidated Reports in the Case Summary. These logs will list any uncollected evidence items.
-
-
Bandwidth limit configuration for Acquire & Image Evidence Tasks
-
AIR users now have the ability to determine the amount of network bandwidth they wish to allocate to their AIR collections.
-
-
Ability to purge locally saved acquisition task data
-
This new action, ‘Purge Local Data’, will create a ‘Purge’ Task to remove all data generated for a task assignment on an endpoint.
-
Purge Local Data can also be run from the Case’s page to purge all data generated for a task assignment on an endpoint.
-
Purging local data will not affect the installed AIR agent, so it remains ready for new task assignments.
-
To use Purge Local Data, the privilege “Delete task assignment” is required.
-
Binalyze AIR now supports the collection of over 350 evidence items.
New evidence types collected for Windows:
-
LNK Files
-
AIR will analyze and parse LNK files which are often abused by hackers, who can leverage them to use legitimate applications (such as PowerShell) to download malware or other malicious files.
-
-
Users
-
User accounts are created and stored as objects in Active Directory Domain Services. These accounts can be compromised by bad actors and programs such as system services used to log on to a computer. A successful login generates an access token which includes the security identity and group memberships of the user account associated with the process or thread. Every process executed on behalf of this user has a copy of this access token.
-
-
Timeline
-
Windows 10 Timeline feature enables users to: (i) View their currently running apps and look back at their previous activities such as; opened documents, programs, images, videos or visited websites. (ii) Synchronize activities across devices. (iii) Provide information about applications that were executed within the last 30 days, such as application name, time when it was launched and its duration. This information can be of forensic value, helping to reconstruct events, even if the files, documents or applications have been deleted.
-
-
UAL Logs
-
User Access Logs (UAL) store a lot of information and often present IT admins with privacy concerns. One such feature helps correlate an account and the source IP address with actions performed remotely on systems, so potentially valuable to attackers. (Credit: Daniel M)
-
New Evidence Types For macOS:
-
Apple Audit Logs
-
macOS writes important operational and security information that can be useful to an attacker as a place to obfuscate changes that were recorded. As part of defense-in-depth, the files in /var/audit should be owned only by root with group wheel with read-only rights and no other access allowed. macOS ACLs should not be used for these files.
-
-
AnyDesk Logs
-
AnyDesk is a remote desktop application that provides platform-independent remote access to personal computers and other devices running the host application.
-
-
Teamviewer Logs
-
TeamViewer is a German remote access and remote control software application often concerned with the maintenance of computers and other devices.
-
New Evidence Type For Linux:
-
AnyDesk Logs
-
(See above)
-
-
Filtering of Tasks to determine the presence of DRONE data
-
AIR now creates a metadata flag: ‘hasDroneData’ which indicates that DRONE data exists for a particular Task and reports with DRONE data can be filtered for in the endpoint’s Task listings.
-
-
‘biunzip’ is a new command-line tool from Binalyze specifically designed to extract zip files generated by the AIR Off-Network Agent.
-
You can download the latest release of biunzip from the releases section on GitHub: Let’s build from here
-
Biunzip will either unzip a single zip file or unzip zip files in a directory using a CSV file.
-
This capability will allow running off-network investigation at scale, and at speed with minimum effort.
-
Enhancements
-
Huge Timeline improvements
-
The timeline events bar is now displayed in histogram format, making it clear when activity has taken place.
-
The timeline bar now has zoom-in and zoom-out capabilities allowing users to drill down from decades to individual hours.
-
Findings flags will be shown in the timeline bar.
-
Filtering down via start and end dates is now possible as is filtering by; decades, years, months and days.
-
-
Hash Values for all Event and Registry Files are now shown in all Case and Consolidated Reports.
-
These hash values are searchable via Global Searching.
-
-
Last Used fields added
-
To help better understand analyst’s activity within AIR, a ‘Last Used Field’ has been added to the following pages:
-
interACT Library
-
Evidence Repositories
-
API tokens
-
Webhooks
-
Acquisition (profiles)
-
Triage (profiles)
-
-
-
Backup AIR every 4 hours
-
It is now possible to automate your AIR backups to take place every 4 hours, or or as was available in previous versions; daily, weekly and monthly. (Credit: Daniel M)
-
-
Loading Bar added for Async Commands
-
A loading bar for ongoing asynchronous commands is now displayed in all interACT shell sessions.
-
Fixes
-
No significant fixes needed this month
05/07/2023
Version 3.9.2
Features
-
Acquisition Profiles now display average time taken to complete
-
-
This great new feature displays to the user the average time it takes to run a particular acquisition profile in their own AIR environment. This will help analysts make decisions as to which Profile is best suited to a particular circumstance. (Credit: Daniel M)
-
This feature is unique to the users own environment, so the collection of metrics will start afresh with each new AIR console install.
-
-
New wizard to add endpoints to a Timeline
-
This dedicated Timeline wizard will speed up and simplify the addition of endpoints to your Timelines. The new flow allows you to select endpoints, define the Task and then choose the post acquisition analyzers such as DRONE or any of the other AIR analyzers needed for your specific investigations.
-
This feature is aligned with the new Quick Start feature introduced in v3.8 - Both designed to simplify and speed up your investigations.
-
-
Five new Webhooks available in AIR:
-
Stellar EDR
-
LogicHub SOAR (DEVO)
-
Rapid7 InsightIDR
-
Fortigate SIEM
-
Dynatrace
-
Take advantage of AIR’s Webhooks to increase your SOC’s automated collections and analysis of data from endpoints and dramatically speed up all of your investigations.
-
New macOS evidence support - Apple System Logs
-
Apple System Log Files (.asl files) contain detailed records of various system events, processes, errors, warnings, and activities that occur on a macOS device.
-
-
New macOS evidence support - Apple Unified Logs
-
The Apple Unified Logs (AUL) system was introduced with macOS 10.12. It creates a standard log format used in all Apple operating systems, including macOS, iOS, watchOS, and tvOS. One of the most powerful filtering capabilities of AUL is the predicates.
-
AIR will present unified logs using the comprehensive set of predicates shown below:
-
User login events
-
Tccd events
-
Ssh activity events
-
Command line activity run with elevated privileges
-
Kernel extension events
-
Screen sharing events
-
Keychain unlock events
-
Sessions creation and destruction events
-
Detecting and blocking malicious software events
-
Failed sudo events
-
MDM Clients Events
-
-
Enhancements
-
Consolidated Report improvements
-
To support collaboration between analysts by highlighting important evidence and findings, we have added the option to bookmark items within Consolidated reports.
-
Users can also see who bookmarked an item and when they did so. They can also apply filters to show ‘Bookmarks’ or ‘Bookmarked by’.
-
A new ‘event viewing’ window will display expanded details for any item selected in the main viewing area.
-
Global Search has been enhanced for faster search returns.
-
-
YARA rule scans can be run via interACT
-
It is now possible to run YARA scans inside the AIR cross-platform remote shell, interACT. (Credit: Ramesh P)
-
-
YARA and Sigma rules use the same verification method
-
Binalyze AIR will now use matching validation methodologies for these two different rule types, so YARA and Sigma scanning can no longer be tasked to run any incompatible rules. (Credit: Antonio L)
-
Fixes
-
AWS S3 upload failures
-
Simultaneous upload issues to AWS S3 bucket and all other repositories have been fixed by enforcing sequential uploads only. (Credit: Simon L)
-
-
Reporting a Failed Status
-
When a Task is running, and something causes the agent to restart, a ‘failed’ status will be shown when the agent starts again if any of the tasks fail to complete.
-
-
Timeline imports to Chrome
-
An issue preventing Chrome uploads to the AIR Timeline has been resolved.
-
-
Authentication Errors for Public API's are fixed
05/07/2023
12/06/2023
Version 3.8
Features
-
New Quick Start wizard for launching AIR tasks.
-
-
This new feature is available from all AIR Console views, it speeds up and simplifies the launching of AIR tasks; Acquire Evidence, Acquire Image, Triage, interACT, Timeline, Compare and Schedule Acquisition.
-
-
Disk Images
-
AWS S3 and Azure evidence repositories now provide support for forensic disk image acquisitions. (Credit: Daniel M)
-
-
Downloading from Evidence Repositories - For individual endpoint Case Reports, it is now possible to directly download the evidence.zip file associated with that report:
-
A download button will be shown for the following sources:
-
-
AWS
-
Azure
-
-
-
A URL with a copy button will be shown for the following sources:
-
-
Local
-
SFTP
-
FTPS
-
SMB
-
-
-
-
AIR Backup - AWS S3 is now a supported repository for AIR backups (Credit: Daniel M)
-
Relay Server - Not everyone can have direct access from all of their endpoints to the AIR console. This new AIR Relay Server/traffic router capability, will allow network segments which need to remain air-gapped to communicate with the AIR console.
*This feature will be enabled per demand. If you're interested, contact your customer success.
Enhancements
-
Task Naming - Users can customize the individual Tasks' name. In doing so, this will override the default auto-task naming function. If the user decides not to give the task a customized name, AIR will revert to its auto-task naming convention.
-
Settings Menu - Streamlining the main settings menu by relocating the following to the sub-settings tab; Users/Roles, Evidence Repositories and Licence options.
-
The new settings menu is grouped as follows:
-
General - Version, Logging, License, Connection, Console Proxy.
-
Endpoints - Agent updates,, Tamper detection, Active directory.
-
Security - SSL certificate, SSL root CA, Console port, IP restriction, Authentication, SSO.
-
Features - Enable interACT, Resolve Agent Public IP, Case selection, RFC3161 Time-stamping, SMTP, Syslog / SIEM.
-
Users/Roles
-
Evidence Repositories
-
Backup
-
New artifacts for collection - For macOS, in both ‘Full’ and ‘Quick’ acquisition profiles we have added; Quarantine Events, Sudo Last Run, iMessages, Dock Items (dock.plist) and Document Revisions.
-
UX improvement - In the Timeline view it is now possible to select or deselect all evidence categories with a checkbox found at the top of the evidence category listings.
-
UI improvements - To improve workflow:
-
When creating a New Case in AIR, the Organization field will not be automatically populated anymore, it will remain blank so that the user is ‘forced’ to think about which Organization the New Case should be attributed to.
-
The auto expansion animation has been removed from the left side navigation menu of the UI.
-
Evidence Repository - It is now possible to define a Domain Name for any new SMB Evidence Repositories.
-
Triage Rules - There is now no limit to the number of triage rules available to investigators.(Credit Antonio L)
-
Yara - AIR’s version of Yara has been updated to Yara v4.3.1.
-
interACT opens in a new window - allowing users to continue to use the Console UI and have several interACT sessions active simultaneously.
-
interACT auto-complete - Navigation between the auto-complete options is now possible with tab key. (Credit: Christian K)
-
$mft as a .csv improvement - The full file path for each $mft record entry will now be included in the .csv generated by an AIR, ‘$mft as csv’ collection.
-
CPU limit for macOS - Users can now limit the amount of CPU usage available to the AIR agent on the endpoint when assigning a task.
Fixes
-
OSquery on Triage bug fixes. (Credit: Christian K)
-
Timeline bug fixes. (Credit: Ramesh P)
11/05/2023
Version 3.7
Features
-
Triage Match Count Column
-
In the Task window it is now possible to select, from a column selector, to display a column for Match Counts, and if the user filters by Triage the Match Count column will be added automatically to the filtered results.
-
-
New Webhook - Microsoft Sentinel
-
AIR now has built-in support for a Microsoft Sentinel Webhook (Credit to Elisa.com - Finland).
-
-
Mandatory Case Selection Option
-
This new feature allows Enterprise and MSOC customers to enforce the selection of a case for all Acquisition and Triage tasks ensuring that all collections and tasking results are attributed to a case. For FIS customers this feature will always be active by default.
-
-
New Chrome artifacts for Mac Linux and Windows
-
For Mac, Linux and Windows support has been added for parsed evidence from Chrome; Bookmarks, Cookies, Downloads, User Profiles, Extensions and Browsing History
-
-
Isolation Support for Linux
-
Linux endpoints can now be 'Isolated' from within the Endpoints Details UI window.
-
-
New 'Last Seen' Endpoint Filter
-
AIR now allows for the date and time filtering of endpoints by; 'Last Seen After', 'Last Seen Before' and 'Last Seen Between'.
-
-
Apple macOS TCC collection
-
AIR now supports the collection of Mac TCC (Transparency, Consent and Control) data.
-
IMPORTANT: In order to benefit from these new features, you should install our new DataBase. Click here to learn more.
Enhancements
MITRE ATT&CK enhancements
-
MITRE ATT&CK Rules with Drone for Acquisition and Triage Tasks
-
Users can now see and select the MITRE ATT&CK analyzer in both the Acquire Evidence and Triage Tasking windows. In these views it is now also possible to see when AIR last checked our MITRE ATT&CK database to ensure that the user has access to the latest MITRE ATT&CK definitions for AIR.
-
-
MITRE ATT&CK Rules support for off-network tasks
-
The same level of support mentioned above for MITRE ATT&CK is now also available for off-network Evidence Acquisitions and Triaging.
-
-
MITRE ATT&CK Tactics Widget View within Consolidated Report
-
The Consolidated Report now aligns and displays artifacts by the number of times a particular MITRE ATT&CK Tactic, Technique or Finding has been identified. The Technique and Sub-Technique identified will also be displayed along with a direct link to the relevant MITRE ATT&CK webpage.
-
-
MITRE ATT&CK Auto update
-
Binalyze AIR will now automatically check for any new MITRE ATT&CK updates as soon as a user opens the Acquire Evidence or Triage Tasking windows. An internet connected AIR installation is required, ensuring customers always have access to the latest AIR MITRE ATT&CK definitions. (Off-Line support will be coming in future versions)
-
Consolidated Report enhancements
-
Consolidated Report: MITRE ATT&CK Report View
-
The Consolidated Report front page now displays a MITRE ATT&CK overview report.
-
-
Consolidated Report: Event Records Consolidation
-
Event Records are now consolidated in human readable format for investigators.
-
-
Consolidated Report: Global Search
-
Global Searching is now possible across Consolidated Reports. This feature addition is super powerful, and allows users to search across all of the acquisition and triage data that constructs a Consolidated Report from multiple endpoints in any particular case.
-
-
Consolidated Report: Process Details View
-
An event details module has been added at the bottom of the evidence item page, so when an item is selected in the upper window, if there is additional information available it will be displayed in the lower details window.
-
-
Consolidated Report: Process Tree View
-
A Tree view is now available for processes within Consolidated Reports.
-
-
Consolidated Report: CSV export
-
It is now possible to export Evidence Items from within the Consolidated Report to CSV.
-
Fixes
-
Security fix related to endpoint isolation
-
Security fix related to the installation process
-
Security fix related to the password reset process
-
Security fix related to access to server files
11/05/2023
17/04/2023
Version 3.6
Features
-
Public key authentication support was added to SFTP evidence repositories
-
Users can use public key authentication on SFTP servers or services such as Amazon Transfer Family to store the evidence and artifacts.
-
Users can use either a username and password authentication or public key authentication on SFTP on Evidence Repository
Enhancements
-
N/A
Fixes
-
Minor bug fixes
10/04/2023
Version 3.5.1
Features
-
Consolidated Report.
-
The Consolidated report is a single, easy-to-read DFIR intelligence report, that displays Acquisition and Triage acquired data from multiple endpoints in one report.
-
Triage with OSQuery.
-
Analysts can now create, modify and run OSQuery queries across multiple assets in the AIR Triage GUI, along with our pre-existing YARA and Sigma capabilities.
-
Timeline support was added for Linux and macOS.
-
Investigators and analysts can add Linux and macOS artifacts to AIR Timelines. Leverage this addition to have just one Timeline with multiple endpoints from all 3 operating systems; Windows, Mac and Linux. This is potentially another massive boost to speeding up investigation times.
-
Importing Chrome/Chromebook collections to Binalyze AIR Console
-
Investigators and analysts can now add standalone Chrome evidence acquisition results (PPC file) to Binalyze AIR
-
New Artifacts and Evidence for macOS and Linux.
-
More than 35 new artifacts and evidence types, such as Apache, Nginx, MySQL, PostgreSQL, MongoDB, Docker, KnowledgeC, and more system-related logs were added to Binalyze AIR
-
Organization Tags
-
Managed SOCs partners (MSSPs) can add, remove, list and group their Organizations by Tags. This would simplify operational day to day needs, since it is much simpler to define and classify each Organization by 1 or multiple Tags. The new capability is available also via the API.
Enhancements
-
N/A
Fixes
-
interACT get the command’s unresponsiveness bug fixed
-
interACT session termination bug fixed
10/04/2023
10/03/2023
Version 3.4.3
Features
-
Network Capture for Linux and macOS
-
Beginning in version 3.4, the network capture feature is available on Linux and macOS operating systems.
-
-
Display Real IP Addresses of Endpoints by using XFF (Credits: Aaron V.)
-
AIR Console can read and parse the HTTP requests and XFF headers from the Forward Proxy and associate them with the assets to determine the assets' real IP.
-
-
x64 support for Off-Network Microsoft Windows
-
Beginning in version 3.4, Microsoft Windows 64-bit Off-Network binary package is available and can be run on supported 64-bit architectures.
-
-
Disk Imaging
-
Binalyze AIR provides disk imaging which we call “Acquire Image”, for Microsoft Windows, Linux, and macOS operating systems.
-
-
The last Seen Endpoints filter parameter was added to API (Credits to Garmin)
-
“Get Endpoint” API request now has the Last Seen Endpoints filter parameter. So the assets can be listed by the last seen date.
-
-
AIR for Chrome
-
AIR For Chrome is the evidence collector extension for Chrome and ChromeOS. AIR For Chrome extension allows investigators and analysts to capture forensically sound data with a single click at machine speed.
-
Enhancements
-
The character limitation on the hostname field of the Endpoints is removed.
-
Beginning in version 3.4, there will be no character limitation for assets' hostnames. Assets that have hostnames longer than 15 characters won't be trimmed and shown as they are.
-
-
The Endpoint Details page has been improved
-
The new endpoint details page is more organized and practical and provides more information about the asset.
-
The name of the System Resources tab has been changed to Hardware, and Volume and disk information will be shown here.
-
Acquire button function has been expanded. When it is clicked, Acquire Evidence and Acquire Image options will appear, and users can select any of them to start a data acquisition or disk/volume imaging task.
-
Disk and volume imaging, what we call Acquire Image tasks, can be performed in Volume or Disk tabs under the Hardware section of the Endpoint Details page.
-
06/02/2023
Version 3.3.1
Features
-
Multiple Sigma Rule Upload
-
Investigators and Analysts can upload multiple Sigma rules to AIR Console at once
-
-
Taking Full Logical Volume Images by using the user interface
-
Investigators and Analysts can create full logical volumes of images using either a user interface or a secure remote shell interACT.
-
Microsoft Windows, Linux, and Apple macOS operating systems are supported
-
-
x64 support for Windows Agent
-
Beginning in version 3.3 64-bit version of the Microsoft Windows AIR Agent is available.
-
-
Case ID Prefix
-
Customers using more than one Binalyze AIR Console instance can now add a prefix to their Case IDs. Therefore there will not be experienced any confusion about Case IDs anymore.
-
-
Progress monitoring added to Get & Put commands on the interACT
-
Investigators and Analysts can see the file download progress from an endpoint (get command) and file upload to the endpoint from the library (put command) command outputs while using secure remote shell interACT.
-
-
MITRE ATT&CK Scanner was added to Binalyze AIR Automated Threat Analyzer, DRONE
-
When Investigators and Analysts scan their systems with DRONE, they can see the MITRE ATT&CK mapped results in the report. DRONE rules are continuously developed and mapped to the MITRE ATT&CK framework.
-
Enhancements
-
Some security improvements on AIR Console
-
Some performance improvements on AIR Console
Fixes
-
Minor bug fixes
06/02/2023
11/01/2023
Version 3.2.4
Security Hot fix
-
Binalyze AIR uses the JWT library that was compromised, immediate actions have been taken to remediate and AIR v3.2.4, containing the hot-fixes for the related vulnerabilities, has been released as of today. This includes fixes for the indirect vulnerabilities due to second-level dependencies.
Therefore, it is strongly recommended to update your existing AIR deployments to this latest version AIR v3.2.4 at your earliest convenience.
10/01/2023
Version 3.2.3
Hot Fix
-
Hot fix that includes typo fixes, timeline date filtering, and browser back button navigation caused regarding the dashboard
10/01/2023
05/01/2023
Version 3.2.2
Features
-
Activity Overview Dashboard added
-
Activity Overview Dashboard is a dynamic dashboard that provides tabular and graphical information about the usage, benefits, and return on investment of the Binalyze AIR in the enterprise company.
-
-
Progress Monitoring was added to InterACT secure remote shell
-
Investigators can track the progress of the command and estimate how much time is left on the interACT shell
-
-
AIR Agent Proxy Support
-
AIR agent automatically identifies the proxy configuration on the endpoint and configures itself to access the required services over the proxy service.
-
Enhancements
-
Miscellaneous package and dependency updates
Fixes
-
Several bugs fixed
30/11/2022
Version 3.1
Features
-
Golden image option was added to AIR Agent installation
-
AIR agent is now compatible with installation via a golden image for new device deployment. With this feature enabled, an administrator can prevent potential connection and availability problems that may have previously occurred on the AIR console for machines installed from a golden image.
-
-
New File System Enumeration evidence for Linux and macOS
-
Investigators can list the creation, modification, and access dates and times of the files and folders on the Linux and macOS filesystem as CSV files.
-
Enhancements
-
Baseline Comparison Reporting
-
Collapse/Expand All items under the Acquisition Profile section.
-
Acquisition Profile information was added to the Tasks list under the Endpoint details page.
-
YARA 4.2 update
-
FTPS support for full disk image
-
SSL/TLS proxy server support was enhanced
30/11/2022
02/11/2022
Version 3.0.5
Features
-
RFC-3161 compatible evidence signing for the chain of custody
Enhancements
-
New Asset status, "Off-Network," added
-
AIR Console domain address updates are enhanced
-
New evidence types added
-
Docker Artifacts for Linux OS
-
Browser History Artifacts for Linux OS
-
Browser History Artifacts for macOS
-
RAM image collection for Linux
-
-
Agent uninstallation and purge operations are enhanced
-
Multi-file upload for Off-Network devices
-
Path of the evidence files added
-
Local IP addresses added to the endpoint details page
-
The full disk image for macOS
Fixes
-
Case activity reporting to Binalyze cloud services [credit: Nixu]
-
DNS and ICMP Protocols are filtered when Endpoint Isolation
04/10/2022
Version 2.10.2
Features
-
AWS EC2 one-click agent deployment
-
Cloud forensics - Azure VM support
-
Azure VM one-click agent deployment
-
Auto Asset Tagging based on hostname, IP address, and subnet
-
Auto Asset Tagging based on custom rules with osquery builder
-
Linux full disc image via interACT
Enhancements
-
7x speed improvement for most evidence acquisitions on macOS and Linux
-
You can now upload multiple YARA rules at once
-
Improved troubleshooting logs
-
Token support for MFA
Fixes
-
Fixed an issue where sometimes recycle bin collection would fail
-
Fixed an issue that prevented baseline comparison on unreachable endpoints
-
Other minor bug fixes
04/10/2022
16/09/2022
Version 2.9.3
Fixes
-
Fixed an agent uninstallation issue on Linux and macOS
-
Fixed an issue where in some cases, disk imaging would hang
01/09/2022
Version 2.9.1
Features
-
Added ability to enumerate Amazon AWS EC2 assets
-
Added Yara triage support to macOS assets
-
Added Baseline comparison for macOS assets
-
Added full disk image collection with interACT for Windows assets
Enhancements
-
Added ability to duplicate acquisition profiles
Fixes
-
Fixed an issue where notifications were not shown about tasks in non-default Organisations
-
Fixed the wrong warning message when deleting a task from a case.
-
Fixed an issue where the user couldn't see the baseline comparison report even though the baseline acquisition task was finished.
-
Fixed the name column sorting in the interACT Library
01/09/2022
04/08/2022
Version 2.8.2
Features
-
Added off-network Acquisition and Triage with portable agent
-
Added interACT for macOS
-
Added Tamper Detection for macOS agent
Enhancements
-
API now includes endpoints for Policy, Auto Asset Tagging, Triage Rules, and Users (Docs)
-
interACT shell now supports backslash (\) for newline
-
Updated and improved the powershell deployment script
-
Improved efficiency of e-Discovery and custom content collections
Fixes
-
Fixed an issue where some users were not able to upload files to the interACT library
-
Fixed an issue where sending the same acquisition twice to the same timeline would result in duplications
-
Fixed an issue where an evidence repository that’s in use in a policy could be removed from the console
-
Fixed limitation on username length
08/07/2022
Version 2.7.2
Fixes
-
Fixed task migration scripts update
-
Fixed scheduled task comparison is missing on Baseline Comparison
-
Fixed connecting AD user with less than 5 characters
-
Fixed spelling mistake is shown On ESXi Agent Deployment Page
-
Fixed UI issues about ESXi tab
08/07/2022
01/07/2022
Version 2.7.1
Fix
-
Fixed a bug related to agent uninstallation process
29/06/2022
Version 2.7.0
Features
-
Added support for Apple macOS assets
-
Added Chromebook standalone collector (credit: Yuta K.)
-
Added ESXi standalone collector (credit: Andres S. and Mason T.)
Enhancements
-
Case selection is now optional with an Enterprise or MSOC license
-
API now includes endpoints for Repositories, Baseline, Case and Organizations (Docs)
-
Improved the retry process for interACT’s get and put commands
Fixes
-
Fixed issue with downloading files with special characters via interACT
-
Fixed acquisition history graph on the dashboard
-
Fixed other minor functionality and UI issues
-
Fixed UTC time mismatch in DRONE for Windows event logs and event records
-
Fixed DRONE stability issue when using keyword search
29/06/2022
10/06/2022
Version 2.6.1
Features
-
Added asset baseline forensic comparison
-
Added support for FTPS evidence repositories
-
You can now have interACT sessions with isolated Windows endpoints
Enhancements
-
Added new evidence and artifact types to Windows acquisition
-
All active interACT sessions are now ended when interACT is disabled from settings
-
Added "New Rule" shortcut to Triage assignment screen
-
Added keyboard support for confirming and dismissing popups (Enter/Esc)
-
Improved evidence compression performance
-
Enabled option not to compress evidence on collection
-
Upgraded interACT curl executable to version 7.83.1
-
Upgraded interACT osquery executable to version 5.2.3
-
Improved performance of agent installation on Windows
Fixes
-
Improved Auto Asset Tagging task assignment
-
Improved UI performance in various locations
-
Improved security of sensitive credentials saved in the AIR setting
-
Fixed an issue with the status of the agent update task
-
Fixed a bug in the interACT zip command
-
Fixed a minor bug in unique case directory creation on endpoints
-
Fixed other minor bugs
09/05/2022
Version 2.5.1
Fix
-
Fixed a bug in the DRONE configuration file migration process.
09/05/2022
21/04/2022
Version 2.5.0
Features
-
Added DRONE support for Linux
-
Added Sigma rule triage to Linux
-
Added shareable deployment feature
-
Added new organization management page
-
Added osquery command to interACT
-
Added mkdir command to interACT
-
Added sort and tree options to interACT pslist command
Enhancements
-
Added SSL Enforcement for accessing AIR.
-
Added auto asset tag rules for Apache, Redis, Mysql and Rabbitmq
-
Added tamper detection type to audit log description
-
Added filtering endpoints by label
-
Added filtering audit logs by endpoint name
-
Added TACTICAL and DRONE KB download links
-
Added required privileges section to interACT command help pages
-
Improved endpoint update performance
-
View and Update Organization privileges moved from system privileges to user privileges
-
Hardened to prevent less-privileged users from accessing sensitive settings data
-
Upgraded interACT curl executable to version 7.82.0
-
Improved tamper detection
-
Improved triage to allow the same Yara rule name in different rulesets
-
Added time frame limit to DRONE Event Records Analyzer
-
Improved DRONE Ransomware Analyzer performance. Added total and per channel limit for Events of Interest and Event Records analyzer.
Fixes
-
Fixed a minor issue on global search
-
Fixed evidence repository path validation bug
-
Fixed Endpoint label delete issue
-
Fixed e-Discovery patterns search issue
-
Fixed interACT curl command's missing CA certificates on Windows
-
Fixed a bug in sigma triage to kill DRONE process when task is canceled
-
Fixed an issue with the DRONE Linux x86 build.
-
Fixed other minor bugs
-
UI/UX improvements
16/03/2022
Version 2.4.0
Features
-
Added e-Discovery collection to acquisition profiles (credit Yalkin D.)
-
Added Tamper detection to agent
-
Added agent support for Linux arm64 (aarch64)
-
Added curl command to interACT
-
Added hex command to interACT
Enhancements
-
Added IP Address column to Endpoint table
-
Added silent installation tooltip for SCCM agent deployment
-
Added endpoint name to audit log filter
-
DRONE keyword search capability is now more visible
-
Improved zip command in interACT - Now zips to folder
-
Added new metrics for case report memory section
Fixes
-
Fixed unquoted service path issue after a config update (CVE-2021-42563)
-
Fixed minor issues on timeline export
-
Fixed duplicated user validation issue
-
Fixed evidence repository name and path validation issue
-
Fixed system resource usage not updating in interACT session issue
-
Fixed renaming evidence repository issue
-
Fixed an issue that allowed task assignment to endpoints with an old agent
-
Fixed webhook addresses not updated after a change of console address
-
Fixed SFTP current directory support
-
Fixed opening report issue in Safari browser
-
Fixed minor issue on Sigma rule parser
-
Fixed minor issue on Drone table
-
Fixed minor UI issues
16/03/2022
09/03/2022
Version 2.3.6
Fixes
-
Fixed a bug that broke the database migration step on v2.3.5
-
Fixed minor memory leak in the Events of Interest analyzer
23/02/2022
Version 2.3.5
Features
-
Added Sigma rule triage for Windows
-
Added autocomplete functionality to interACT
-
Added ServiceNow support to webhooks
Enhancements
-
Added new privilege to allow changing endpoint label
-
Added auto asset tag rules for Docker and Kubernetes
-
Added version information to settings
-
Added ability to handle Unicode file paths in YARA scanner
-
Added ability to specify a temporary staging directory for acquisition tasks that use evidence repository
-
Improved evidence collection on low capacity endpoints by letting AIR automatically select the volume with the greatest available free space (credits: Babak M.)
-
Improved evidence repository background upload mechanism with persistent retries
-
Improved case export functionality
Fixes
-
Fixed minor memory leak of canceled tasks
-
Fixed minor logging issues
-
Fixed interACT exec command stdin issues on Windows
-
Fixed a bug related to listing unsupported drone analyzers
-
Fixed case filter issue
-
Fixed policy list on task creation, missing policies
-
Fixed case-sensitive username issues
-
Fixed case day counter
-
Fixed minor bugs on the report
-
Fixed other minor bugs
23/02/2022
24/01/2022
Version 2.3.0
Features
-
InterACT: A cross-platform remote shell session capability that allows the users to run commands on remote endpoints for triage, mitigation, and remediation purposes in situations such as cyber incident response activities.
Enhancements
-
Improved windows agent installation
-
Improved endpoint tag assignment
-
Increased timeout duration for Azure Blob Storage
Fixes
-
Fixed incorrect tag-endpoint count
-
Fixed scheduled instant execution
-
Fixed invalid SFTP port
-
Fixed returning wrong http status code for invalid evidence repository Id
-
Fixed organization search criteria
-
Fixed timeline wrong date range issue on export
-
Fixed multiple role assignment issue on UI
-
Fixed showing "Reset filter" button in the timeline
-
Fixed organizations tag gaps on the UI
-
Fixed privilege hierarchy issue between organization and global admin roles
-
Fixed not showing 404 page for case section
-
Fixed webhook URLs display issue in some cases
-
Fixed duplicated start date field in scheduled task detail
-
Fixed no link issue on "see details" text on Settings > Connection page
-
Fixed broken KB links for Webhooks and SSO
09/12/2021
Version 2.2.1
-
Added Slack integration support
-
Added Mattermost integration support
-
Fixed timeline sort issue
-
Fixed viewing case.ppc issue on failed tasks
09/12/2021
25/11/2021
Version 2.2.0 (RC)
Features
-
Added exporting endpoints as CSV
-
Added exporting cases as CSV
-
Added exporting case activities as CSV
-
Added exporting case notes as CSV
-
Added exporting case endpoints as CSV
-
Added exporting audit logs as CSV
-
Added exporting timeline events as CSV
-
Added Yara external variables and removed yara+ modules (file, process)
-
Upgraded Yara to 4.1
-
Enriched triage case report for file matches for Linux
Enhancements
-
Added webhook support for Elasticsearch Logstash Kibana (ELK)
-
Added webhook support for SumoLogic
-
Improved task queues
-
Improved triage performance
-
Improved handling of cancel tasks
-
Improved connection timeouts
-
Improved log rotation
-
Improved log format
-
Improved logging
-
Improved Triage case report
-
Updated the application icon for the Windows agent
-
Added timeout for evidence repositories on agent
Fixes
-
Added retry for agent HTTP requests
-
Added retry for failed case file uploads
-
Introduced Linux systemd service restart on failure
-
Fixed compression progress reporting
-
Fixed HTTP response close
-
Fixed a race condition for HTTP transport
-
Fixed progress reporting
-
Fixed self match possibility of custom content collection for Linux
-
Fixed misc. minor bugs
18/11/2021
Version 2.1.5
-
UI/UX improvements on case containers
-
Fixed minor bugs related to case containers
-
Fixed drone autopilot issue on scheduled tasks and webhooks.
-
Fixed a bug about using azure storage as evidence repository on linux agents
18/11/2021
9/11/2021
Version 2.1.0 (RC-2)
-
Added additional functionality to cases feature
-
Minor fixes and improvements
01/11/2021
Version 2.0.5
-
Added FQDN support for console address
-
Added a Quick Intro guide to help new users get started with AIR
-
Fixed an issue on SSO with 8443 port
-
Console migration process moved to task logic
-
Minor Linux agent fixes:
-
Minor http timeout fix
-
Minor triage command line parameter fix for excluded files
-
Visit poll interval overflow fix for 32bit architectures
-
-
Minor Windows agent fixes:
-
Minor improvement on isolation
-
01/11/2021
12/10/2021
Version 2.1.0 (RC)
New:
-
Added case container feature
-
Added FIS license support
Fixes:
-
Fixed a minor issue related to the auto-asset-tagging feature
-
Fixed organization admin privileges issue
-
Minor UI/UX fixes
22/9/2021
Version 2.0.1
This is the stable version of the latest RC (v2.0-RC)
In this version;
-
Added new predefined acquisition profile: Compromise Assessment
-
Added deployment script support for Windows agents
-
Added webhook parser for Cortex XSOAR and Splunk Phantom
-
Added new evidence type for Windows agents: Collecting USB Storage History
-
Improved license validation messages
-
Improved temporary path usage for Windows agents
-
Fixed a bug related to timeline event count
-
Fixed a bug related to sending events to syslog
-
Fixed a bug related to canceling Auto Tag Asset task on Windows agents
-
Major performance improvements
22/9/2021
9/9/2021
Version 2.0 (RC)
New:
-
Added AIR-DRONE Integration (available only for acquisition and timeline for now) - rapid keyword searching, anomaly finding, scanning SIGMA rules live directly on any endpoint, and many other DRONE features are available now in AIR.
-
Added Auto Asset Tagging feature - tag your assets automatically by the conditions you provide.
-
Added Off-Network Endpoints feature - add and filter off-network endpoints.
-
Added PPC Import to Timeline feature - import PPC files collected from offline or online environments to Timeline.
-
Added IP Restrictions feature - restrict access to the AIR Console based on IP addresses or IP blocks.
-
Added UI Port Splitting feature - enables you to serve AIR Console and Endpoint requests from separated ports. With this feature, you can create separate firewall rules in AIR.
-
Added Drone findings on the Timeline
-
Added SMB Repository Support for Linux
-
Added Pardus Linux Support
-
Added Super glob meta (double star) support for custom content
-
Added IP Restriction Reset Script
-
Added an ability to download case reports from the endpoint detail task page
-
Added hashes.csv file that contains hashes of the files in the case report
-
Added detailed step by step task statuses (Processing, Compressing, Uploading, Analyzing)
-
Added support for .pfx, .der SSL certificate types
-
Added supported Linux distributions information to deploy the page
-
Added "Send to Timeline" action to Acquisition tasks
-
Added displaying support for PPC file metadata
-
AIR UI has a new design layout now
Improvements:
-
Improved more user-friendly error messages
-
Improved database connection functionality on backend
-
Improved case report view options on the endpoint detail page
-
Improved global search bar visibility for each page
-
Improved notification module "Mark All as Read" accessibility
-
Improved showing EULA in AIR setup
-
Improved and simplified AIR deployment with Docker for Linux
-
Improved performance while opening the Case Report.
-
Improved SSL Certificate installation
-
Minor improvements/fixes on case report
-
Upgraded MongoDB version to 4.4.7
Fixes:
-
Fixed an issue related to uninstallation of windows agent manually
-
Fixed LDAP issue occurring while trying to login AIR with:
username@domain format -
Fixed task queue cancellation
-
Fixed Proxy SSL issue
-
Fixed organization name update issue
-
Fixed organization filter bug on the policy creation page
-
Minor UI/UX fixes
18/8/2021
Version 1.8.3
-
Minor changes and improvements
Go to knowledgebase to learn how to migrate from v1.7.61 to v1.8
18/8/2021
17/8/2021
Version 1.8.2
This is the stable version of the latest RC (v1.8.0-rc)
In this version;
-
Added AIR CLI Support
-
Added to restore using a backup file support
-
Added to reset local user password support
-
-
Improved AWS S3 Bucket upload on Windows agent
-
Improved Custom Content Collection on Windows agent
-
Fixed some minor bugs
Go to knowledgebase to learn how to migrate from v1.7.61 to v1.8
14/7/2021
Version 1.8.0 (RC)
New:
-
Added Docker-based installation support. Once a stable version of v1.8 is released, docker will be the only deployment option. Since then, the MSI installer will no longer be available. Our knowledge base page is available to show how to install the new version of AIR
-
Added multiple organization support.
-
Added stateless queue-based background worker system.
-
Added device name and os on agent visit requests.
-
Added deployment token to deploy endpoints more secure way.
-
Added some rules to prevent confusion and irregularity on users/roles (Only Global Admins can create Roles, predefined roles cannot be updated).
Improvements:
-
Added ability to unisolate an endpoint, whether it's already isolated or not, for easier troubleshooting.
-
Added predefined roles: Organization Admin, L1&L2 Analyst, L3&L4 Analyst, Maintenance Engineer.
-
Added authorization guard for unauthorized users while accessing organization-specific resources and deployment-related pages.
-
Optimized all database indexes for the organization system.
-
Moved policy priority-based config to order-based config.
-
Improved the stateless task scheduler.
-
Improved create tag rest endpoint for organization system.
-
Improved policy-endpoint match stats.
-
Improved caching by moving it from in-memory to a queue-based infrastructure.
-
Improved the backup feature.
-
Updated policy priority/order to clear up the confusion
-
Removed default SMTP connection, users have to enable the SMTP settings to send emails such as password reset
-
Improved auto-isolate operation after reboot
Fixes:
-
Fixed task data error on getting task by id.
-
Added aborting existing TCP connections after Isolate operation
Additional instructions for existing customers:
-
Once a stable version of v1.8 is released, migration documentation and technical support will be provided for existing customers.
14/7/2021
12/7/2021
Version 1.7.61
-
Fixed NATS blocking call problem.
-
This is the last AIR Console version that supports the MSI installer. In future releases, Docker will be the only deployment option.
2/7/2021
Version 1.7.60
-
Fixed password reset bug.
-
Improved endpoint console address migration feature.
2/7/2021
21/6/2021
Version 1.7.55
-
Added ability to change the console address to migrate endpoints to a new AIR instance.
9/6/2021
Version 1.7.50
This is the stable release of the previous RC version (v.1.7.45)
-
Fixed a bug upgrading endpoints with old version to newer version
-
Fixed notifying NATS for the endpoints that need to be upgraded to the new version
-
Fixed a bug regarding database backup
-
Added support for validating settings for Azure Blob Storage and AWS S3
9/6/2021
27/5/2021
Version 1.7.45 (RC)
-
New Feature: CSV import support for Timeline
-
New Feature: Amazon S3 Bucket evidence repository support
-
New Feature: Azure Blob Storage evidence repository support
-
New Feature: LDAPS integration support
-
Changed Triggers to
Webhooks -
Added Sources field for Investigation
-
Added support for deleting timeline resources
-
Added LimaCharlie Webhook support
-
Added new predefined YARA rule:
NSA Mitigating Webshells -
Added name field to evidence repositories
-
Improved timeline filtering
-
Improved timeline performance
-
Improved progress reporting based on percentage and time on Linux agent
-
Improved recursive directory walk when compressing case directory on Linux agent
-
Improved isolation task assignment validation
-
Improved task cancellation for network share evidence repository on Windows agent
-
Improved SFTP upload on Windows agent
-
Fixed delay on task receiving after an agent is upgraded to a new version
-
Fixed deploy script bug for non-HTTPS servers
-
Fixed minor bugs on Linux agent
-
Fixed an issue in YARA scanner on Windows agent
6/5/2021
Version 1.7.41
-
Minor bug fixes
6/5/2021
27/4/2021
Version 1.7.40
-
New feature: AIR-QRadar integration. Now, an acquisition can be started by triggering AIR via QRadar (credits: Esra Kulüp)
-
New feature: Added Roles and Privileges. Starting from this version AIR contains 70+ user privileges for more fine-grained control
-
New feature: Added backup support for case reports and config files. (Database backup is already available beginning from v1.7.16)
-
New feature: Added AES encryption option for backups
-
New feature: Added SFTP support to store backups on the remote server
-
New feature: Added performing bulk operations on the selected endpoints (adding/removing tags, deleting endpoints, starting acquisition triage, and much more. credits: Babak Mirzahosseiny)
-
New feature: Added triage support to Linux. Now, the file system and memory can be scanned using YARA rules. (credits: Hilko Bengen (https://github.com/hillu/) Author of go-yara (https://github.com/hillu/go-yara))
-
New feature: Added Custom Content collection from Linux distributions
-
Added progress update for compression and SFTP upload process on Linux
-
Added sending matched triage rules to Syslog
-
Added advance filter options to data grids
-
Added auto-generated shell script to facilitate Linux deb and rpm packages deployment
-
Added AIR integration guideline to documentation
-
Improved policy creation UI & UX
-
Improved setup process UI & UX
-
Improved custom SSL certificate information
-
Improved task completion status UX
-
Improved nats communication in agent
-
Implemented more secure cookie-based authentication
-
Optimized Audit logging performance
-
Optimized Syslog bulk processing performance
-
Fixed changing proxy settings when the license is lockdown
-
Fixed an issue in the agent installer
-
Fixed some security vulnerabilities
-
Minor changes and bug fixes
31/3/2021
Version 1.7.35
-
New feature: GNU/Linux support for Debian and Redhat based distributions (Preview)
-
New feature: Added compression and encryption support for evidence
-
New feature: Added policy support that gives you the ability to manage evidence repository location, compression, encryption, and CPU limit based on rules (credits: Turkcell CDC)
-
Added extended file information for triage files
-
Added dependecy checking to evidence repository deletion process
-
Added linux acquisition evidence list
-
Added "Use options provided in policies" and "Use custom options" choices to the acquisition, triage, trigger process
-
Added platform column to endpoint datagrid
-
Added platform, isolation status, and policy filters to endpoint page
-
Added Linux deploy steps to deploy page
-
Added assigning log retrieval task to offline endpoints.
-
Optimized caching to minimize performance bottlenecks caused by high request load
-
Optimized security token check performance
-
Optimized concurrent message handling on Nats server
-
Refactored worker pool to works based on priority
-
Refactored the endpoint task queue to work with the task configs in policies and custom configs
-
Removed patrol from AIR
-
Fixed XSS exploit on audit logs
-
Fixed the performance bottleneck on the task progress update process
-
Fixed a memory leak in the visit process on the windows agent
-
Fixed a problem in windows agent installation version check
-
Updated EULA
-
Minor UX improvements
-
Minor bug fixes
31/3/2021
1/3/2021
Version 1.7.31
-
Fixed the bug related to task assignment to endpoints that are associated with multiple tags
25/2/2021
Version 1.7.30
-
Improved triage match results
-
Improved AD sync performance
-
Improved audit log db write transactions
-
Improved license capacity checks
-
Improved LDAP login
-
Highly optimized task core module performance
-
Highly optimized endpoint task queue memory usage
-
Highly optimized audit log storage
-
Highly optimized realtime task assignment to endpoints
-
Optimized logging on agent
-
Optimized debugging log on worker tasks
-
Optimized Agent Installer download performance
-
Optimized task result upload performance
-
Optimized db bulk operations
-
Optimized triage rule storage
-
Optimized task storage
-
Refactored worker core module
-
Fixed an issue related to sending triage task result
-
Fixed performance issue caused by Patrol module
-
Fixed disappearing endpoint tags after AD sync issue
-
Fixed loading up tasks to endpoint queue issue caused by db migration
-
Fixed the register required bug that is caused by latency on endpoint registration
-
Fixed the performance issue on visit requests caused by agent update load balancer
-
Fixed investigating same endpoints multiple times in the same investigation
-
Fixed security token mismatch bug on visit requests
-
Fixed the bug caused by reloading task details on the UI
-
Fixed the bug related to license validation for online and offline environments
25/2/2021
27/1/2021
Version 1.7.24
-
Fixed a critical issue on the task assignment module
24/1/2021
Version 1.7.23
-
Improved endpoint connection error logging
-
Changed max memory cache size to maximum
-
Highly improved memory usage of the endpoint task queue
-
Increased node's memory usage limit to 6GB
-
Reduced effect of long-running tasks on the starting speed of the application
-
Fixed performance and memory issue on sending events to Syslog and audit logs
-
Fixed a minor bug on the endpoint registration issue
-
Fixed a minor bug on fix endpoint issue task
-
Fixed a minor bug on the installer
24/1/2021
18/1/2021
Version 1.7.21
-
Fixed an issue in UI
-
Other minor bug fixes and improvements
14/1/2021
Version 1.7.20
-
Fixed minor bugs
14/1/2021
11/1/2021
Version 1.7.16 (RC)
-
Added getting endpoint system resources feature
-
Added database backup feature that allows admin to create database backups regularly (credits: Turkcell CDC)
-
Added version column to the endpoint page
-
Added two new endpoint issue types
-
Added agent update management feature (credits: Turkcell CDC)
-
Added capability to fix registration issue for endpoints that re-installed
-
Improved error report sending on the installer
-
Improved offline license check
-
Improved endpoint issue filter
-
Improved dashboard page statistics
-
Improved automatic page data polling
-
Highly improved backend and agent logs
-
Improved re-upload task mechanism
-
Fixed an issue on triggers that cause not to ignore recurring requests
-
Fixed getting 404 when trying to download an external resource from the report
-
Fixed an issue in task fail upload condition
-
Fixed an exception in downloads collector
-
Other minor bug fixes and improvements
2021
29/12/2020
Version 1.7.13 (RC)
-
Fixed an issue in agent installer
-
Other minor bug fixes and improvements
29/12/2020
22/12/2020
Version 1.7.12 (RC)
-
Highly improved Yara Scanner speed
-
Improved getting agent logs from AIR
-
Improved process collector
-
Fixed an issue in Yara Scanner
-
Fixed an issue in Prefetch collector
17/12/2020
Version 1.7.11 (RC Sunburst Edition)
Fixed minor typo
17/12/2020
17/12/2020
Version 1.7.10 (RC Sunburst Edition)
-
Added FireEye Red Team Tool Countermeasures Yara Rule
-
Added FireEye Mandiant SunBurst Countermeasures Yara Rule
-
Added support for both filesystem and memory triage
-
Added support for getting agent logs from AIR
-
Added support for agent log rotating
-
Highly improved AIR backend for concurrent operations
-
Fixed an issue in triage results
-
Fixed a minor issue in license
-
Other minor bug fixes and improvements
14/12/2020
Version 1.7.8 (RC)
-
Fixed an issue in event log parser
14/12/2020
10/12/2020
Version 1.7.7 (RC)
-
Added Log Retrieval action to endpoint
-
Added Timeline action to endpoint group and endpoint tag tree
-
Added Reset Password support for users
-
Added scroll support for timeline
-
Added downloading case entries from report
-
Improved TimelineIR experience
-
Fixed minor install/uninstall bugs
-
Fixed trigger recurrence bug
-
Fixed other minor bugs
-
Removed setting AD and proxy configs from the installer
3/12/2020
Version 1.7.6 (Beta)
-
Minor improvements and bug fixes
3/12/2020
30/11/2020
Version 1.7.4 (Beta)
-
Fixed an issue in event log parser
27/11/2020
Version 1.7.3 (Beta)
-
Added support for downloading report as HTML (credits: Turkcell CDC)
-
Improved Quick Acquisition Profile
-
Improved agent update mechanism (credits: Orhan Solak - Barikat Cyber Security)
-
Fixed an issue in agent task processing mechanism (credits: Burak Karapınar - HAVELSAN)
-
Fixed an issue in agent manual uninstallation (credits: Orhan Solak - Barikat Cyber Security)
27/11/2020
20/11/2020
Version 1.7.1 (Beta)
-
Added TimelineIR feature
-
Added Binalyze Patrol feature
-
Added audit logs feature
-
Added role-based access control
-
Added "Acquire Evidence", "Schedule Acquisition", "Triage" and "Delete Endpoint" actions by tag
-
Highly improved agent performance
-
Highly improved agent memory usage
-
Improved settings page to separate The Users, License, and Evidence Repositories pages
-
Improved case file upload to handle .ppc files
-
Improved the installer prerequisites to handle the newer version of NodeJS
-
Improved debug logs
-
The minimum memory requirement for the AIR server increased to 8GB
-
Other minor bug fixes and improvements
13/10/2020
Version 1.6.14
-
Added support for parsing SRUM Application Resource Usage
-
Added support for parsing SRUM Network Data Usage
-
Added new event records
-
Added MAC time to crash dumps
-
Added Custom Content collection from all drives (credits: Mason Toups)
-
Added Triage on all disk drives (credits: Mason Toups)
-
Added host content to report
-
Added export process table as CSV (credits: Alexander Jarvis)
-
Added Last Write Time for Installed Applications
-
Added support for CPU usage limitation (credits: Turkcell CDC)
-
Added Refresh button to the endpoint groups section
-
Added Delete All Tags button to the endpoint tags section
-
Added Delete button to all detail pages
-
Improved settings page design
-
Improved design of table action buttons
-
Improved Browser History acquisition
-
Improved Network Share connection check
-
Improved exception handling
-
Fixed an issue with event logs
-
Fixed WMI query exception problem
-
Fixed Downloads section processed count
-
Fixed an issue with timestamping
13/10/2020
27/9/2020
Version 1.6.11
-
Improved endpoint tags
-
Improved installer (credits: Babak Mirzahosseiny)
-
Fixed LDAP user login authentication (credits: Turkcell CDC)
-
Fixed LDAP endpoints register problem (credits: Turkcell CDC)
-
Fixed enable/disable debug logging bug
17/9/2020
Version 1.6.9
-
Added feature of adding tags to endpoints (credits: Yalkın Demirkaya)
-
Added LDAP Sync option to endpoint group tree
-
Added refresh button to the endpoint tags section
-
Added delete tag action to the endpoint tags section
-
Added New Profile button to acquisition profiles dropdowns
-
Improved server logger to make logs more readable
17/9/2020
8/9/2020
Version 1.6.8
-
Added the Recent Tasks section to the dashboard
-
Added task assignment delete option
-
Added Scheduled Acquisition edit option
-
Added confirmation modal to Active Directory settings
-
Added status line to the task detail page
-
Added select all option to triage list of the endpoint
-
Added uninstall task assignment for unmanaged endpoints on a visit request
-
Added onetime scheduled task removal after execution
-
Added task execution history to dashboard backend API
-
Added task assignment removal to backend API
-
Added nats server port status checker job
-
Added match count stats to task details
-
Added support to login with an LDAP account
-
Added sending user deleted event to Syslog
-
Added e-mail field for the user
-
Improved task removal
-
Improved LDAP sync (credits: Babak Mirzahosseiny)
-
Improved SMTP validation logic
-
Improved server restart logic (credits: Babak Mirzahosseiny)
-
Improved agent https connection (credits: Babak Mirzahosseiny)
-
Refactored task assignment and scheduler
-
Fixed changing LDAP endpoint group after visit request (credits: Babak Mirzahosseiny)
-
Fixed https redirection bug (credits: Babak Mirzahosseiny)
-
Fixed report process tree view
-
Minor improvements and bug fixes
14/8/2020
Version 1.6.4 (Code Name: Sirius)
-
New backend in NestJS (TypeScript) with 100% unit test coverage
-
New frontend in Vue.js
-
Added auto-complete support for YARA rule editor
-
Added support for YARA rule validation
-
Added group triage feature
-
Added global search feature
-
Added filtering support to all tables
-
Added local search for each page
-
Added security token refresh for triggers
-
Added new evidence types
-
Added new Custom Content collection editor
-
Added required port detection to the installer
-
Added Active Directory server setting alongside domain name
-
Added Memcache for decreasing response times
-
Added support for the upcoming Compromise Assessment feature (PPC file)
-
Added retry feature to agents in case there is no connection to evidence repository
-
Highly improved evidence selection page
-
Highly improved UX for task actions
-
Fixed minor issues in installer
-
Fixed minor issues in the Case report
-
Fixed an issue in NATS
-
Fixed an issue in license handling
-
Fixed Smart Screen warning on agent installation
14/8/2020
17/5/2020
Version 1.4.1
-
Added collection of Autorun locations
-
Added collection of Downloaded Files information
-
Added collection of RDP Cache Files
-
Added port availability check for the installer
-
Added new license models
-
Added support for offline licensing
-
Added support for task cancellation
-
Highly improved report
-
Highly improved calculation on visit interval
-
Improved UI/UX
-
Fixed an issue with timezone handling
-
Fixed an issue in group task assignments
-
Fixed app manifest problem for console service
-
Removed internet dependency from the installer
-
Minor updates and improvements
13/4/2020
Version 1.4
-
Added support for Triage on FileSystem and Memory using YARA+
-
Added support for installation on Windows 7+ OSes
-
Added support for assigning a task to all endpoints in endpoint groups
-
Added support for sending case report after the task completion
-
Added support for anonymous network share connections
-
Added support for send notifications for failed tasks
-
Added Online filter into endpoints page
-
Added support for network share folder permissions check
-
Added support for updating endpoint details for upgraded OSes
-
Added support for filtering with endpoint groups are added
-
Added resilience to case report sending
-
Added sending match count after triage task completes
-
Added Yara rule validation
-
Added validating Yara rule file
-
Added sending Yara rule error message if the wrong rule provided
-
Added sending duration during the task
-
Highly improved evidence acquisition to network shares
-
Improved agent logs
-
Improved exception handling
-
Improved uninstall task
-
Improved fetching array from JSON
-
Improved network share authentication
-
Fixed an issue in LDAP Sync
-
Fixed unhandled exception with JSON GetValue
-
Fixed unhandled exception
-
Fixed wrong function usage for JSON
-
Fixed an issue with agent log
-
Removed unnecessary console API calls
-
Removed console out messages
-
Removed .NET Core dependency
-
Minor updates and improvements
13/4/2020
2020
26/12/2019
Version 1.3.6
-
Fixed an issue in agent update
-
Fixed an issue in license handling
-
Fixed a UX issue in agent register
25/12/2019
Version 1.3.5
-
Improved UI/UX
-
Highly optimized client connection handling
-
Highly optimized database operations
-
Added support for Custom Content
-
Added support for Syslog
-
Added console auditing logs
-
Added support for DB migration
-
Added edit button to tables
-
Added endpoint filter links to dashboard statistics
-
Improved license handling
-
Performance optimizations
-
Fixed an issue in LDAP synchronization
-
Fixed an issue leading to duplicate domain
-
Fixed an issue in tasks page showing incorrect endpoint
-
Fixed an issue in task scheduler
-
Fixed an issue in installer test LDAP button
-
Fixed an issue in installer test proxy button
-
Minor updates and improvements
25/12/2019
21/11/2019
Version 1.3.3
-
Improved UI/UX
-
Added validation to settings save
-
Fixed screenshot not captured issue
-
Fixed clipboard not captured issue
-
Fixed UsnJournal not retrieved issue
-
Fixed Active Directory paging issue
-
Fixed multiple Active Directory groups issue
-
Added scroll to Active Directory groups
19/11/2019
Version 1.3
-
Major architectural improvements
-
Major security enhancements (credits: Mehmet İNCE & https://invictuseurope.com)
-
Improved NATS real-time messaging
-
Improved email template
-
Added support for generic Webhook integration with SIEM, SOAR, and EDR products.
-
Added Custom Content Collection
-
Added administrator manifest to installers
-
Added logging for prerequisities
-
Added LDAP / Proxy test buttons to settings
-
Added support for SSL
-
Added 404 Not Found pages
-
Fixed an issue with forgot password dialog
-
Fixed an issue with Console updater
-
Fixed an issue with client IP handling
-
Fixed an issue with environment variables
-
Other minor bug fixes and improvements
19/11/2019
2019
AIR was born on 21st October 2019 with our first public Beta release 1.2.1










