2 min read
New in Binalyze AIR v1.7.50: Enriched Timeline with CSV import
![]() Amina Zilic
:
Fri, Sep 10, '21
Amina Zilic
:
Fri, Sep 10, '21

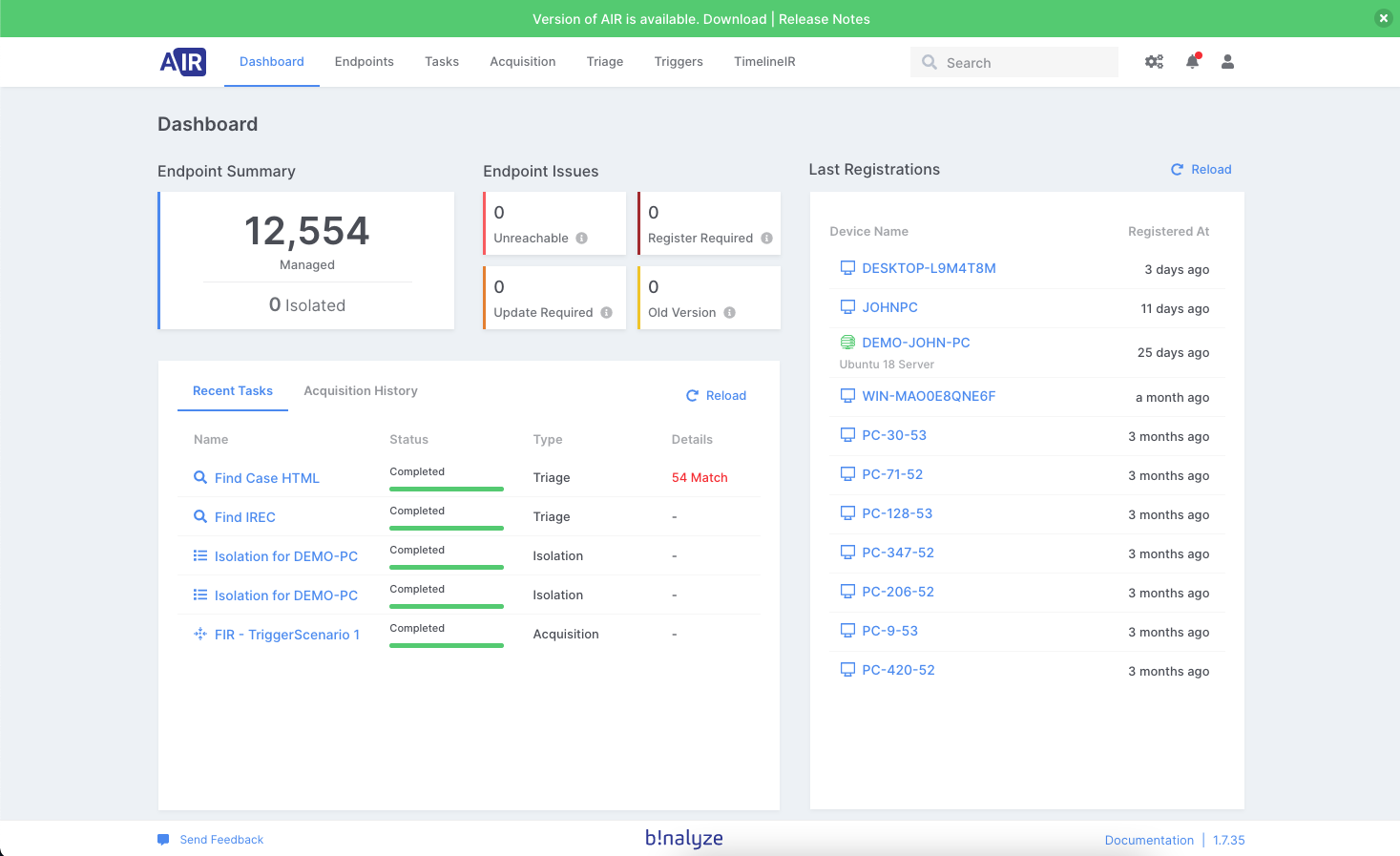
Binalyze AIR v1.7.50 is now available.
You can update directly from your product (shown below) or download it from the product page.
 Product release highlights:
Product release highlights:
-
Enriched timeline with CSV import
-
Microsoft Azure and Amazon S3 Bucket evidence repositories
-
NSA web shell detection YARA rules
This blog post covers more details about the new feature set. You can go to the latest release notes.
CSV import
After the first release of our Timeline feature, we started getting good feedback regarding the ease of use, simple UI/UX, and robust feature set. Along with that, we also received quality feedback for further enrichment of the timeline feature, so the first in line was – CSV import.
With the latest AIR release, we have enriched the Timeline capability with the CSV import feature that gives you the possibility to upload your own CSV file and start analyzing the uploaded data on your AIR Timeline. These CSV files can be collected from your cloud platform, firewall logs, or anywhere else. The source doesn’t play any role here. The important thing is that you can upload and start analyzing CSV files quickly and in a simple, collaborative way.
Before demonstrating the enrichment with the CSV file, let’s first create a new timeline.
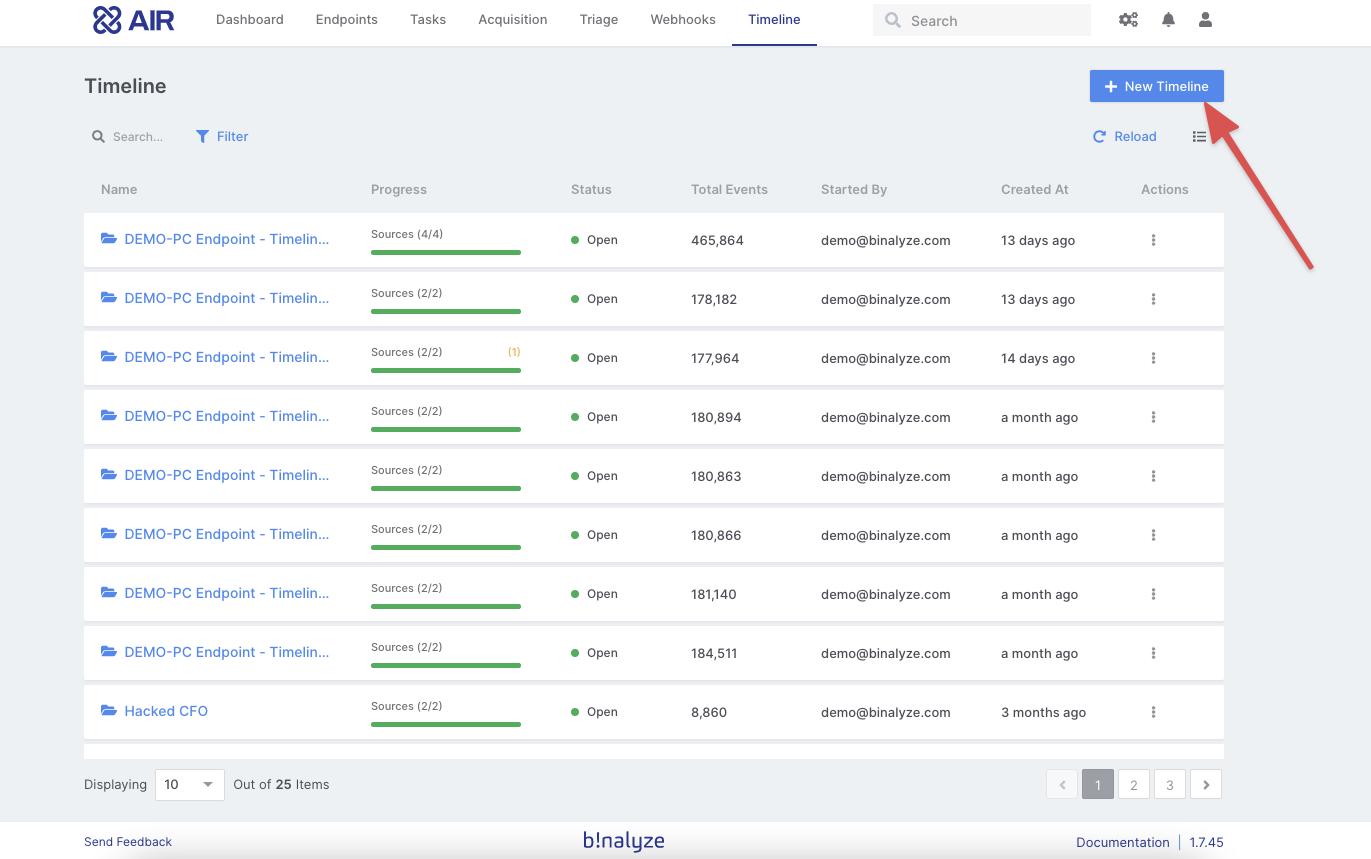
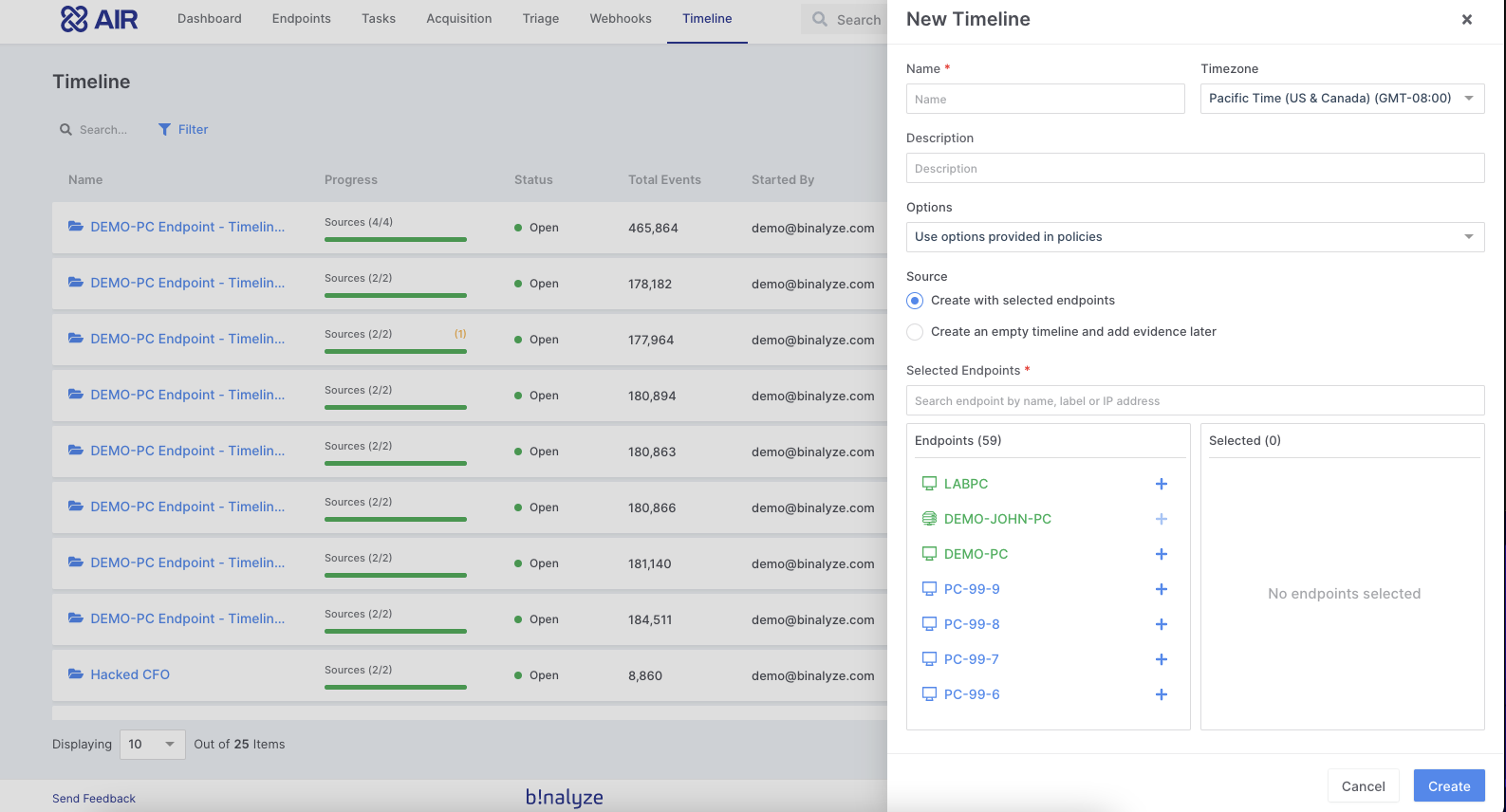
We will provide a unique name for this investigation and select a time zone so all events that AIR collects from these endpoints will align and normalize to the selected timezone. In the following step, we will choose a number of endpoints that we want to extract events from and click on “Create.”
By clicking create, you immediately assign a task to these endpoints to collect all relevant events and import them in a unified timeline. In around three to five minutes, the entire created timeline will appear in your AIR dashboard.
The great thing about the timeline feature is that it is collaborative so that multiple investigators can work on the same timeline simultaneously. Whenever they flag an event, it will be immediately visible to the other investigators.
All flagged events will appear in the flag section, which proves as a handy feature in the reporting phase.
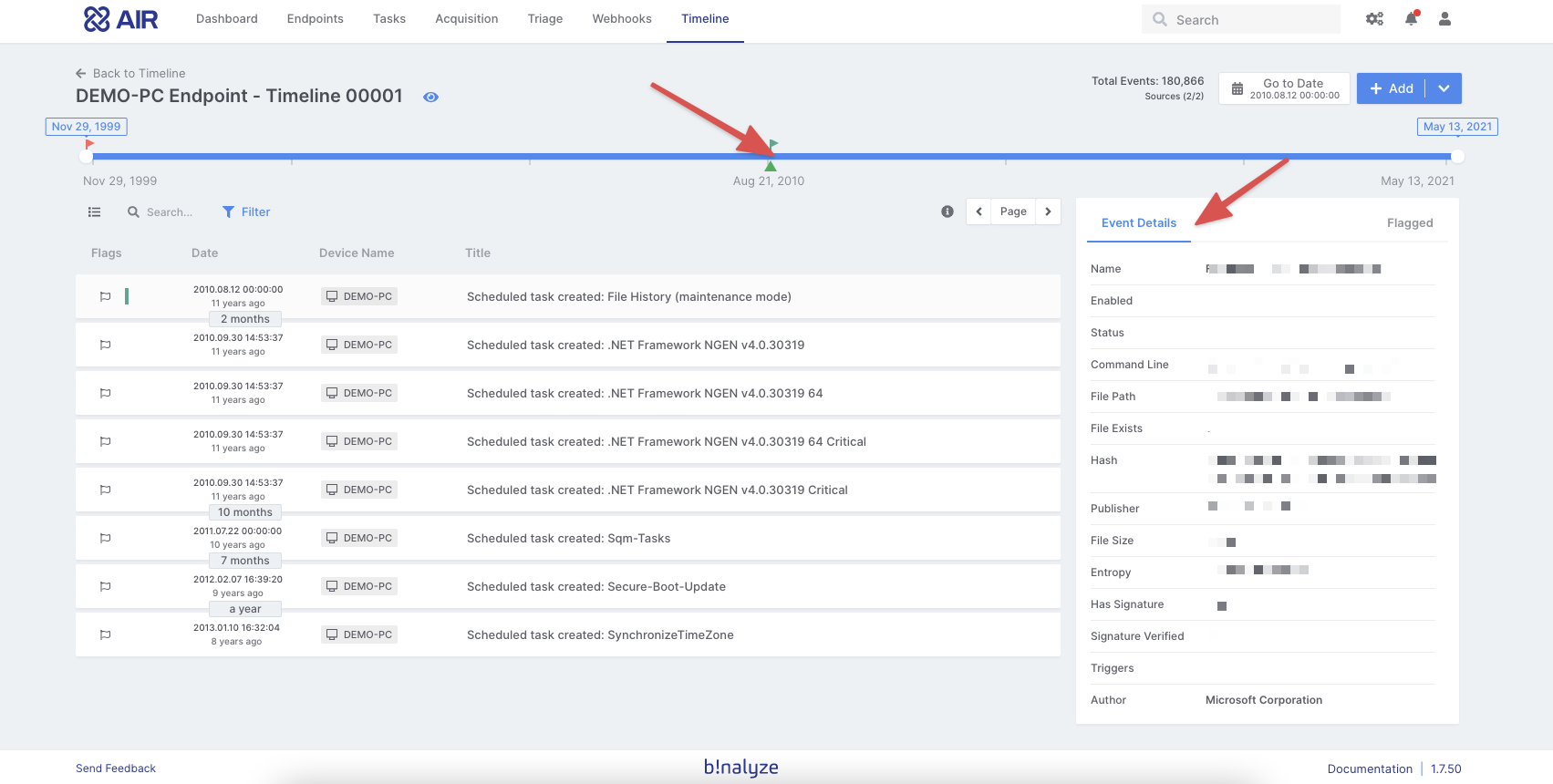
Suppose you would like to enrich this timeline further by adding other endpoints. You can do that easily by clicking on the “Endpoint” button and selecting needed endpoints from the available list.
With the latest AIR version, we have extended this capability by adding support for custom CSV files. So now, we will enrich this timeline by using this new capability. We will add a CSV file and import all the events from the file into the timeline in just four steps.
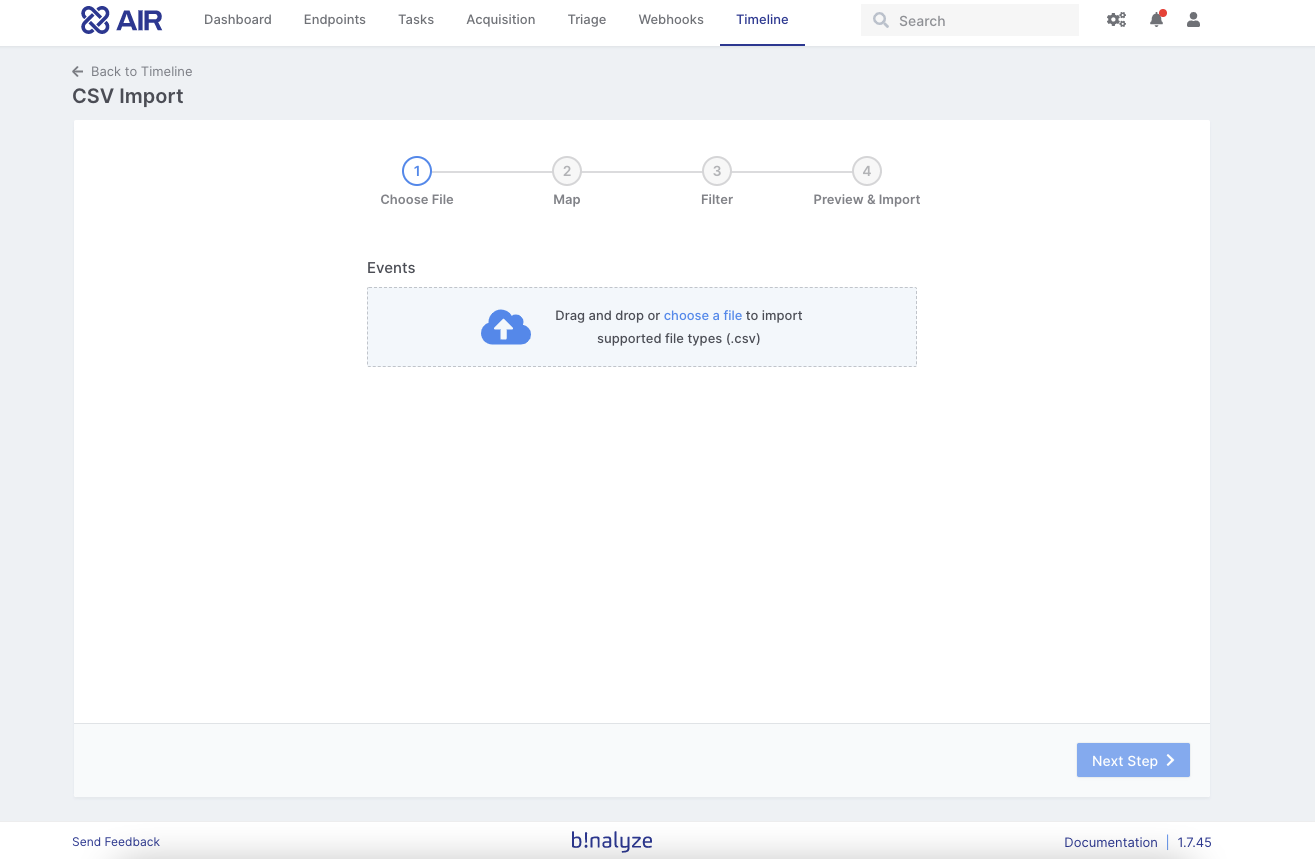
In the first stage, AIR shows a preview of the file format. So, when you click “Next,” you need to map between the CSV columns and the timeline event properties. In the third step, optionally, you can filter your data by importing all records, by date, or by the number of records. At the final stage, you will see a preview of how the events will look when you import them into your timeline.
Once you click on “Import,” it will start processing the CSV file.
As soon as you complete importing the file, you can simply click on “Go to timeline,” and it will bring you to the enriched timeline to start investigating.
Microsoft Azure and Amazon S3 Bucket evidence repositories
With this release, we are taking our first step toward cloud platforms and introducing two major evidence repositories. Now you can store collected evidence in your Azure Storage or Amazon S3 bucket accounts. If you select Azure or Amazon evidence repositories in the acquisition settings, evidence files will be uploaded to your cloud platform after the acquisition is completed.
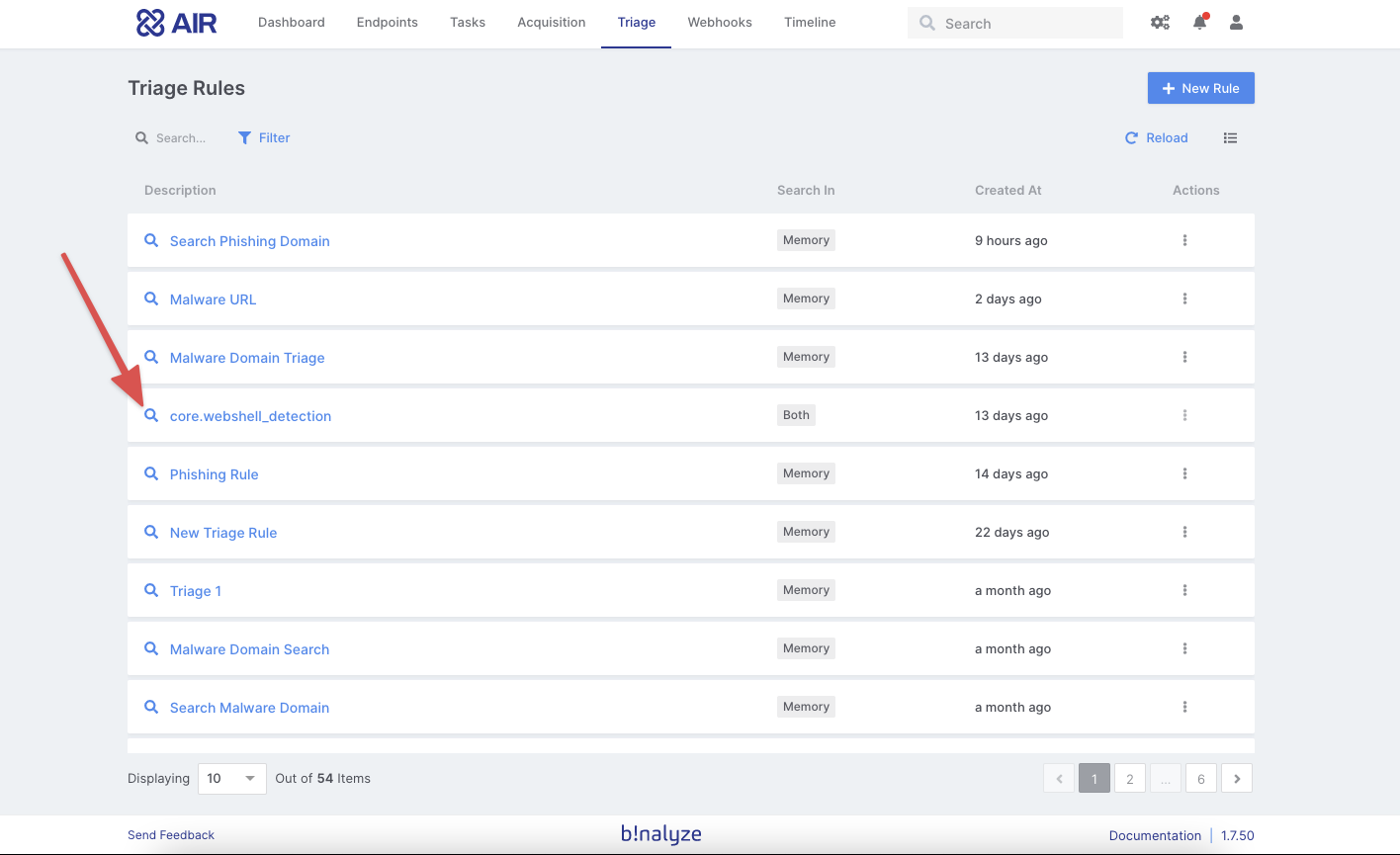
NSA web shell detection YARA rules
With this release, AIR contains out-of-the-box YARA rules to flag web shells.
Download the new version.









