The shot came at 3:30 a.m. Eastern.
While most of the U.S. was asleep, more than 200,000 devices across 79 countries went dark. Laptops. Mobile phones. Medical workstations. On the Entra login page for one of the world's largest medical technology companies, employees were greeted by a symbol: the cartoon of a barefoot Palestinian child, arms crossed behind his back, staring at the horizon.
Handala had just hit Stryker Corporation. And nothing about it looked like a hack in the way most people still imagine one.
Operation Epic Fury and the Trigger
To understand what happened on March 11, 2026, you have to go back thirteen days.
On February 28, the U.S. and Israel launched Operation Epic Fury, a coordinated wave of airstrikes against Iranian nuclear facilities, banking infrastructure, and IRGC command centers. Among the targets hit that day was a girls' elementary school in Minab, in Iran's Hormozgan province. The Shajareh Tayyebeh school collapsed on its students. 156 civilians were killed, 120 of them children. Multiple independent investigations by Bellingcat, The New York Times, and Reuters concluded the munition was a U.S. Tomahawk missile, likely the result of faulty DIA coordinates. The U.S. government initially denied responsibility. Defense Secretary Pete Hegseth later promised a "thorough probe," which The Washington Post described as a tacit acknowledgement.
Handala announced its response the same day. The group cited the Minab school directly: "In retaliation for the brutal attack on the Minab school and in response to ongoing cyber assaults against the infrastructure of the Axis of Resistance, our major cyber operation has been executed with complete success."
The target was Stryker, a $25 billion medical device manufacturer headquartered in Portage, Michigan, with 56,000 employees across 61 countries.
How They Did It: No Malware Required
This is the part that should make security teams uneasy.
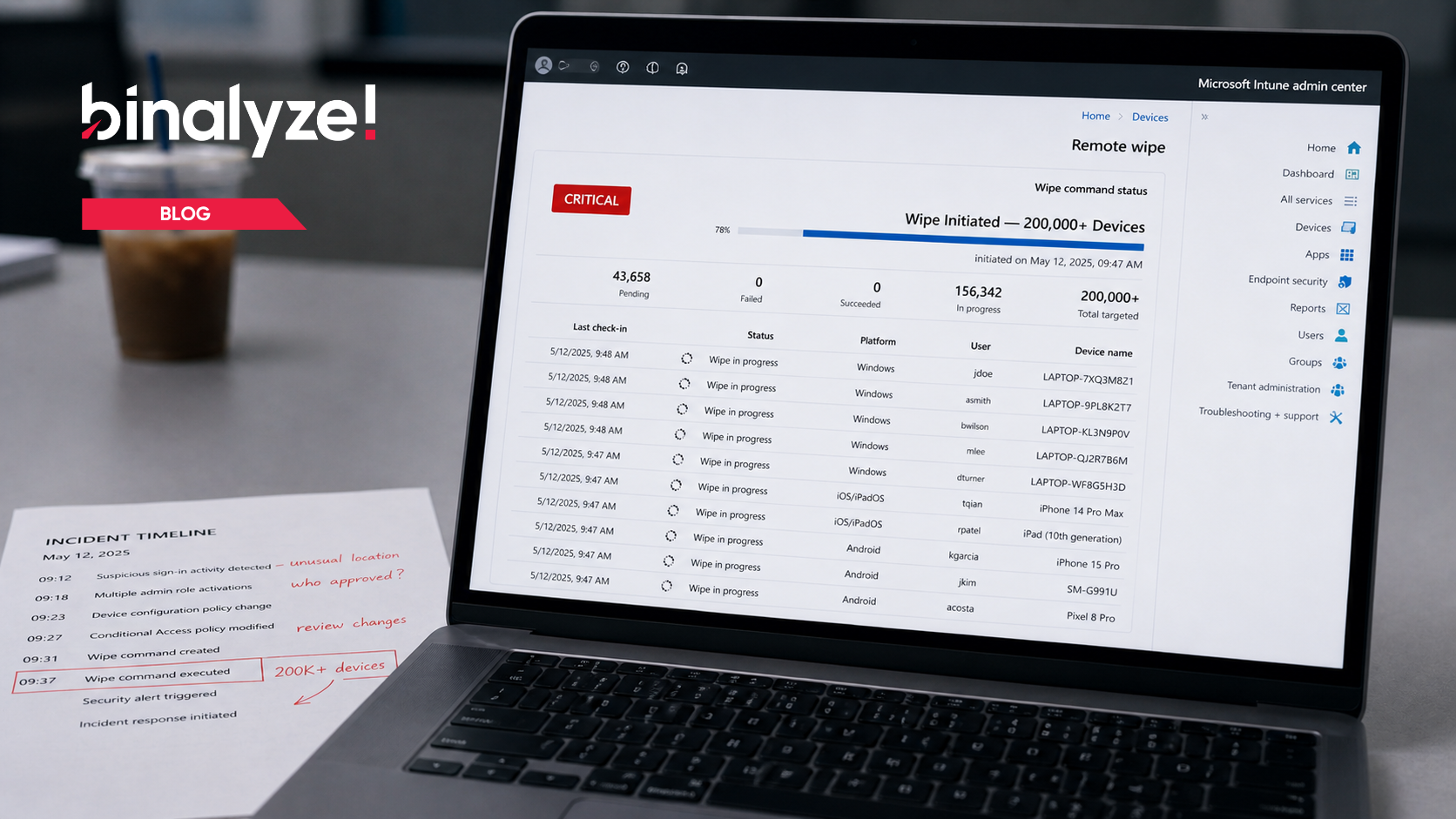
Handala didn't deploy a wiper. It didn't need to. The group compromised an administrative credential for Stryker's Microsoft Intune tenant, the company's own device management platform, and used Intune's built-in Remote Wipe feature to issue factory reset commands across enrolled endpoints.
That was it. No malware. No exploit chain. No exotic zero-day. Just a legitimate admin tool turned into a kill switch.
Starting at 3:30 a.m. EDT, laptops, tablets, phones, and Windows devices enrolled in Stryker's Intune tenant were bricked. Employees who had Outlook installed on personal phones said those were wiped too. More than 5,500 staff in Cork, Ireland, Stryker's largest non-U.S. base, were sent home when the network went down. Stryker's phone system in Kalamazoo played a recorded message saying the company was "facing a building emergency." The stock dropped 3.6% before markets had fully absorbed what happened.
Stryker's initial statement was blunt: "We have no indication of ransomware or malware and believe the incident is contained."
Technically accurate. Strategically beside the point. Your EDR doesn't light up when the attack looks like an IT admin doing routine work.
Why Stryker? The Targeting Logic
Handala called Stryker a "Zionist-rooted corporation." That framing was deliberate. The group needed a justification that fit its narrative. But the targeting logic was more concrete than the slogan.
In 2019, Stryker acquired OrthoSpace, an Israeli medical technology firm. That acquisition placed Stryker on MOIS's target list. A U.S. company. Global footprint. Israeli corporate ties. Medical supply chains serving hospitals in conflict-adjacent nations. Stryker was a visible target, but more than that, it was a disruptive one.
The Guardian quoted my view of the attack directly: this looked like "the first drop of blood in the water" from nation-state and hacktivist activity spilling out of the Iran conflict, and more shots were likely coming.
I still think that's right. This was not a one-off. It was a proof of concept.
The Wiper Is the New Normal, Possibly for a While
Here's the part people need to sit with: wiper attacks are not new for Iran. Saudi Aramco in 2012. Sands in 2014. The Albanian government in 2022. Iran has a long, documented history of using destructive cyber operations as a geopolitical instrument. What changed with Stryker was the method and the geography.
Weaponizing an MDM platform is a living-off-the-land attack. It uses infrastructure security teams are supposed to trust. Standard malware detection is blind to that. Your EDR sees a legitimate admin action. Your SIEM logs expected behavior. You find out when employees can't turn their laptops back on.
And the tempo is not slowing. April 2026 brought a Passover-timed operation that wiped 22TB of data across 14 companies at once. FBI, CISA, and the Department of Energy issued a joint advisory warning that Iran-linked hackers were actively targeting PLCs and SCADA systems in U.S. water, wastewater, and energy sectors, manipulating HMI displays and disrupting operational technology. ProCircular's Andrew Chipman put it well: "The threat of cyber-attack from Iran is real. History teaches us that hospitals and medical service providers are prime targets for the regime and its supporters. However, any critical infrastructure is a potential target."
This is not going to burn out on its own. Iran's regime is fighting for survival after Operation Epic Fury decimated parts of its leadership structure. Its nuclear program has been pushed back. Its conventional military capacity has taken real damage. What it still has, and what it has long been effective with, is cyber.
Wiper attacks are cheap compared with their impact. One compromised admin credential can trigger downstream damage across hospitals, supply chains, and financial systems. They generate headlines without necessarily triggering a kinetic response. For an adversary in Iran's current position, that is an efficient playbook.
Expect more of this. The attack surface is huge. Any organization with supply chain exposure to Israeli or U.S. defense interests is in scope. The methods will keep changing, but the Stryker playbook is portable: compromise an MDM admin account, issue mass wipes, and let the chaos do the rest.
The Stryker attack was not a warning shot. It was a template.
Lee Sult is Chief Investigator at Binalyze, specializing in digital forensics, incident response, and threat intelligence. Follow for continued analysis on Handala and Iranian nation-state cyber operations.









