2 min read
New isolation feature puts investigation under your control
![]() Amina Zilic
:
Fri, Sep 10, '21
Amina Zilic
:
Fri, Sep 10, '21

In the current cases in the DFIR world, there is a lot of confusion about which steps to take decisively and quickly at the endpoint side when something suspicious is found from the moment the investigation started, or from the moment the evidence is found.
As soon as these cases and findings begin, it is mandatory to contact the firewall or the relevant unit to close the connections of the endpoint in order to prevent lateral movement to any other location or to prevent data leakage to the outside world.
As you can see, at this point the investigators have to contact an outside body or unit to finalize this isolation process from time which takes time and it can jeopardize your investigation.
How Isolation makes this process with one single click?
Binalyze AIR now contains the Isolation feature that puts the investigation under the control of the Investigators / SOC Analyst teams by making it possible for them to disconnect any endpoint from the network with one single click immediately. In addition, since the communication with AIR continues, analysts can examine the isolated endpoint via AIR.
Main advantages:
-
AIR isolates the machine from the network with a single click immediately, a hard-to-find feature among digital forensic solutions. Normally firewalls or NAC devices are used for this purpose, with this feature we shorten the process without contacting any other product or department.
-
Isolated machines can be further examined by the DFIR investigators which lets them continue the investigation without any disturbances or interference.
How Isolation works?
-
Open endpoint dashboard on AIR and click on any endpoint. A slide window will open and you will see the “Isolation” button in the upper right corner.
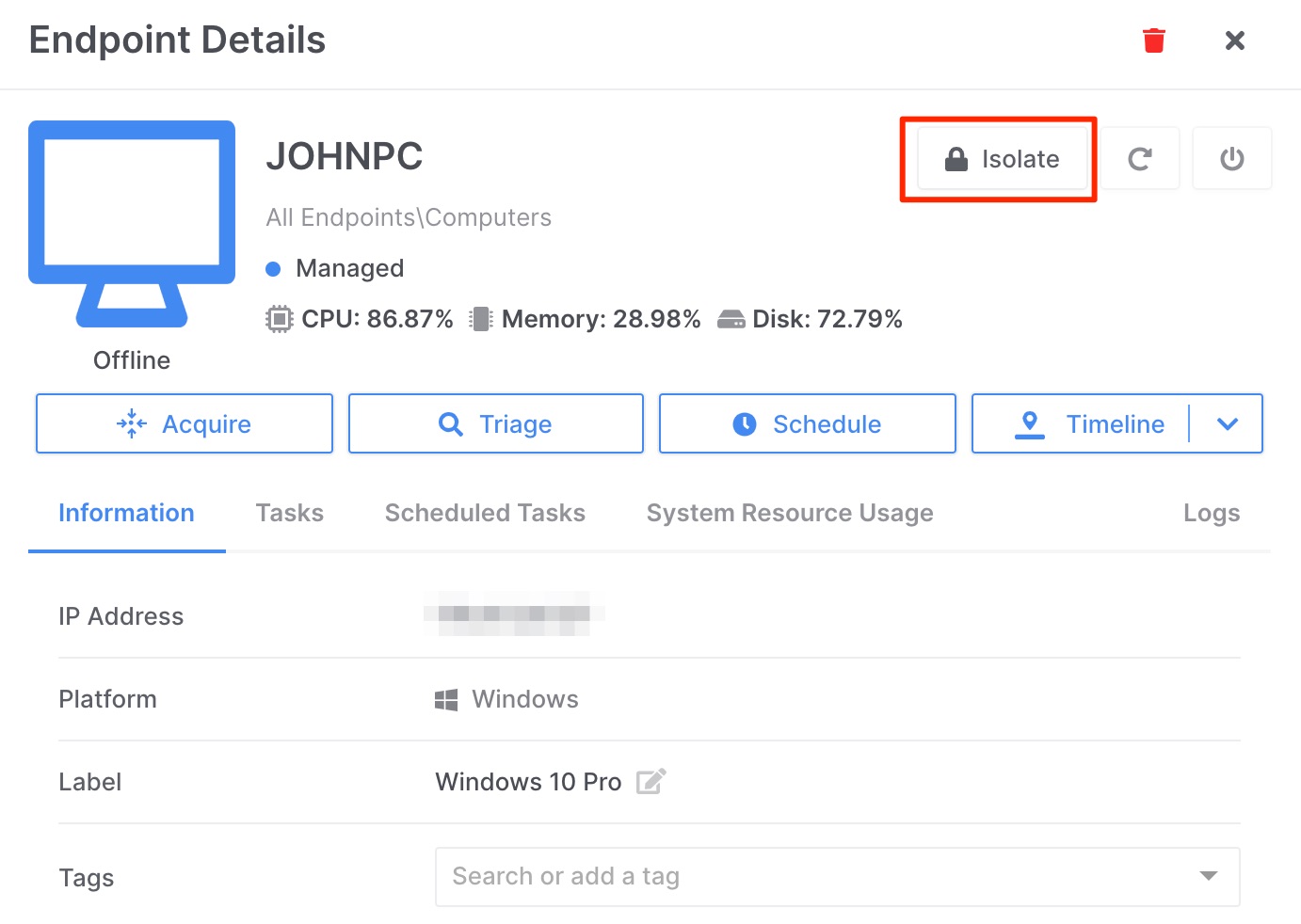
2. Once you click on that button a warning pops up to check if you are sure about the isolation task, click “Yes” and you isolated the endpoint from the network. Now you can investigate the machine without any disruptions.
Presently, the Isolation feature is available only for Windows clients but we will update you as soon as we make it cross-platform functional.
For now, we are only doing manual isolation, but in future versions, we will automate the isolation process of an endpoint in case of any findings with Drone and Triage integrations. Stay tuned for that.
LIVE EVENT ALERT
We will have a pre-release live event on Thursday (1st April) where our CEO will showcase the new features and its functionalities.
You can register on Teams.
Also, we will have a live Q&A discussion during the event so make sure to join our Discord channel.
Make sure to check out our other features in this upcoming release on our blog.









